- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Conditional Access native iOS mail app works - but not if manually configured or if mail already set
Conditional Access native iOS mail app works - but not if manually configured or if mail already set
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 01 2019 08:35 AM
Hello
When I create CA Policies for iOS, (All iOS devices on iOS 11+)
Scenario: Client has existing iPhone's already in use - 90% use native iOS App - We want to force these devices into MDM Enrollment (via Intune)
I am essentially using this guide to set CA policies : https://www.easycloud365.com/blog/how-to-block-native-apple-mail-app-ios-with-conditional-access-par...
So far this works if I am setting up a new device, it will prompt me to sign into organisation and require me to enroll the device etc. - Works as it says on the tin. However....
A couple of things are apparent:
- When I setup a new phone - i click on the iOS mail app > Add Account > Exchange > type in username(email address) & password and I receive a prompt:
"Sign in to your "username@tenant.onmicrosoft.com"Exchange account using Microsoft?"
1) Configure Manually
2) Sign In
If I select "Sign In" then no drama - I go through the enrollment process normally
If I select can also select "Set up manually" and then proceed to set up the device using- email address: (username@tenant.onmicrosoft.com)
- username & Password (username@tenant.onmicrosoft.com)
- Server: outlook.office365.com
I am then able to get mail flowing in the native iOS mail app without the phone being required to go into MDM or adhere to the Conditional Access Policies and Compliance policies
Next is that any phones already with their mail configured in the default iOS App
- Nothing happens - you just continue to use the phone as normal and it does not block mail on the native iOS app sop that the users are forced to enroll their devices.
I hope this all makes some sense - and looking for any guidance. i.e. perhaps I need to block via PowerShell?
https://docs.microsoft.com/en-us/exchange/clients-and-mobile-in-exchange-online/outlook-for-ios-and-...
Thanks for your time reading this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 12:39 AM
@Adam Weldon-Ming Nature of Conditional Access is that it actually works only with Modern Auth. So, in your case you need to have 2 policies.
- One to block Legacy authentication.
- And one more following guide you used.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 01:15 AM
@Adam Weldon-Ming
What does the sign-inn log in Azure AD say, choose to show the client app column?
Do you also block legacy authentication?
You could also add an App Protection Policy to make sure also nonregistered BYOD devices are forced to use Outlook, but this shouldn't be necessary for access control if you don't also want better management of company data.
JT
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 07:00 AM - edited Jul 02 2019 07:15 AM
thanks for your time going through my problem @jenstf & @Alexander Vanyurikhin
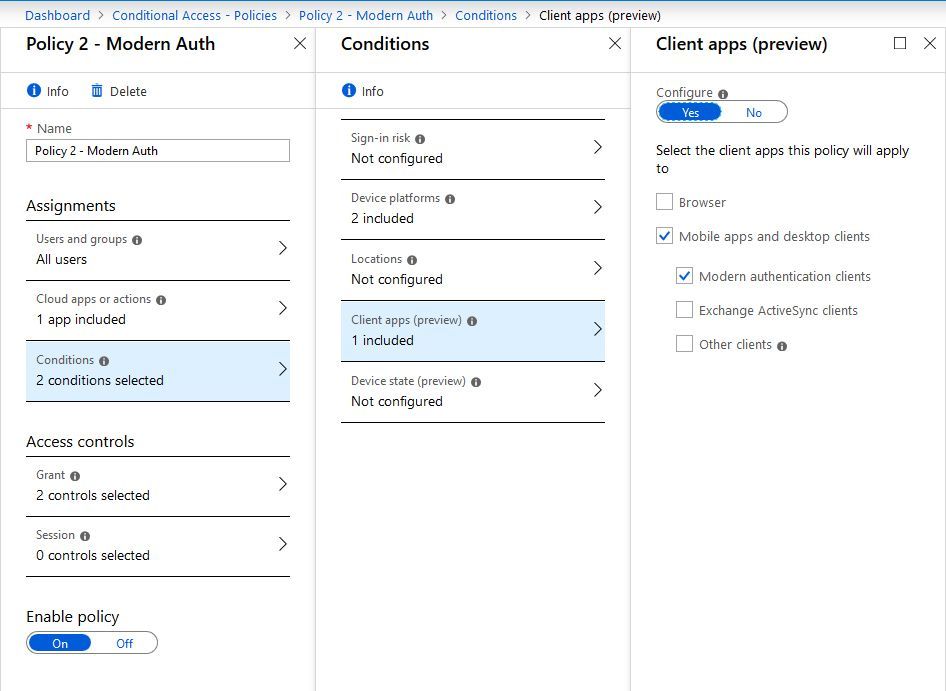
I have created two policies
1 Policy for Legacy and Native iOS App
1 Policy for Modern Authentication
Both Require device to be marked as compliant & Requires approved client app
But I am still able to get mail to flow in once configuring manually.
(unless while I am changing policies it may take some time before it takes affect)
These are my policies
Only applying to Exchange Online App
Only applying to iOS and Android devices.
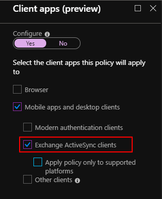
[First is for native iOS / Legacy Auth]

[Second below is for Modern Auth - If setting up via outlook app this works fine and enrolls the device problem I think is the first policy above]

With the above set - I was able to manually configure mail on iOS device by adding the server: outlook.office365.com
I have turned policies on and off for the first one so maybe it will rake some time to apply(?)
I checked Sign-Ins on Azure AD monitoring but not showing anything with signing if I configure manually -
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 11:11 AM - edited Jul 02 2019 11:32 AM
SolutionI would monitor the sign-in log and look for logins from other client and active sync (unsupported) before doing this in production.
JT
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 03:02 PM
@jenstf- Many thanks - this has helped clarify some things in my head
1 last question on this if that's ok:
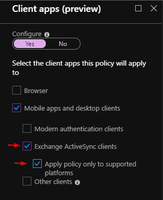
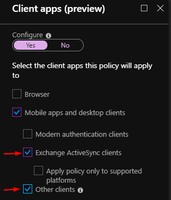
It's also recommended to make one policy for active sync and one for other clients.
Would you essential be creating 3 for this? i.e.
Or would you always combine, say, Exchange ActiveSync + Apply policy only to supported platforms in one policy?
Adam
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 10:46 PM
@Adam Weldon-Ming In my policies I don't use "Apply policy only to supported platforms". The documentation isn't clear on what that choice actually is good for. i.e. Linux isn't a supported platform and will then bypass this policy.
I have one policy with "Exchange active sync clients" and one for "other clients".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2019 08:44 AM
Thanks a lot @jenstf
I've separated them out into 2 policies and this has forced my test iPhone's to get the message to enroll the phones. Rather than blocking the e-mail entirely and I cannot configure manually any more.
My main problem here was patience :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 17 2019 03:49 AM
@Adam Weldon-Ming could you summarize and provide us with the final conditional access policies?
I have the same problem. I push an E-Mail profile (via the Device Configuration Profile) to the devices. However, I want the native Mail app to be blocked.
Best regards,
Labinot
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 01 2019 02:55 AM
Hey, sorry for the long wait - best thing I think to do here now is to use the :
"Baseline policy: Block Legacy authentication (Preview)"
Enable this Policy - However, there are no exceptions for this so therefore it would apply to all users, global admins etc.
If you need to have it more granular you can do a couple thinfs
1 - Build a custom Conditional Access Policy that BLOCKS legacy authentication.
- Create a no CA policy - Include All apps (or ones you want)
- Under: Conditions > Client Apps > Select YES
- Select: Mobile Apps and Desktop Clients > Other (Choose Exchange ActiveSync if you want to block native mail apps.
- Then on Access Control > Grant: Select Block Access
- Save and Enable.
2 - Create a authentication policy: https://docs.microsoft.com/en-us/exchange/clients-and-mobile-in-exchange-online/disable-basic-authen...
CA Is more recommended though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 12 2020 04:07 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 12 2020 08:57 AM
If you have AAD P1, you should create your own conditional access policies
Otherwise, use security defaults https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/concept-fundamentals-security-d...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 13 2020 01:34 AM
@Thijs Lecomte Thanks, I'm also looking for the solution for following
Scenario: Client has existing iPhone's already in use - 90% use native iOS App - We want to force these devices into MDM Enrollment (via Intune) and forced to use MS Outlook
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 02 2021 09:48 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 03 2021 02:47 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 03 2021 04:25 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 04 2021 11:55 PM
Or an Exchange level: https://docs.microsoft.com/en-us/exchange/clients-and-mobile-in-exchange-online/disable-basic-authen...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 08 2021 12:47 AM
Yup was able to do it via Conditional Access already. Had issues mainly with my patience haha. Took it more than a day till my expected outcome were observed.
Thank you!
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 11:11 AM - edited Jul 02 2019 11:32 AM
SolutionI would monitor the sign-in log and look for logins from other client and active sync (unsupported) before doing this in production.
JT