- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2019 11:35 AM
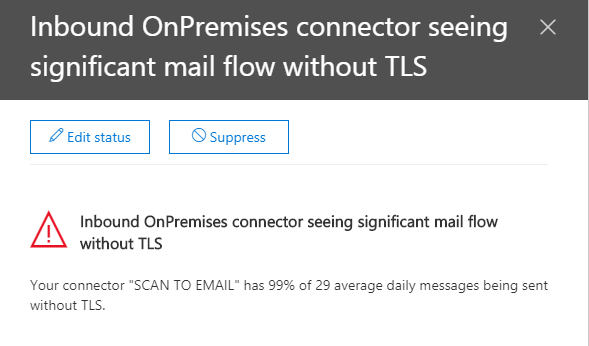
I am getting some messages in my Office 365 about Mail without TLS. Is there any concerns here? Do I need to make any changes?
- Labels:
-
Office 365
-
Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2019 12:49 PM
Most e-mail servers have opportunistic TLS on so it will try TLS first then do no TLS as a backup so there could be an issue with the TLS connection but my gut says that one of your domains you are using just has it off for some reason.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2019 01:06 PM
Hi @Chris Webb
Is TLS something I can turn on in Office 365 or does that have to be done with my Domain Registrar?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2019 01:26 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2019 01:36 PM
Here is the Connector I am using that is getting the TLS warnings.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 24 2019 12:57 AM
Switch to using the other option, "By verifying that the subject name on the certificate that the sending server uses to authenticate with Office 365 matches this domain name". Details for example here: https://docs.microsoft.com/en-us/exchange/mail-flow-best-practices/use-connectors-to-configure-mail-...
You can also toggle the RequireTls parameter.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 31 2019 09:22 AM
Tim
I have been wondering the same thing but none of the answers here make sense to me.
In our case, and it looks like yours as well, the connector exists to allow printers, scanners, software, and other devices to send email using an unauthenticated smtp connection to Office 365. What appears to me to be happening is that some of those devices are sending email without using TLS 1.2. I assume that is either because the devices are unable to (Too old or need updates) or they are able too but TLS 1.2 is not enabled on those devices.
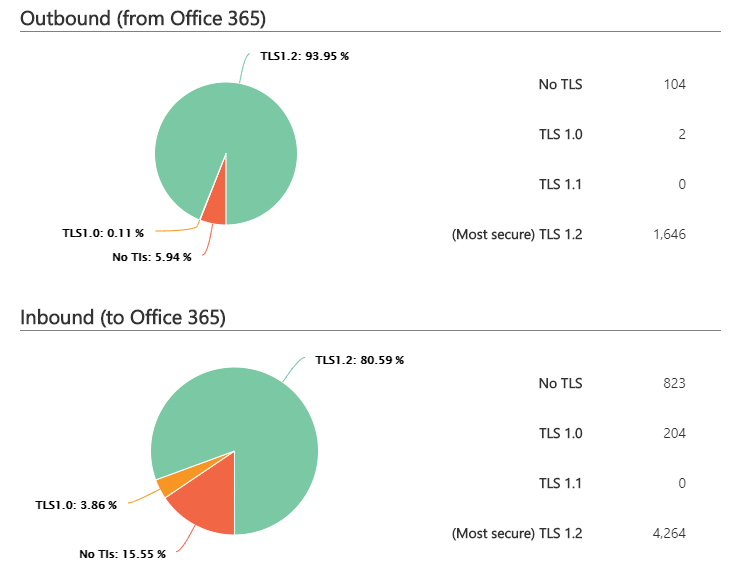
I thought that the solution was to find those devices and update them and enable TLS 1.2 if possible. However, I haven't been able to find a way to identify where the emails are coming from. In your case if you could drill down on the 104 NO TLS messages to see where they come from you could quickly determine whether they could be updated to send TLS 1.2 and get rid of the warnings. If someone knows how to do that please tell.
Or maybe I have completely misunderstood what is going on ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 31 2019 09:25 AM
@John Twohig @Vasil Michev @Chris Webb
Hi John,
I believe the devices that send may be too old. Does anyone know how to "drill down" on the 104 NO TLS messages to see where they are coming from so I can determine if it is possible to turn on TLS 1.2.
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 22 2019 10:40 AM
I know this is old but there is a report that shows the devices. I ran it this morning and it showed how many emails each printer/MFD sent last week.
In the comments near the bottom there is one from @Shawn Housler that shows how to get the report.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 22 2019 11:09 AM
So I found the 1 email address in my account that is still apparently using TLS 1.0. It is an email we use for automated billing. How can I find out what device it is sending through using TLS 1.0, so I can upgrade that device to TLS 1.2? Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 22 2019 02:22 PM
Is it perhaps an application and not a device? I have a couple of applications that send automated emails. You may have to contact whoever wrote the software to see when they will upgrade it.
I heard from one software vendor who got back to me with a link to an update. I did the update so I will check the TLS reports next week and hopefully that application will be gone.
