- Home
- Security, Compliance, and Identity
- Microsoft Entra
- New Blog Post | Upgrade your tenant restrictions to v2
New Blog Post | Upgrade your tenant restrictions to v2
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 21 2024 02:28 PM
In a previous blog in the Data Exfiltration series, we discussed different types of tenant restrictions policy. In this blog, we’ll discuss migrating from tenant restrictions v1 to authentication plane tenant restrictions v2. In future blogs, we’ll discuss migrating to Universal tenant restrictions v2.
Tenant restrictions are a vital tool to help prevent data exfiltration from unauthorized access to external Microsoft Entra ID tenants and consumer Microsoft accounts. Tenant restrictions v1 lets you create an allow list of tenant IDs and Microsoft sign-in endpoints to ensure that users access external tenants that your organization authorizes. While tenant restrictions v1 served well for many years, tenant restrictions v2 offers more granularity and easier policy management with no additional licensing requirements.
Tenant restrictions v2 has several benefits over tenant restrictions v1. For example, admins can:
- Update the policy from the Microsoft Entra portal rather than from each network proxy. There’s no need to update the header.
- Increase the size limitations of your maximum proxy header length. There’s no limit to the number of partners you can add with tenant restrictions v2.
- Selectively indicate which user groups access which apps in external tenants rather than allowing entire tenants for all identities.
In this blog post, I’ll explain the differences between how the two tenant restriction types work independently from, and in tandem with, cross-tenant access settings (outbound) to highlight the benefits of upgrading to tenant restrictions v2.
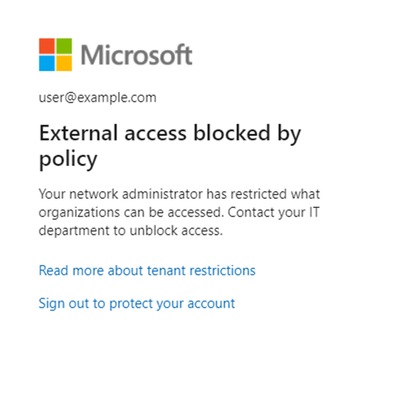
Getting started with tenant restrictions
Tenant restrictions require routing all user authentication traffic through a proxy. Typically, the proxy is the on-premises network egress, but it can also be a cloud-based proxy. The proxy injects a header indicating that an allow list of destinations is enforced on the traffic, regardless of the originating device or network location. In tenant restrictions v1, the destination allow list is in the header. In tenant restrictions v2, the header has a tenant ID and policy ID. Traffic arrives at Microsoft Entra ID, which reads the header and enforces the policy. If the traffic destination isn’t in the allow list, the user receives an error message.
Read the full story here: Upgrade your tenant restrictions to v2
- Labels:
-
Identity Management