First published on CloudBlogs on Jun 27, 2017
 We encourage you to:
We encourage you to:
Granting and restricting access to data with Azure Active Directory
This blog post is the latest in our series about how EMS can support you in your journey to EU GDPR compliance. We last looked at how Azure Information Protection helps keep your data protected, whether it’s stored on-premises or in the cloud. Today, I’m going to talk about how you can protect access to your data using Azure Active Directory , Microsoft’s Identity and Access Management solution. Hackers work hard to steal credentials. Stealing credentials is the easiest way to sneak into a network undetected, which is why controlling and protecting identities needs to be your first line of defense. Considering the majority of cybersecurity attacks traced back to lost, weak or compromised user credentials, it’s clear you need more security than passwords will ever give you. Below are some of the great features in Azure AD that put stronger locks on your front door so you only let in people you trust.Set conditions to protect access
Protecting data starts with securing identities and controlling access and Azure Active Directory helps you protect your organization beginning at the front door. But one critical aspect of good security is that it’s nearly invisible to good users. Excessive friction inhibits productivity, and good users will find ways to work around things that block their productivity, creating risk. While you could challenge every user at every login with multi-factor authentication (MFA), ideally you’d maximize productivity by allowing good users to get their work done with few interruptions, all while stopping the bad guys in their tracks. Azure AD Conditional Access allows you to do just that. Previously, you might’ve had to say, “No access from off the corporate network” or, “No access from a personal device,” but Azure AD Conditional Access allows you to basically say, “Yes, but there are conditions.” The group that users belong to, the location from which they’re accessing corporate resources, the health of their device, the sign-in, and the user risk are conditions to consider when you’re deciding whether you’d like to block access, grant access, or challenge the user with MFA.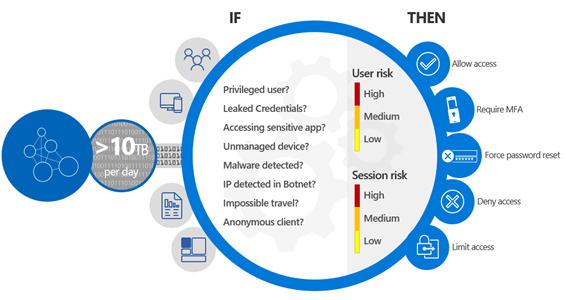
Evaluate risk before granting access
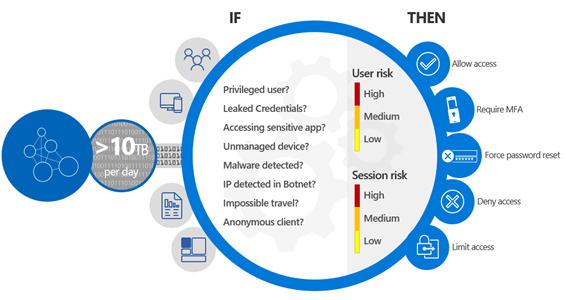
Azure AD Identity Protection lets you define conditional access policies based on risk calculation enhanced by Microsoft’s Intelligent Security Graph – the cumulative intelligence we collect from our products, services, internal teams, and external sources. Based on this data, we calculate the risk of an individual user or a sign-in attempt. Azure AD Identity Protection will notify you if it detects suspicious behavior, help you investigate, and take automated action like blocking a sign-in or triggering a password reset.Give people the right level of permissions, only when they need it
The higher the user’s privileges, the bigger the potential damage if their account gets compromised. Azure AD Privileged Identity Management helps you bring hygiene to your privileged accounts by providing visibility into admin accounts so you can monitor their activity. With this visibility you can revoke permanent privileged access from people who don’t need it all the time and give just-in-time privileged access temporarily.Define special controls for groups and their members
The Dynamic Groups feature automatically adds or removes members from a group based on user attributes that you define. You can use these groups to provide access to applications or cloud resources like SharePoint sites.Get information on users, groups, and managed applications
Azure AD reporting gives you insight into the detailed activities happening in your environment. View sign-in activities for individual users and understand which applications people are using and who’s using them. Audit logs will show you a list of privileged actions, such as role creation, password resets, and changes to groups, as well as show you applications that have been added, updated, or removed. We encourage you to:
We encourage you to:
- Learn more about Azure Active Directory by reading through our technical documentation
- Download our whitepaper to learn how EMS supports your GDPR compliance journey
- Explore these capabilities with a free EMS trial
- Learn more about Microsoft’s commitment to the GDPR and how we can help you on your journey to compliance on Microsoft's GDPR website
Published Sep 08, 2018
Version 1.0MicrosoftSecurityandComplianceTeam
Iron Contributor
Joined September 05, 2018
Microsoft Security Community Blog
Follow this blog board to get notified when there's new activity