- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Anomalous Token & activity from Microsoft
Anomalous Token & activity from Microsoft
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 13 2022 08:58 PM
Hi,
I am trying to understand the following activity.
I have had a few users in my organization flagged as a "Risky User" due to an anomalous token. This is normally supposed to flag if a users session token is stolen and replayed.
Upon investigating the flagged sign ins, the IP addresses used for these are within Microsoft's Exchange Online IP range. Office 365 URLs and IP address ranges - Microsoft 365 Enterprise | Microsoft Docs
52.96.172.x
It is also common to see these as non-interactive sign ins.
I am trying to understand why there would be a sign in from a Microsoft Exchange Online IP address to one of our accounts that would be attempting to use a token from a users client as per the error message reported?
Is there a service running in Exchange Online I am not aware of that signs in on the users behalf? Why would it be using a token granted to a users device?
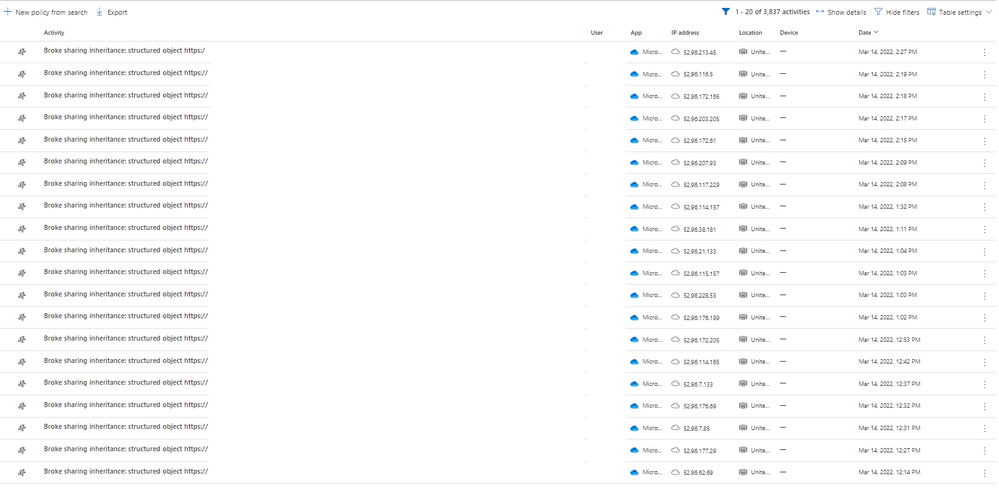
I have also noticed consistent activity from these IP addresses in Cloud App Security.
Any help or clarification would be greatly appreciated!
Kind Regards,
Jacques
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 10 2022 06:51 AM