- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Re: Azure federated users unable to login to Windows 10
Azure federated users unable to login to Windows 10
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Jul 10 2017
11:14 PM
- last edited on
Jan 14 2022
05:31 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 10 2017
11:14 PM
- last edited on
Jan 14 2022
05:31 PM
by
TechCommunityAP
We have setup our on-premise AD with ADFS to enable login for Active Directory users to Azure AD. This configuration is done like this articel http://www.ruudborst.nl/multi-tenant-azure-federation-without-dirsync-aadsync-aadconnect-fim/
This setup works for Passive and Active logons, the only problem is that users are not able to logon to Windows 10 computer with this configuration. If the type there username and password there password always seems to be wrong. (Checked multple times).
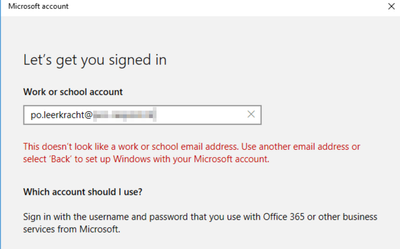
Trying to join the Windows 10 computer will fail for this users with the following message "...This isn't an school or work account...."
Is there something in Azure AD that we need to activate to get this working?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 10 2017 11:31 PM
Hi Bjorn,
Have you setup Azure AD Join ? Here How https://docs.microsoft.com/en-us/azure/active-directory/active-directory-azureadjoin-setup
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 11 2017 01:14 AM
Nuno,
Azure AD join is setup, in fact when the domain is set to managed instead of federated, users are able to join there device and logon. But for bussiness requirements it's necesarry to put the domain in federated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 11 2017 12:04 PM
Ok, if is a business requirement I cannot see the solution, maybe in future that will be possible.
After you set up Azure AD Join for your users, they can connect to Azure AD through their corporate or personal devices.+
Following are the three scenarios you can use to enable your users to set up Azure AD Join:+
- Users join a company-owned device directly to Azure AD.
- Users domain-join a company-owned device to the on-premises Active Directory and then extend the device to Azure AD.
- Users add work or school accounts to Windows on a personal device
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 12 2017 07:00 AM
Both managed and federated configurations should be able to authenticate to both cloud and on-prem upon signing to Windows, both domain joined (registered with Azure AD) and Azure AD joined devices.
Signing in to Windows 10 devices require one of the WS-trust username/mixed (13 or 2005) end-points in AD FS to be enabled. Can you check whether one of these end-points are enabled?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 13 2017 07:16 AM - edited Jul 14 2017 06:43 AM
Both the endpoints are enabled. even on the adfs proxies.
I've did some network sniffing during Azure AD Join, and this is what's happening.
1 - http://login.microsoftonline.com:443
2 - https://login.microsoftonline.com/webapp/UnifiedEnrollment/3
3 - http://secure.aadcdn.microsoftonline-p.com:443
4 - https://login.microsoftonline.com/WebApp/CloudDomainJoin/8
5 - https://login.microsoftonline.com/common/.well-known/openid-configuration
6 - https://login.microsoftonline.com/common/oauth2/authorize?client_id=1b89ed98-a469-4536-ade2-f981bc1d...
7 - http://secure.aadcdn.microsoftonline-p.com:443
8 - https://login.microsoftonline.com/common/GetCredentialType
After these step the following error is displayed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 20 2017 06:48 AM
have you enable in your ADFS on-prem a service endpoint ?
adfs/services/trust/13/windowstransport
your computer windows 10 is integrated as Azure AD join or in your domain on-prem ?
Do you use a proxy in your enterprise for going out to microsoft ?