- Home
- Security, Compliance, and Identity
- Microsoft Defender for Endpoint
- Re: Feature request: Block readaccess to Windows Defender exclusions
Feature request: Block readaccess to Windows Defender exclusions
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 09 2020 01:10 PM - edited Jul 09 2020 01:16 PM
Hello Defender ATP Team,
I have already submitted this request via the Feedbackhub, but I think it is important enough to request it here.
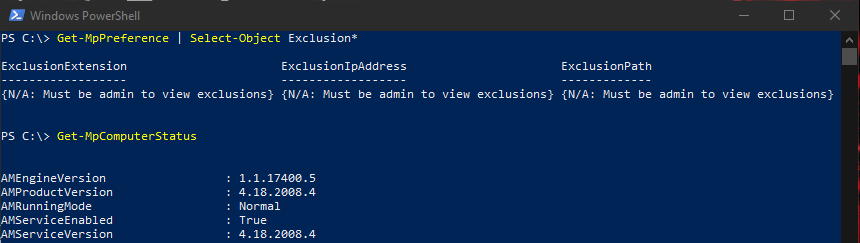
A user without administrative right can't add exclusions to Windows Defender, however, he can read the exclusions:
- via Powershellcmdlet "Get-MpPreference"
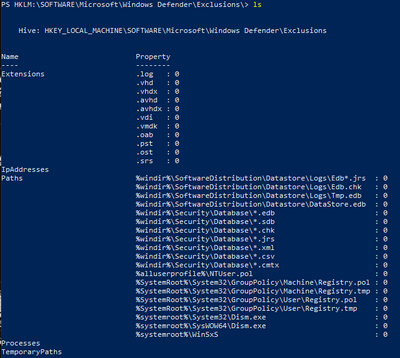
- via registry
An attacker which manages to get his code running on a machine with userrights could check for folderexclusions with writeaccess and place its payload there.
I created a (verry quick and verry dirty) sample powershellscript which will place a Base64 encoded EICAR string in each directory where the BUILDIN users have writeaccess.
I would appreciate an option to disable the readaccess to Windows Defender exclusions, at least for normal users without administrative rights.
Best regards
Stefan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 15 2020 08:25 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 24 2020 12:08 PM
A quick status from my side about this topic. Someone at Microsoft listened to this post or my Feedbackhub request:
Starting with Windows Defender Platform Version 4.18.2008.4, only admins can view the exclusions when using the Powershell cmdlet "Get-MpPreference":
Sadly, the access to the exclusions via registry (with userrights) is still possible:
The access to the ASR exclusions is also still possible via powershell and registry.
So if you are the one from Microsoft who read my post: it would be great to get this things fixed with the next platform version.
Cheers,
Stefan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 11 2020 06:27 PM
Just a question when you say that on 4.18.2008.4 only admins can see, do you know if it is also hidden from Defender UI (interface)? Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 13 2020 04:25 AM
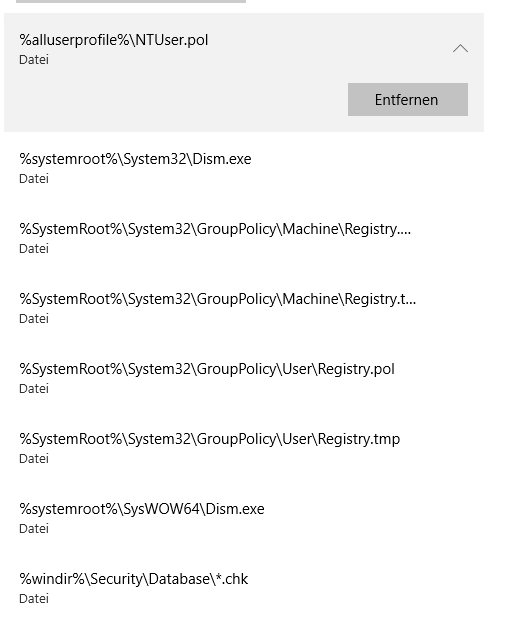
@Thiago_Mota Unfortunately, no. The "normal" User without administrative rights can still see exclusion in the Securitycenter:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 14 2020 03:00 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 21 2022 03:01 AM
There is an option now, called in the GPO "HideExclusionsFromLocalAdmins";
But, I'm challenged now why we cannot Disable of use of the Exclusions for users also with Administrative rights, I think this will be better. And could be interesting to deploy an Intune profile, that simply locks any Exclusions to be added, viewed, accessed, only Intune service/tenant admins can.