- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Forefront Endpoint Protection 2010 Group Policy Tool is unable to import policy files exported from System Center 2...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Symptoms:
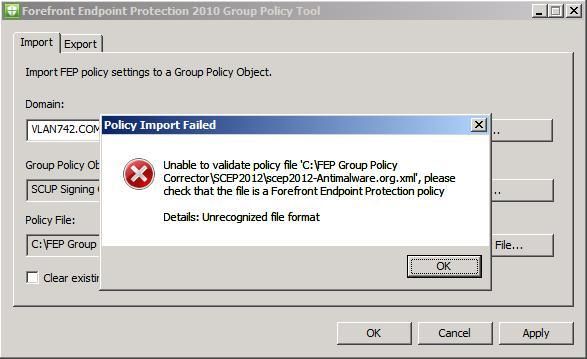
When you use the Forefront Endpoint Protection (FEP) 2010 Group Policy Tool to import a policy file that was exported from System Center 2012 Endpoint Protection, it will fail with a screenshot similar to the following:
Cause:
The XML namespace is missing and a couple of registry value types have changed in System Center 2012 Endpoint Protection, which results in the error.
Resolution:
-
Perform the following changes manually
- Add "xmlns=" http://forefront.microsoft.com/FEP/2010/01/PolicyData "" in the "SecurityPolicy" section of the policy file.
- Open the policy file, in the “AddKey Name="SOFTWAREPoliciesMicrosoftMicrosoft AntimalwareSignature Updates"” section, replace “FallbackOrder” type “ REG_DWORD ” with “ REG_SZ ”.
- Open the policy file, in the “AddKey Name="SOFTWAREPoliciesMicrosoftMicrosoft AntimalwareSignature Updates"” section, replace “DefinitionUpdateFileSharesSources” type “ REG_DWORD ” with “ REG_SZ ”.
-
Automate the changes by using the script in the Script section
You can use the script in the Script section to make the changes to the policy file. You can also write a Java script tool to automate the script. For example, you can name the script in the Script section FepGPFileCorrector.js, and then use a command such as the following:
cscript.exe FepGPFileCorrector.js <originpolicyfile>.xml
Where, originpolicyfile is the exported System Center 2012 Endpoint Protection policy file. Currently, the following is supported:
- Full path of local xml file. For example, c:testoutput.xml
- Full path of network share file. For example, \atc-dist-01testoutput.xml
- File located under the folder that script tool is running.
The target/output policy file is named Converted-<originpolicyfile>.xml .
References:
The Forefront Endpoint Protection Group Policy Tool is used to convert policy settings contained in configured FEP policies to the format that is used by Group Policy. This tool can be obtained from the Microsoft Download Center ( http://go.microsoft.com/fwlink/?LinkId=207729 ) as part of the FEP 2010 Group Policy Tools download package.
System Center 2012 Endpoint Protection provides several default policy template files that you can find in subfolder AdminConsoleXmlStorageEPTemplates of site server installation directory. You can import the policy template files by using FEP 2010 Forefront Endpoint Protection Group Policy Tool by default.
Script:
@set @debug = false //****************************************************************************** // // Constants // //****************************************************************************** var c_sSecurityPolicy = "SecurityPolicy"; var c_sPolicySection = "PolicySection"; var c_sLocalGroupPolicySettings = "LocalGroupPolicySettings"; var c_sXmlns = "xmlns"; var c_sNameSpace = "http://forefront.microsoft.com/FEP/2010/01/PolicyData"; var c_sAddKey = "AddKey"; var c_sAddValue = "AddValue"; var c_sName = "Name"; var c_sType = "Type"; var c_sDisabled = "Disabled"; var c_sFallbackOrder = "FallbackOrder"; var c_sDefinitionUpdateFileShareSources = "DefinitionUpdateFileSharesSources"; var c_sDWord = "REG_DWORD"; var c_sSZ = "REG_SZ"; var c_sHelp = "cscript.exe FepGPFileCorrector.js <originpolicyfile> rn" + "rn" + "originpolicyfile Original exported SCEp2012 policy file.rn" //****************************************************************************** // // Globals // //****************************************************************************** var g_fso = null; // Scripting.FileSystemObject var g_xmlSource = null; // Source XML document var g_xmlTarget = null; // Target XML document var g_shell = null; var g_environment = null; var g_sScriptDir = null; // cscript.exe running directory var g_sOriginPolicyFile = null; // Original FEP2012 exported policy file var g_sOriginFileName = null; // Original FEP2012 exported policy file name var g_sOriginPolicyPath = null; // The directory hosting original FEP2012 exported policy file //****************************************************************************** // // GetAttribute // //****************************************************************************** function GetAttribute(oNode, sAttrib, bAllowNull) { var attrib = oNode.attributes.getNamedItem(sAttrib); if (attrib != null) { return attrib.text; } else if (bAllowNull) { return null; } return null; } // Validate script host version if (Number(WScript.Version) < 5.6) { WScript.Echo( "This script requires Windows Script Host v5.6 or later. " + "Go to http://www.microsoft.com/scripting for download" ); WScript.Quit(1); } if (WScript.FullName.toLowerCase().indexOf("cscript.exe") < 0) { WScript.Echo( "This script can only be executed with Cscript." ); WScript.Quit(1); } if ((WScript.Arguments.length < 1) || (WScript.Arguments(0) == "/?")) { WScript.Echo(c_sHelp); WScript.Quit(1); } // Initialize g_fso = new ActiveXObject("Scripting.FileSystemObject"); g_shell = new ActiveXObject("WScript.Shell"); g_environment = g_shell.Environment("Process"); g_sScriptDir = g_fso.GetParentFolderName(WScript.ScriptFullName); g_sOriginPolicyFile = String(WScript.Arguments(0)); // If g_sOriginPolicyFile has not path if ((g_sOriginPolicyFile.indexOf(":") > 0) && (g_sOriginPolicyFile.charAt(0) != ".")) { g_sOriginPolicyPath = g_sOriginPolicyFile.substr(0, g_sOriginPolicyFile.lastIndexOf("\")); g_sOriginFileName = g_sOriginPolicyFile.substr(g_sOriginPolicyFile.lastIndexOf("\") + 1); } else if ((g_sOriginPolicyFile.charAt(0) == "\") && (g_sOriginPolicyFile.charAt(1) == "\")) { g_sOriginPolicyPath = g_sOriginPolicyFile.substr(0, g_sOriginPolicyFile.lastIndexOf("\")); g_sOriginFileName = g_sOriginPolicyFile.substr(g_sOriginPolicyFile.lastIndexOf("\") + 1); } else { g_sOriginPolicyPath = g_sScriptDir; g_sOriginFileName = g_sOriginPolicyFile; } if (!g_fso.FileExists(g_sOriginPolicyFile)) { WScript.Echo("XML file " + g_sOriginPolicyFile + " does not exist!"); throw new Error(1, "The XML file does not exist!"); } //var oFile = g_fso.GetFile(g_sOriginPolicyFile); //oFile.Attributes = oFile.Attributes & (~1); g_xmlSource = new ActiveXObject("MSXML2.DOMDocument.6.0"); // Load original SCEP2012 exported policy file if (!g_xmlSource.load(g_sOriginPolicyFile)) { var pe = g_xmlSource.parseError; INFO( "XML load failed:n" + " Location: " + pe.line + ", " + pe.linepos + "n" + " Source: " + pe.srcText + "n" + " Reason: " + pe.reason + "n" ); throw new Error(-1, "Policy file is invalid."); } var oSrcSecurityPolicyNode; //var oRootNodes = g_xmlSource.documentElement.selectNodes(c_sSecurityPolicy); var oRootNodes = g_xmlSource.childNodes; if (!g_xmlSource.hasChildNodes()) { WScript.Echo("XML file " + g_sOriginPolicyFile + " might not need to process, exit directly."); WScript.Quit(1); } for (var iIndex = 0; iIndex < oRootNodes.length; iIndex++) { if (oRootNodes[iIndex].nodeName == c_sSecurityPolicy) { oSrcSecurityPolicyNode = oRootNodes[iIndex]; if (oSrcSecurityPolicyNode != null) { if (oSrcSecurityPolicyNode.attributes.getNamedItem(c_sXmlns) != null) { WScript.Echo("XML file " + g_sOriginPolicyFile + " might not need to process, exit directly."); WScript.Quit(1); } } break; } } g_xmlTarget = new ActiveXObject("MSXML2.DOMDocument.6.0"); var sTargetXmlFile = g_sOriginPolicyPath + "\Converted-" + g_sOriginFileName; if (g_fso.FileExists(sTargetXmlFile)) { var oFile = g_fso.GetFile(sTargetXmlFile); oFile.Attributes = oFile.Attributes & (~1); g_fso.DeleteFile(sTargetXmlFile); } WScript.Echo("The target converted policy file: " + sTargetXmlFile); var oSrcAddKeyNodes; var oSrcAddValueNodes; var sNameAttribute; var sTypeAttribute; var sDisabledAttribute; var sNodeValue; var oTargetAddKeyNode; var oTargetAddValueNode; var oAttributes; // Check "SecurityPolicy" node in source XML if (oSrcSecurityPolicyNode != null) { // Create "SecurityPolicy" node for target XML var oTargetSecurityPolicyNode = g_xmlTarget.createNode(1, c_sSecurityPolicy, c_sNameSpace); // Add attributes under "SecurityPolicy" child node to target node oAttributes = oSrcSecurityPolicyNode.attributes; for (var index = 0; index < oAttributes.length; index++) { if (oAttributes.item(index).name != c_sXmlns) { oTargetSecurityPolicyNode.setAttribute(oAttributes.item(index).name, oAttributes.item(index).nodeValue); } } // Check "PolicySection" child node in source XML var oSrcPolicySectionNode = oSrcSecurityPolicyNode.selectSingleNode(c_sPolicySection); if (oSrcPolicySectionNode != null) { // Create "PolicySection" node for target XML var oTargetPolicySectionNode = g_xmlTarget.createNode(1, c_sPolicySection, c_sNameSpace); // Add attributes under "PolicySection" child node to target node oAttributes = oSrcPolicySectionNode.attributes; for (var index = 0; index < oAttributes.length; index++) { oTargetPolicySectionNode.setAttribute(oAttributes.item(index).name, oAttributes.item(index).nodeValue); } // Check "LocalGroupPolicySettings" child node var oSrcLocalGroupPolicySettingsNode = oSrcPolicySectionNode.selectSingleNode(c_sLocalGroupPolicySettings); if (oSrcLocalGroupPolicySettingsNode != null) { // Create "LocalGroupPolicySettings" node for target XML var oTargetLocalGroupPolicySettingsNode = g_xmlTarget.createNode(1, c_sLocalGroupPolicySettings, c_sNameSpace); oSrcAddKeyNodes = oSrcLocalGroupPolicySettingsNode.selectNodes(c_sAddKey); for (var iKeyIndex = 0; iKeyIndex < oSrcAddKeyNodes.length; iKeyIndex++) { // Create one "AddKey" node for target XML oTargetAddKeyNode = g_xmlTarget.createNode(1, c_sAddKey, c_sNameSpace); // Add attributes under "AddKey" child node to target node oAttributes = oSrcAddKeyNodes[iKeyIndex].attributes; for (var index = 0; index < oAttributes.length; index++) { oTargetAddKeyNode.setAttribute(oAttributes.item(index).name, oAttributes.item(index).nodeValue); } oSrcAddValueNodes = oSrcAddKeyNodes[iKeyIndex].selectNodes(c_sAddValue); for (var iValueIndex = 0; iValueIndex < oSrcAddValueNodes.length; iValueIndex++) { // Create "AddValue" node oTargetAddValueNode = g_xmlTarget.createNode(1, c_sAddValue, c_sNameSpace); // Add attributes under "AddValue" child node to target node sNameAttribute = GetAttribute(oSrcAddValueNodes[iValueIndex], c_sName); oTargetAddValueNode.setAttribute(c_sName, sNameAttribute); sTypeAttribute = GetAttribute(oSrcAddValueNodes[iValueIndex], c_sType); if (sNameAttribute == c_sFallbackOrder) { if (sTypeAttribute == c_sDWord) { oTargetAddValueNode.setAttribute(c_sType, c_sSZ); } else { oTargetAddValueNode.setAttribute(c_sType, sTypeAttribute); } } else if (sNameAttribute == c_sDefinitionUpdateFileShareSources) { if (sTypeAttribute == c_sDWord) { oTargetAddValueNode.setAttribute(c_sType, c_sSZ); } else { oTargetAddValueNode.setAttribute(c_sType, sTypeAttribute); } } else { oTargetAddValueNode.setAttribute(c_sType, sTypeAttribute); } if (oSrcAddValueNodes[iValueIndex].attributes.getNamedItem(c_sDisabled) != null) { sDisabledAttribute = GetAttribute(oSrcAddValueNodes[iValueIndex], c_sDisabled); oTargetAddValueNode.setAttribute(c_sDisabled, sDisabledAttribute); } sNodeValue = oSrcAddValueNodes[iValueIndex].text; oTargetNodeValue = g_xmlTarget.createTextNode(sNodeValue); oTargetAddValueNode.appendChild(oTargetNodeValue); // Append "AddValue" child node under current "AddKey" node oTargetAddKeyNode.appendChild(oTargetAddValueNode); } // Append "AddKey" child node under "LocalGroupPolicySettings" node oTargetLocalGroupPolicySettingsNode.appendChild(oTargetAddKeyNode); } // Append "LocalGroupPolicySettings" child node under "PolicySection" node oTargetPolicySectionNode.appendChild(oTargetLocalGroupPolicySettingsNode); } // Append "PolicySection" child node under "SecurityPolicy" node oTargetSecurityPolicyNode.appendChild(oTargetPolicySectionNode); } // Append "SecurityPolicy" node g_xmlTarget.appendChild(oTargetSecurityPolicyNode); g_xmlTarget.save(sTargetXmlFile); }-- Weitao Wang
This posting is provided "AS IS" with no warranties, and confers no rights.You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.