[
Today’s post comes to us courtesy of JoAnn McKimpson from the SBS Marketing Team
]
Are you concerned about the security of your company's data? If your employees use laptops, they can easily be lost or stolen. USB sticks are easy to lose or to leave in a customer's office. What if your office building was broken into and the thieves managed to steal servers and desktop computers? How can you make sure that you don't lose the company-critical information on your server? The BitLocker feature of Windows Small Business Server 2008 and of Windows 7 Ultimate can help mitigate these risks.
For the purposes of this post, let's consider that your accountant uses a laptop. The data is backed up on your server that is running Windows SBS, but you want to make sure that the data both on the laptop and on the server is protected. In this post, we'll discuss how you can use BitLocker to accomplish this goal.
BitLockerBitLocker encrypts all the data that is stored on the Windows operating system volume (and configured data volumes). This includes the Windows operating system, the hibernation and paging files, the applications, and the data.
BitLocker uses encryption keys to help ensure the integrity of the components that are used in the earlier stages of the startup process. By default, BitLocker is configured to use a Trusted Platform Module (TPM) chip for the storage and management of these keys. Protected volumes remain protected even if your accountant's computer is tampered with when the operating system is not running.
BitLocker encrypts the entire drive. Your accountant can log on and work with files normally, but BitLocker can help block hackers from accessing the system files that they rely on to discover your accountant's password or from accessing your accountant's drive by removing it from the laptop and installing it in a different computer.
Whenever you deal with the encryption of data, especially in an enterprise environment, you must consider how that data can be recovered in the event of hardware failure, changes in personnel, or other situations in which encryption keys are lost. BitLocker supports a robust recovery scenario.
BitLocker offers many benefits when you use it in Windows SBS 2008 or in Windows 7 Ultimate. A few of the primary benefits are as follows:
- Full-volume encryption: Everything written to a BitLocker-protected volume is encrypted. This includes the operating system itself and all applications and data.
- Integrity checking: In conjunction with the TPM, BitLocker verifies the integrity of early startup components, which helps prevent additional offline attacks, such as attempts to insert malicious code into those components.
- Recovery options: BitLocker supports a robust series of recovery options to ensure that data is available to legitimate users. When BitLocker is enabled, the user is prompted to store a "recovery password" that can be used to unlock a locked BitLocker volume. The BitLocker setup wizard requires that at least one copy of the recovery password is saved. In many environments, however, you might not be able to rely on users keeping and protecting recovery passwords; therefore, you can configure BitLocker to save recovery information to Active Directory or Active Directory Domain Services. We recommend that you save recovery passwords to Active Directory in enterprise environments.
- Remote management: BitLocker can be managed remotely by using Windows Management Instrumentation (WMI) or a command-line interface.
-
Secure decommissioning:
BitLocker helps ensure that data is not stored on disk in a way that would be useful to an attacker, thief, or new hardware owner. Because everything that is written to the disk is encrypted, you can render the data permanently and completely inaccessible by destroying all copies of the encryption keys. The disk itself is unharmed and can be reused for other purposes. The format tool in Windows Server 2008 has been updated so that a format command deletes the volume metadata and uses methods that are accepted by the security community to delete and overwrite any sectors that could potentially be used to obtain BitLocker keys.
In our scenario, we're discussing securing your accountant's laptop, but why stop there? You can use Group Policy to enforce BitLocker for all of the computers and USB drives in your domain.
From policy-configured Active Directory Domain Services integration for the escrow of recovery keys, to simple and efficient hardware recovery processes, BitLocker provides an integrated management experience. Group Policy settings that affect BitLocker are located in Computer Configuration/Administrative Templates/Windows Components/BitLocker Drive Encryption. For more information about BitLocker drive encryption and about these settings, see the following Microsoft TechNet article:
http://technet.microsoft.com/en-us/library/cc725719(WS.10).aspx
You can use Group Policy settings to configure BitLocker to require or to prevent different types of recovery password storage or to make them optional. You can also use Group Policy settings to prevent BitLocker from being enabled if the keys cannot be backed up to Active Directory. For more information about how to configure Active Directory to support recovery options, see Configuring Active Directory to Back up Windows BitLocker Drive Encryption and Trusted Platform Module Recovery Information ( http://go.microsoft.com/fwlink/?LinkId=82827 ).
Note: If you choose to save encryption keys in Active Directory, it is a best practice to promote an additional domain controller as a backup.
Two new sets of Group Policy settings have been introduced to support BitLocker and management of the TPM. All of the policy settings are explained in the Local Group Policy Editor and the Group Policy Management Console. To view more detailed explanations, start the Local Group Policy Editor by typing
gpedit.msc
at an elevated command prompt or in the
Start Search
box, and then examine the description provided for each of the settings in the table.
- The server must be equipped with a compatible TPM chip
- The active partition must contain startup configuration data and startup files.
- The target partition must meet the following requirements:
- The partition must be on a simple disk that is initialized for basic storage.
- The partition must be a primary partition. Extended drives and logical drives are not supported.
- The partition must be formatted by using the NTFS file system.
- The partition must not be compressed.
- The cluster size of the partition must be less than or equal to 4 KB.
-
The partition is not using software spanning, software mirroring, or software RAID.
Note: This tool works correctly in hardware RAID configurations. - For a split operation, at least 10 percent of the active partition must remain free after the partition size is reduced by 1.5 GB.
-
For a merge operation, the partition's total capacity must be at least 1.5 GB. Also, the partition must have at least 800 MB of free disk space.
You can use BitLocker to secure your server that is running Windows SBS 2008. BitLocker is an optional component in Windows SBS 2008; you must install BitLocker before you can use it. Please note that depending on your hardware configuration, enabling BitLocker can have a moderate impact on server performance. If your server is already I/O bound, you should upgrade your disk subsystem before implementing Bitlocker on the server that is running Windows SBS 2008.
Important: Before you install BitLocker, it is imperative that you perform a full backup of the server.
To install BitLocker during the initial configuration, follow these steps:
- When you install Windows Server 2008, the Initial Configuration Tasks window appears.
- Choose Add features , and then install BitLocker Drive Encryption.
- Restart your server.
To install BitLocker after the initial installation by using the Windows user interface, follow these steps:
- Click the Start button, and then click Server Manager .
-
Click
Add Features.
- Click to select the BitLocker Drive Encryption check box, and then click Next .
- On the Confirm Installation Selections page, click Install .
- When the installation is complete, click Close .
- On the Do you want to restart page, click Yes .
-
When the
Resume Server Configuration
page displays confirmation that the installation succeeded, click
Close
.
To install BitLocker after the initial installation by using a Command Prompt window, follow these steps:
-
Open a Command Prompt window as an administrator. To do this, follow these steps:
- Click the Start button, click All Programs , and then click Accessories .
- Right-click Command Prompt , and then click Run as administrator .
- If the User Account Control dialog box appears, confirm that the action it displays is what you want, and then click Continue .
-
At the command prompt, type the following command:
ServerManagerCmd -install BitLocker -restart
Note: This command installs BitLocker if you have not already installed it and then restarts the server.
After you install BitLocker, turn on BitLocker Drive Encryption:
-
Click the
Start
button, click
Control Panel
, click
Security
, and then click
BitLocker Drive Encryption
.
Note: If BitLocker Drive Encryption is not available, download and run the BitLocker Drive Preparation Tool. For more information, visit the following Microsoft website :
http://support.microsoft.com/kb/933246 - If the User Account Control dialog box appears, confirm that the action it displays is what you want, and then click Continue .
-
On the
BitLocker Drive Encryption
page, click
Turn On BitLocker
next to the system drive.
Notes:- You must turn on BitLocker on the system drive to enable BitLocker on any other hard drives. After you turn on BitLocker on the system drive, you will see that BitLocker has been enabled on all other hard drives as well.
- If your TPM is not initialized, you will see the Initialize TPM Security Hardware wizard. Follow the directions to initialize the TPM, and then restart or shut down your computer.
-
On the
BitLocker Drive Encryption
page, click
Turn Off BitLocker
next to the system drive.
Since you have now turned on BitLocker for the other hard drives, you can now turn off BitLocker on the system drive to prevent undesirable impacts on server performance. -
On the
Save the recovery password
page, you will see the following options:
- Save the password on a USB drive . Saves the password to a USB flash drive.
- Save the password in a folder . Saves the password to a folder on a network drive or other location.
-
Print the password
. Prints the password.
Use one or more of these options to preserve the recovery password. For each option, select the option, and then follow the wizard steps to set the location for saving or printing the recovery password.
-
When you finish saving the recovery password, click
Next
.
Notes:-
The recovery password will be required in the event that the encrypted disk must be moved to another computer or if changes are made to the system startup information. This password is so important that we recommend that you make additional copies of the password and store it in safe places to ensure that you can access your data. You will need your recovery password to unlock the encrypted data on the volume if BitLocker enters a locked state. For more information, see "Scenario 5: Recovering Data Protected by BitLocker Drive Encryption" at the following
TechNet website
:
http://technet.microsoft.com/en-us/library/cc732725(WS.10).aspx#BKMK_S5
This recovery password is unique to this particular BitLocker encryption. You cannot use it to recover encrypted data from any other BitLocker encryption session. - Store recovery passwords separate from the computer for maximum security. If your recovery password is lost, Microsoft will be unable to assist you in data recovery.
-
The recovery password will be required in the event that the encrypted disk must be moved to another computer or if changes are made to the system startup information. This password is so important that we recommend that you make additional copies of the password and store it in safe places to ensure that you can access your data. You will need your recovery password to unlock the encrypted data on the volume if BitLocker enters a locked state. For more information, see "Scenario 5: Recovering Data Protected by BitLocker Drive Encryption" at the following
TechNet website
:
-
On the
Encrypt the selected disk volume
page, confirm that the
Run BitLocker system check
check box is selected, and then click
Continue
.
-
Confirm that you want to restart the computer by clicking
Restart Now
. The computer restarts, and BitLocker verifies whether the computer is BitLocker-compatible and ready for encryption. If it is not, you will see an error message that alerts you to the problem.
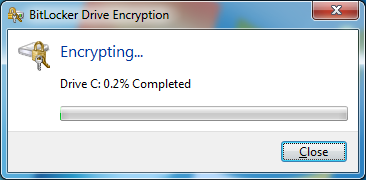
If the computer is ready for encryption, the Encryption in Progress status bar is displayed.
You can monitor the ongoing completion status of the disk volume encryption by placing your cursor over the BitLocker Drive Encryption icon in the notification area at the bottom of your screen.
-
When the encryption is complete, a confirmation appears. Click
Close
.
By completing this procedure, you encrypted the operating system volume and created a recovery password unique to this volume. The next time that you log on, you will see no change. If the TPM ever changes or cannot be accessed, if there are changes to key system files, or if someone tries to start the computer from a product CD or DVD to circumvent the operating system, the computer will switch to recovery mode until the recovery password is supplied.
For additional scenarios, refer to the "BitLocker Drive Encryption Step-by-Step Guide" at the following
TechNet website
:
http://technet.microsoft.com/en-us/library/cc732725(WS.10).aspx
Now that you've protected your server with BitLocker, you can use BitLocker Drive Encryption to help protect all the files that are stored on your employees' computers. BitLocker is available in Windows 7 Ultimate and can help protect the data that is stored on client computers, particularly mobile ones.
If you encrypt the operating system drive, BitLocker checks the computer during startup for any conditions that could represent a security risk (for example, a change to the BIOS or changes to any startup files). If a potential security risk is detected, BitLocker will lock the operating system drive and require a special BitLocker recovery key to unlock it. Make sure that you create this recovery key when you turn on BitLocker for the first time; otherwise, you could permanently lose access to your files. If your computer has the TPM chip, BitLocker uses it to seal the keys that are used to unlock the encrypted operating system drive. When you start your computer, BitLocker asks the TPM for the keys to the drive and unlocks it.
If you encrypt data drives (fixed or removable), you can unlock an encrypted drive with a password or a smart card, or you can set the drive to automatically unlock when you log on to the computer.
You can turn off BitLocker at any time, either temporarily by suspending it or permanently by decrypting the drive.
And of course you can also use BitLocker on your Windows 7 Ultimate laptops to ensure that confidential information on the hard drive cannot be accessed if the laptop gets stolen or lost. Users must supply the correct credentials to access the disk, either through a smart card and a PIN, by entering a password, or through their regular domain logon. Setting up BitLocker in Windows 7 Ultimate is a breeze; any Windows SBS administrator can enable BitLocker with a simple right-click since disk preparation is now automatic.
To turn on BitLocker, follow these steps:
-
To start BitLocker Drive Encryption, click the
Start
button, click
Control Panel
, click
System and Security
, and then click
BitLocker Drive Encryption
.
- Click Turn On BitLocker next to BitLocker Drive Encryption–Hard Disk Drives . This starts the BitLocker setup wizard. If you're prompted for an administrator password or confirmation, type the password, or provide confirmation.
-
On the
Save the recovery password
page, you will see the following options:
- Save the password on a USB drive . Saves the password to a USB flash drive.
- Save the password in a folder . Saves the password to a folder on a network drive or other location.
-
Print the password
. Prints the password.
Use one or more of these options to preserve the recovery password. For each option, select the option, and then follow the wizard steps to set the location for saving or printing the recovery password.
- On the BitLocker Drive Encryption page, click Next to begin encryption.
- Confirm that the Run BitLocker System Check check box is selected, and then click Continue .
-
Confirm that you want to restart the computer by clicking
Restart Now
. The computer restarts, and BitLocker verifies whether the computer is BitLocker-compatible and ready for encryption. If it is not, you will see an error message that alerts you to the problem.
If the computer is ready for encryption, the Encryption in Progress status bar is displayed:
You can monitor the ongoing completion status of the disk volume encryption by placing your cursor over the BitLocker Drive Encryption icon in the notification area at the bottom of your screen. -
When the encryption is complete, a confirmation appears. Click
Close
.
For additional information, refer to the "BitLocker Drive Encryption Step-by-Step Guide for Windows 7" at the following
TechNet website
:
http://technet.microsoft.com/en-us/library/dd835565(WS.10).aspx
.
By turning on BitLocker for your computers that are running Windows Server 2008 and Windows 7 Ultimate, you've gone a long way toward protecting your infrastructure from accidental loss and theft. Let's not forget the easiest to lose, though: removable media.
To protect USB sticks, thumb drives, and other portable media, you can use BitLocker to Go on your Windows 7 Ultimate workstations and laptops. BitLocker to Go protects any USB storage device and allows access only if you know the correct passphrase or key. As an administrator, you have control over passphrase length and complexity, and you can also set a policy that requires users to apply BitLocker protection to any removable drives before they can write to them. This means that even if your users lose their USB drive, no one else can get to the data unless they know the BitLocker key. To manually protect a removable storage device, connect the device to your Windows 7-based computer, follow the instructions in the " Help Protect Files and Folders on Client Computers " section of this post, and click Turn On BitLocker next to BitLocker Drive Encryption–BitLocker To Go in step 2.
A Note about Windows BackupTo protect the data contained within the backup files themselves, it is a best practice to store them on a data drive that has been encrypted with BitLocker. Although the backup may be of a drive that has been encrypted by BitLocker, the backup files themselves are not inherently encrypted. Also, if you must recover a machine that is protected by Bitlocker, you must reapply Bitlocker encryption after the restore. This does not happen automatically.
Help Protect Your Infrastructure with BitLockerAvailable in Windows SBS 2008 and in Windows 7 Ultimate, BitLocker Drive Encryption helps you protect your organization's sensitive information by encrypting the data that is stored on servers, client computers, and removable storage devices. You can easily install BitLocker, turn BitLocker on and off, and manage BitLocker by using Group Policy. To return to our scenario, as a result of turning on BitLocker throughout your infrastructure, you can feel confident that your employees' computers and removable media and your server are protected. Additionally, you've applied Group Policy to automatically enforce these settings. Thanks to BitLocker, you've backed up and protected your critical data.
For more information about the topics covered here, watch the following video:

You can also refer to the following resources for more detailed information and step-by-step instructions for using BitLocker:
-
Read the BitLocker Drive Encryption Overview at the following
TechNet website
:
http://go.microsoft.com/fwlink/?LinkId=99542 -
Read the Windows BitLocker Drive Encryption Step-by-Step Guide at the following
TechNet website
:
http://go.microsoft.com/fwlink/?LinkID=53779