All Lync Server 2010 client traffic is encrypted by default and secure by design. In fact, you can’t run the Lync Server client in TCP mode, it must run in TLS. Security is essential, but it can pose a challenge when you are troubleshooting an issue, or just trying to better understand your system. Fortunately, the Lync Server team has created tools to make your life easier. The Lync Server Logging Tool provides an easy way to monitor or troubleshoot Lync Server traffic such as SIP traces in the clear. The awesome Microsoft Lync Server 2010 Resource Kit Tool: Snooper tool can parse log files and make them easy to read.
Author : Tom Arbuthnot
Publication date : February 15, 2012
Product version : Lync Server 2010
The Logging Tool and Snooper will address 99% of the troubleshooting issues you are likely to encounter in your Lync Server deployment. But, what if you do want to capture the actual network traffic, decrypt it, and see what's going on frame by frame? With a little effort and the right tools, you can meet the challenge.
Several additional tools are required, but after you set them up correctly it's a straightforward process to decrypt a capture. To find out how, read on.
Tools
Use these four tools on the server and a client machine to decrypt the traffic.
- Microsoft Netmon 3.4
- Network Monitor Open Source Parsers
- Lync Network Monitor Parsers
- Network Monitor Decryption Expert (install on the client machine for decrypting)
Step 1. Install the Tools
Install Microsoft Network Monitor on the Lync Server where you want to capture the traffic. Install the NM34_x64.exe edition, select the Typical setup option.
Install the latest version of Network Monitor Open Source Parsers on the Server, select the Typical install option.
Install Lync Network Monitor Parsers on the Lync Server, select the Typical install option.
When you have installed these three tools, you are ready to capture packets on the server.
Step 2. Capture the Traffic
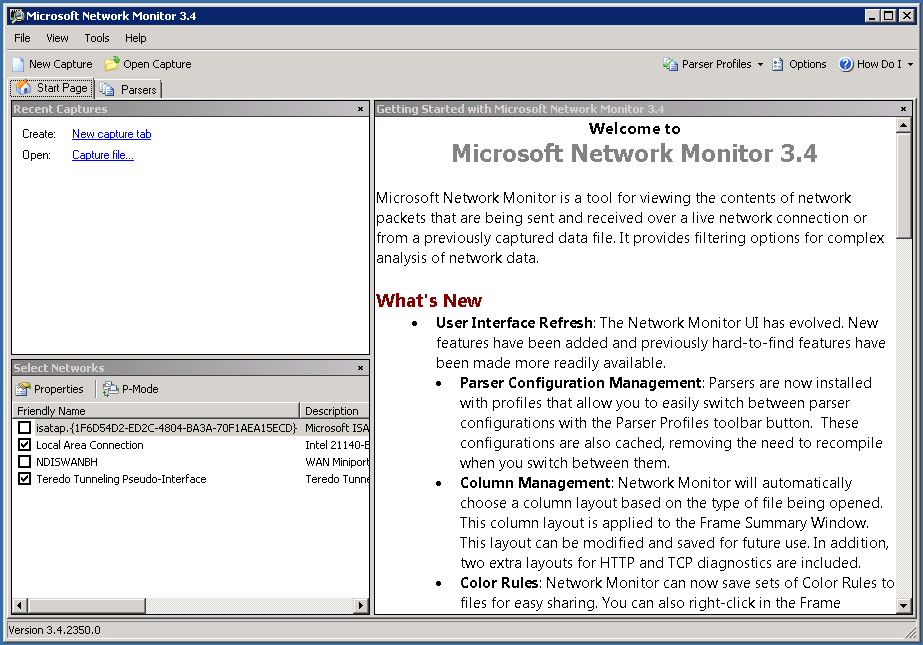
On the server start Microsoft Network Monitor .
Select Parser Profiles Options .
Figure 1. Network Monitor Parser Profiles Options

Confirm that you have the latest parser version.
Select NetworkMonitor Parsers for Lync as the active parser and click OK .
Figure 2. Confirm the parser version

To start the process click New Capture .
Figure 3. Network Monitor New Capture
Click the Capture 1 tab.
Figure 4. Network Monitor start capture

To begin the capture click Start. We need to capture the initial TLS handshake, so it is best to restart the Lync Server 2010 Services if possible, then sign-in to the Lync client to ensure we get the full TLS negotiation.
Figure 5. Network Monitor stop capture

When your capture is complete, click Stop and save the capture.
Figure 6. Network Monitor save the capture

The saved capture is TLS encrypted. Next, we’ll see how to decrypt it.
Step 3. Decrypt the Capture
Copy the capture to a local machine and decrypt it. If you haven’t already done so, install these four tools on the local machine.
- Microsoft Netmon 3.4 .
- Network Monitor Open Source Parsers .
- Lync Network Monitor Parsers .
- Network Monitor Decryption Expert . Select the Typical setup option.
Copy the capture file from the server to your local machine and open it.
Figure 7. Open the capture

View the capture file on your local machine.
Figure 8. View the capture file

To see the TLS traffic, filter by TLS.
Figure 9. Filter the capture file

You can see the TLS traffic, but the SIP information is encrypted.
Figure 10. View the SIP information

To decrypt the traffic with NmDecrypt, we need the information contained in the first TLS negotiation. The first negotiation contains the session ID. The session ID is used again in the session, but we must capture the first negotiation in order to get the information that NmDecrypt needs. In the case of a Lync client, the session ID is created during the initial sign in. Typically you need to start the capture and then sign in from the client whose traffic you want to capture.
There is a simple filter to confirm that you have this handshake information in your capture:
TLS.TlsRecLayer.TlsRecordLayer.SSLHandshake.HandShake.ClientHello.SessionIDLength == 0x0.
In our capture, this information is in frame 37.
Figure 11. TLS.TlsRecLayer

You may have captured traffic for multiple sessions and or clients. This can cause issues with NmDecrypt. You can narrow down the traffic in two different ways.
First, we can narrow it down by IP address. My client IP address is 192.168.5.73. I can apply the filter: IPv4.Address == 192.168.5.73 . We can now see the traffic between my Lync client and the server.
Figure 12. Filter by IP address

Alternatively, we can narrow down the traffic by filtering per session. Use the tree on the left to find the appropriate conversation, and then right click on the appropriate branch to automatically build the filter.
Figure 13 illustrates filtering by the session Conversation.IPv4.Id == 8.
Figure 13. Filter by session

Both approaches work under different situations. If one doesn't work, try the other.
After you have your filtered traffic, use the Save As dialogue to create a separate capture. Apply the filter, and select Displayed Frames when saving.
Figure 14. Save the capture

To identify the certificate, you must find the TLS Handshake. Be advised, you may have only one certificate and it may be on your Lync Server.
The frame TLS:TLS Rec Layer-1 HandShake: Server Hello. Certificate. Certificate Request. Server Hello Done identifies the Certificate Description from the Server to the Lync client.
Figure 15. Select the TLS handshake

If we examine the frame, we can see the certificate. Look for Cert: 0x1 .
Figure 16. Frame detail

We can see the certificate serial number and the Subject Name.
Figure 17. Serial number

To decrypt the traffic, the certificate from the server must be exported as a PFX, along with the private key.
To get the certificate go to the MMC on the server and add the Certificates snap-in.
Figure 18. Add the Certificates snap-in
Select Computer account to manage certificate handling.
Figure 19. Select computer account

Select your local computer.
Figure 20. Select the computer

Browse to the Personal Certificates store.
Figure 21. Certificates store

Find the certificate that matches the capture Serial Number and Certificate Name.
Figure 22. Match the serial number

Export the Certificate including the private key to decrypt the traffic.
Note: Be careful with the certificate and private key. This file grants access to your environment.
Figure 23. Export the certificate

Figure 24. Export the private key

If you can't export your certificate, see the troubleshooting section.
Figure 25. Select the export file format

Create a strong password.
Figure 26. Create a password

Name the file.
Figure 27. Name the file

Export the file.
Figure 28. Complete the export process

Copy the exported certificate to your workstation for the decryption.
Use NmDecrypt and the certificate to decrypt the traffic. Under Experts , choose NmDecrypt and Run Expert .
Figure 29. Run NmDecrypt

NmDecrypt creates a decrypted copy of the packet capture. This enables you to share the decrypted capture without sharing your certificate and private key (sharing your certificate and private key is not recommended).
Choose your certificate and enter the password. Choose a new capture name.cap and logfile.txt.
Figure 30. Decrypt the file

Click Start . Depending on your machine, this process may take several minutes.
Figure 31. Viewing the sec decrypting process

When the process is complete, the decrypted packet capture will pop up in a new instance of NetMon.
You may see the error message shown in Figure 32 at the end of the process.
Figure 32. Potential error message

Sometimes NmDecrypt cannot open the newly created file. If this happens, browse to the file location and open the file manually.
Now, we can filter by SIP and see the SIP packet information in the clear.
Figure 33. Filter by SIP and SIP packet information

We can also see the HTTP in the clear.
Figure 34. Decrypted HTTP content

Summary
This article describes how to capture and decrypt network traffic in a Lync Server 2010 environment. Microsoft Network Monitor is used to capture traffic and NMDecrypt is used to decrypt that traffic. NMDecrypt makes it possible to share decrypted capture information without sharing your certificate and private key (sharing your certificate and private key is not recommended). When the process is complete, you can directly decrypt network traffic captured on Lync Server 2010.
Lync Server Resources
- Lync Server 2010 Documentation Library
- DrRez blog
- NextHop blog
- Lync Server and Communications Server resources
