Starting with Windows Server 2003 SP1, it is possible to provide server authentication by issuing a Secure Sockets Layer (SSL) certificate to the Remote Desktop server. This is easy to configure using the “Remote Desktop Session Host Configuration” tool on Server operating systems. Though no such tool is available on Client operating systems such as Windows Vista and Windows 7, it is still possible to provide them with certificates for Remote Desktop connections. There are two possible ways to accomplish this. The first method is using Group Policy and Certificate Templates, and the second one is using a WMI script.
[April 15, 2010: Updated to correct which certificates can be used.]
Part I: Using Group Policy and Certificate Templates.
This method allows you to install Remote Desktop certificates on multiple computers in your domain but it requires your domain to have a working public key infrastructure (PKI).
First, you need to create a Remote Desktop certificate template.
Creating Remote Desktop certificate template:- On the computer that has your enterprise Certification Authority installed start MMC and open the “Certificate Templates” MMC snap-in.
- Find the “Computer” template, right-click on it, and then choose “Duplicate Template” from the menu.
-
In the “Duplicate Template” dialog box, choose “Windows Server 2003 Enterprise” template version.
- The “Properties of New Template” dialog box will appear.
- On the “General” page of this dialog box, set both “Template display name” and “Template name” to “RemoteDesktopComputer”. Note: it is important to use the same string for both properties.
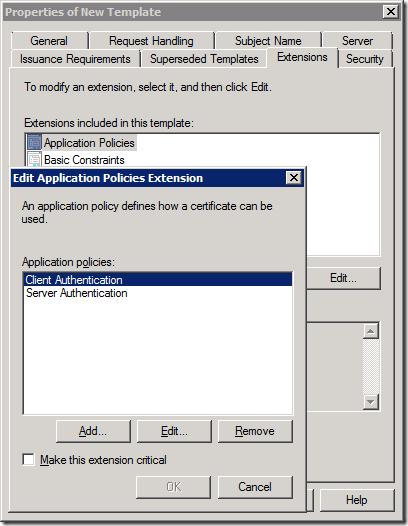
- On the “Extensions” page, select “Application Policies”, and then click the “Edit…” button.
-
The “Edit Application Policies Extension” dialog box appears.
- Now you can either remove the “Client Authentication” policy leaving the “Server Authentication” policy, or you can use the special “Remote Desktop Authentication” policy. Doing the latter will prevent certificates based on this template from being used for any purpose other than Remote Desktop authentication.
- To create the “Remote Desktop Authentication” policy, first remove both the “Client Authentication” and “Server Authentication” policies, and then click “Add…”
-
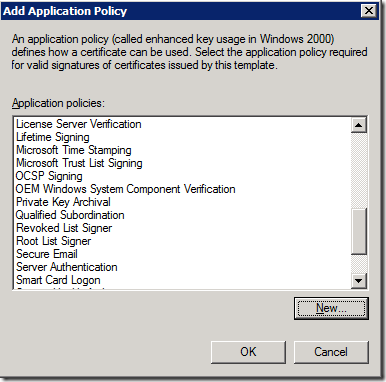
The “Add Application Policy” dialog box appears. In this dialog box click the “New…”
-
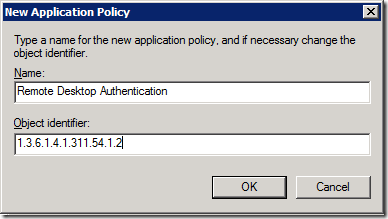
The “New Application Policy” dialog box appears. In this dialog box, set “Name” to “Remote Desktop Authentication” and “Object Identifier” to “1.3.6.1.4.1.311.54.1.2”, and then click “OK.”
- Select “Remote Desktop Authentication” in the “Add Application Policy” dialog box, and then click “OK.”
-
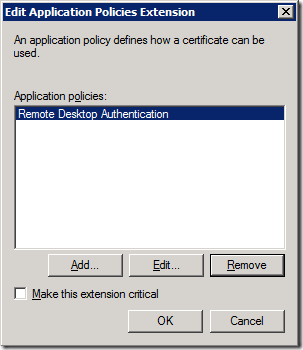
Now the “Edit Application Policies Extension” dialog box should look like this:
- Click “OK” in this dialog box, and then click “OK” in the “Properties of New Template” dialog box.
The new template is now ready to use.
The next step is to publish the template.
Publishing the “RemoteDesktopComputer” certificate template:- On the computer that has your enterprise Certification Authority installed, start the Certification Authority MMC snap-in.
- Right-click on “Certificate Templates”, then select “NewCertificate Template to Issue” from the menu that appears.
- The “Enable Certificate Templates” dialog box appears. Select “RemoteDesktopComputer”, and then click “OK.”
Now the “RemoteDesktopComputer” template is published and can be used in certificate requests.
The last step is to configure Group Policy to use certificates based on the “RemoteDesktopComputer” template for Remote Desktop authentication.
Configuring Group Policy:Note: The following steps create the new policy to apply to all computers in the domain, but it can also be scoped to an Organizational Unit if needed.
- On the domain controller, start the “Group Policy Management” administrative tool.
- Right-click the “Default Domain Policy” and click on “Edit…” in the menu that appears. The “Group Policy Management Editor” appears.
- Navigate to “Computer ConfigurationPoliciesAdministrative TemplatesWindows ComponentsRemote Desktop ServicesRemote Desktop Session HostSecurity.”
- Double-click the “Server Authentication Certificate Template” policy.
-
Enable the policy, type “RemoteDesktopComputer” in the “Certificate Template Name” box, and then click “OK.”
- As soon as this policy is propagated to domain computers, every computer that has Remote Desktop connections enabled will automatically request a certificate based on the “RemoteDesktopComputer” template from the Certification Authority server and use it to authenticate to Remote Desktop clients. You can speed up the propagation to a specific computer by running the “gpupdate.exe” command line tool on that computer.
Part II: Using a WMI script.
This method allows you to use a server certificate of your choice with Remote Desktop connections but the certificate needs to be manually installed on the computer first. For example, this method can be used if you bought your certificate from a public certificate authority.
First check that your certificate meets the requirements for Remote Desktop certificates. Certificates that don’t meet these requirements won’t work and will be ignored.
Basic requirements for Remote Desktop certificates:- The certificate is installed into computer’s “Personal” certificate store.
- The certificate has a corresponding private key.
- The "Enhanced Key Usage" extension has a value of either "Server Authentication" or "Remote Desktop Authentication" (1.3.6.1.4.1.311.54.1.2). Certificates with no "Enhanced Key Usage" extension can be used as well.
In order for a certificate to be used for Remote Desktop connections you first need to obtain the certificate’s thumbprint.
Getting the certificate’s thumbprint:- Double-click on the certificate.
- Click the “Details” tab.
-
Select the “Thumbprint” entry from the list.
- Copy the thumbprint value into Notepad.
- Delete all the spaces between the numbers.
Now you have the thumbprint string ready to use. It should look like this: 0e2a9eb75f1afc321790407fa4b130e0e4e223e2
Once you have the thumbprint you can use the following script to cause the certificate to be used for Remote Desktop connections.
WMI script for configuring Remote Desktop certificate:
var strComputer = "."; var strNamespace = "\root\CIMV2\TerminalServices"; var wbemChangeFlagUpdateOnly = 1; var wbemAuthenticationLevelPktPrivacy = 6; var Locator = new ActiveXObject("WbemScripting.SWbemLocator"); Locator.Security_.AuthenticationLevel = wbemAuthenticationLevelPktPrivacy; var Service = Locator.ConnectServer (strComputer, strNamespace); var TSSettings = Service.Get("Win32_TSGeneralSetting.TerminalName="RDP-Tcp""); if (WScript.Arguments.length >= 1 ) { TSSettings.SSLCertificateSHA1Hash = WScript.Arguments(0); } else { TSSettings.SSLCertificateSHA1Hash = "0000000000000000000000000000000000000000"; } TSSettings.Put_(wbemChangeFlagUpdateOnly); .csharpcode, .csharpcode pre { font-size: small; color: black; font-family: consolas, "Courier New", courier, monospace; background-color: #ffffff; /*white-space: pre;*/ } .csharpcode pre { margin: 0em; } .csharpcode .rem { color: #008000; } .csharpcode .kwrd { color: #0000ff; } .csharpcode .str { color: #006080; } .csharpcode .op { color: #0000c0; } .csharpcode .preproc { color: #cc6633; } .csharpcode .asp { background-color: #ffff00; } .csharpcode .html { color: #800000; } .csharpcode .attr { color: #ff0000; } .csharpcode .alt { background-color: #f4f4f4; width: 100%; margin: 0em; } .csharpcode .lnum { color: #606060; }
To run this sample, copy/paste the above code into a “rdconfig.js” file, start cmd.exe as the Administrator, and then run the following command: “cscript rdconfig.js <thumbprint of your certificate>”. Running this script without a parameter will revert Remote Desktop back to using the default self-signed certificate.