- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Empower data security teams to proactively manage insider risks across diverse digital estate
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
In today's era of digital and AI transformation, an organization's data stands as the driving force behind its operations and future trajectory. With businesses increasingly reliant on data, the imperative task for security teams is safeguarding this invaluable resource from cyber threats and insider incidents.
Our Data Security Index report highlights the ongoing issue of insider risks within organizations, shedding light on the fact that malicious insiders are often perceived as one of the least prepared causes of data security incidents by decision makers1. These findings are aligned with research from Forrester, which indicates that insider risks accounted for 26% of the security breaches reported in the past year. What's even more significant is that over half of these incidents were intentional2.
To secure data in diverse digital landscapes, including cloud environments and AI tools, detecting and mitigating data security risks arising from insiders is a pivotal responsibility. When it comes to risk detection and mitigation, our survey reveals that 74% of organizations express a preference for semi- or fully automated risk mitigation before analysts can review alerts. This streamlined approach affords teams more time to embrace a proactive stance toward data security1. Encouragingly, the study also demonstrates that organizations adopting proactive, rather than reactive, data security strategies have experienced shorter investigation completion times, reduced cost impacts, and increased confidence in averting potential data security incidents.
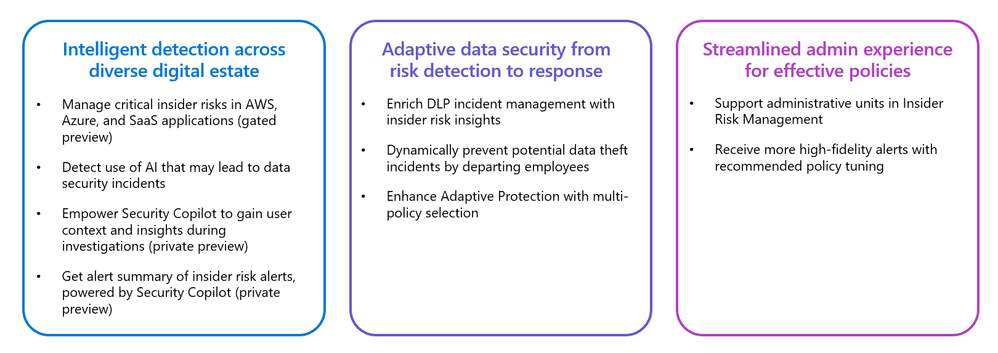
Today, we are thrilled to introduce several upcoming capabilities designed to empower security teams to manage insider risks proactively across their digital estate:
Manage critical insider risks in AWS, Azure, and SaaS applications
In a previous blog post, we announced the capability for security teams to bring their own detections to Insider Risk Management. This helps organizations address key challenges of the 147 public cloud services being used across SaaS, PaaS, and IaaS on average. Today, we are taking it to the next level with ready-to-use risk indicators to detect critical insider risks in Azure, AWS, and SaaS applications, including Box, Dropbox, Google Drive, and GitHub. With this update, admins with appropriate permissions will no longer need to manually configure detections for these environments. They can utilize the curated and preprocessed indicators.
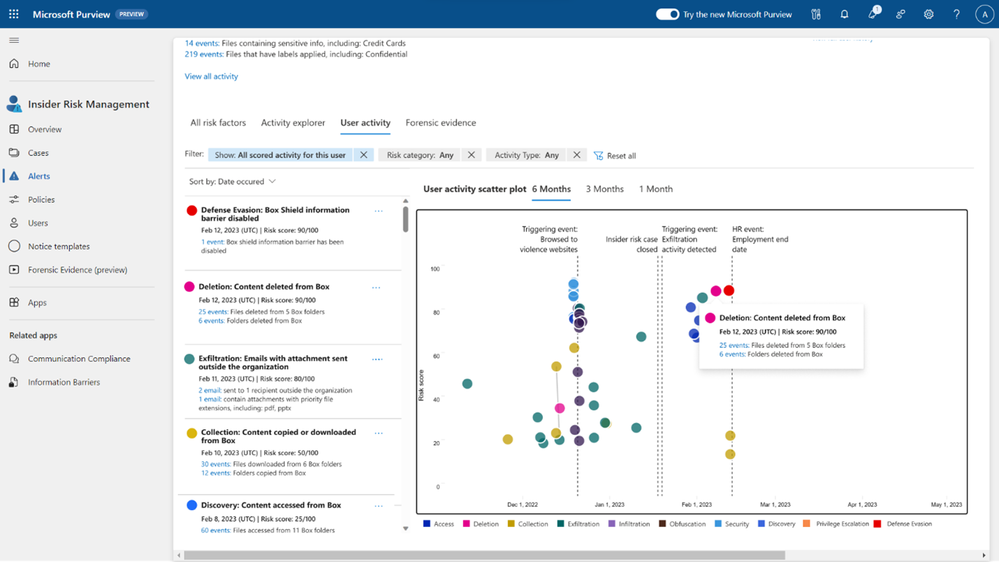
As users within organizations use multiple applications and cloud services in their day-to-day work, security teams must manage the risks associated with these user activities that may lead to potential data security incidents. With this exciting announcement, security teams gain the ability to access aggregated insights of user actions that may potentially lead to data security incidents across their digital environments. In the example illustrated in the screenshot, you can observe that Insider Risk Management generated an alert when a user downloaded numerous files from Box, followed by the user sending an email containing confidential information to an external recipient. All of these insights are now consolidated within a single alert, eliminating the need for analysts to manually cross-reference systems in order to obtain a comprehensive view of a potential insider incident.
These ready-to-use indicators across your diverse digital estate are in gated preview, you can join our Customer Connection Program to learn more about how to access the capability.
Detect use of AI that may lead to data security incidents
As businesses adopt AI to help productivity and drive innovation, it is essential for security teams to join forces to enable secure AI use. In response to this demand, we are introducing a new indicator in Insider Risk Management: browsing to generative AI sites. Security teams can use this indicator to gain visibility into generative AI sites usage, including the types of generative AI sites visited, the frequency with which these sites are being used, and the types of users visiting them. With this new capability, organizations can proactively detect the potential data security risks associated with AI usage and take action to mitigate it. This list of generative AI sites is automatically kept up to date as new sites are added or becoming more popular. User information is pseudonymized by default with strong privacy controls in place to protect end user trust. Learn more about all the Microsoft Purview capabilities that help secure the data in the age of AI in this blogpost.
Empower Security Copilot to gain user context and insights during investigations
Enhancing data security requires strong teamwork across departments. Research shows that 62% of data security teams collaborate with their SOC team to improve their data security posture3, and for those who do, they tend to be more confident and proactive in data security. To support this collaboration and in response to the growing need for efficient and comprehensive security investigations, we are excited to announce the private preview of Microsoft Purview data security insights in Security Copilot. This includes user insights from Insider Risk Management, allowing the SOC team with Insider Risk Management role permissions to quickly identify the specific users involved in a security incident and their activity summary, such as detected sequence that may lead to potential security incidents. The anonymization controls within Insider Risk Management will be respected in this experience, so user information will be pseudonymized if the privacy control is turned on. This information allows security teams to understand the attacker's intent better, assess the potential impact on sensitive data, and respond proactively to prevent further data breaches or unauthorized access. To learn more about how to leverage Microsoft Purview for investigation, check out the Security Copilot in Microsoft Purview blog post.

Get incident summary of insider risk alerts, powered by Security Copilot
When we talk to customers, we hear that they are struggling to keep up with the volume of alerts. In fact, Data security teams receive on average over 50 data security alerts per day and can only get to 60-70% of them1, leaving them exposed to risks. To help with this challenge, we are thrilled to announce the integration of Security Copilot into Microsoft Purview in private preview, leveraging the power of generative AI to provide incident summary that helps accelerate investigations.
This alleviates the time and effort burden security teams once faced when they had to review a multitude of insights to determine the nature of a potential incident. With this new ability to summarize Insider Risk Management alerts, customers can quickly gain a highlight of the potential incident by identifying critical user details like resignation submissions, exfiltration activities, sequential patterns, user roles and unusual activities that may lead to potential security incidents. This AI-powered summary can help security teams quickly focus on the key leading evidence and locate the critical investigation paths forward.

Enrich DLP incident management with insider risk insights
In February, we announced the public preview of Adaptive Protection, helping security teams automatically apply strict DLP policies to users identified as high risks for potential data security incidents. We believe this initiative aligns with Gartner® projection that by 2027, 70% of CISOs in larger enterprises will adopt a consolidated approach to address both insider risk and data exfiltration use cases4. Today, we are excited to introduce another capability to further enhance the integration of DLP and Insider Risk Management, making both detection and response of data loss risks user-context aware.
Traditional DLP solutions generate alerts when certain conditions are met, such as when a user copied a confidential file “Vacation pics.zip” to a USB device. However, these alerts typically highlight only the specific incident and files impacted, without providing context about where the files originated or what other actions the user took. With this new feature powered by Insider Risk Management, DLP alerts are enriched with user context, allowing DLP or SOC analysts with appropriate permissions to see a summary of past user activities that may have led to potential data security incidents. This is all part of the incident management experience in Microsoft Purview and Microsoft Defender.
With this feature, the abovementioned DLP alert now contains a summary of the critical sequence of actions taken by the user, showing that they downloaded confidential files from SharePoint, downgraded the sensitivity label, and compressed the files into a seemly-benign zip file named “Vacation pics.zip” before exfiltrating them to the USB device. With this context, analysts can better understand the user’s intent and determine if they were trying to exfiltrate sensitive data while evading detection. This feature can help analysts gain a better understanding of a DLP incident and make faster, more informed decisions on how to respond to potential incidents.

Dynamically prevent potential data theft incidents by departing employees
When employees leave a company, there is a heightened risk of data theft. They may take company data with them, either with malicious intent or because they feel a sense of ownership over their work. It’s no surprise that 77% of organizations perceive business data, such as intellectual property or source code, as the most vulnerable1. To address this risk, we are excited to announce the addition of the HR resignation date as a condition in Adaptive Protection. This condition will be used to help calculate a user’s risk level, along with other activity indicators that may lead to potential data security incidents. With Adaptive Protection, you can proactively prevent data loss by enforcing a stricter DLP policy for departing employees who perform activities that may lead to potential data security incidents.
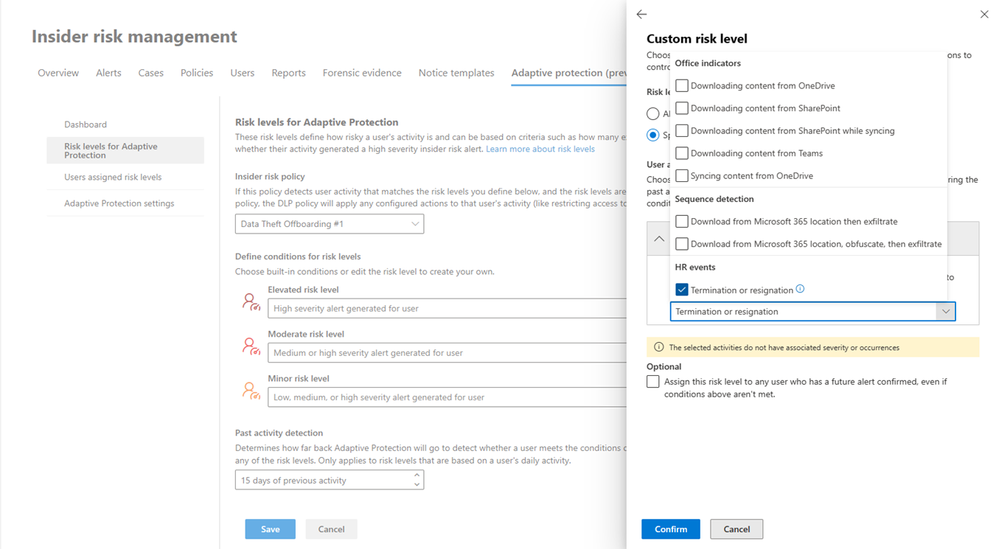
Enhance Adaptive Protection with multi-policy selection
The initial release of Adaptive Protection allowed configuration based on signals from a single policy in Insider Risk Management. However, we’ve heard from customers that multiple policies are often used to detect different types of risk, like data theft vs. data leaks, or to apply varying scopes across departments, like marketing vs. IT. To provide more comprehensive coverage, we are excited to announce the addition of multi-policy support to Adaptive Protection. This enhancement expands the scope and flexibility of the feature, allowing organizations to leverage multiple Insider Risk Management policies for indicators of user risk, which can then be used to dynamically adjust controls in a DLP policy.
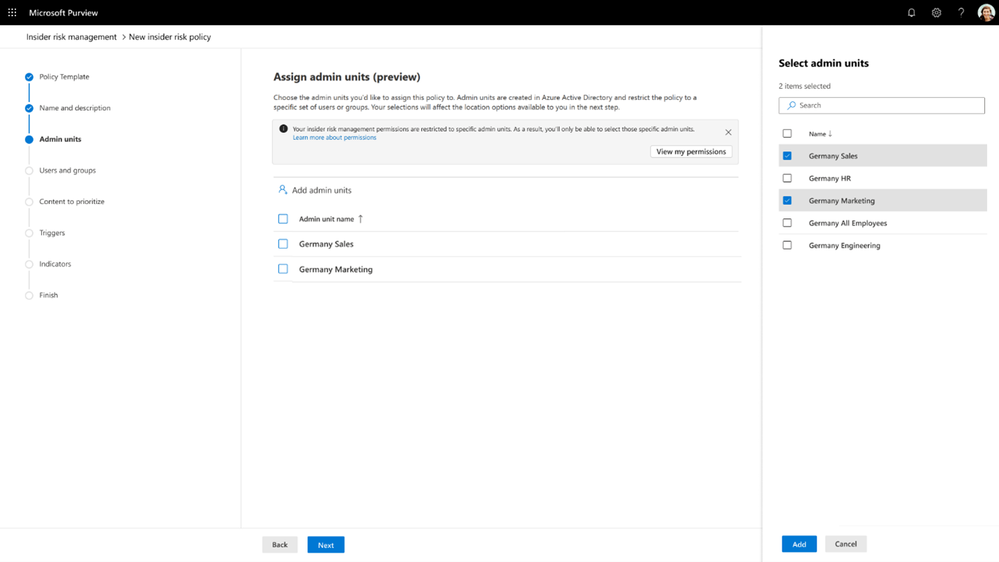
Support administrative units in Insider Risk Management
Different departments or geographic locations may have varying policies or preferences for managing insider risks. Regional regulations may also necessitate distinct designs or processes for implementing insider risk programs. To enable organizations to establish a global insider risk program that respects local requirements, Insider Risk Management now supports administrative units. This feature allows administrators with the appropriate permissions to subdivide the organization into smaller units and assign specific administrators or role groups to manage only the members of those units. For instance, German insider risk administrators can create and manage policies exclusively for German users, while German insider risk investigators can investigate alerts and activities solely from German users.
Get more high-fidelity alerts with recommended policy tuning
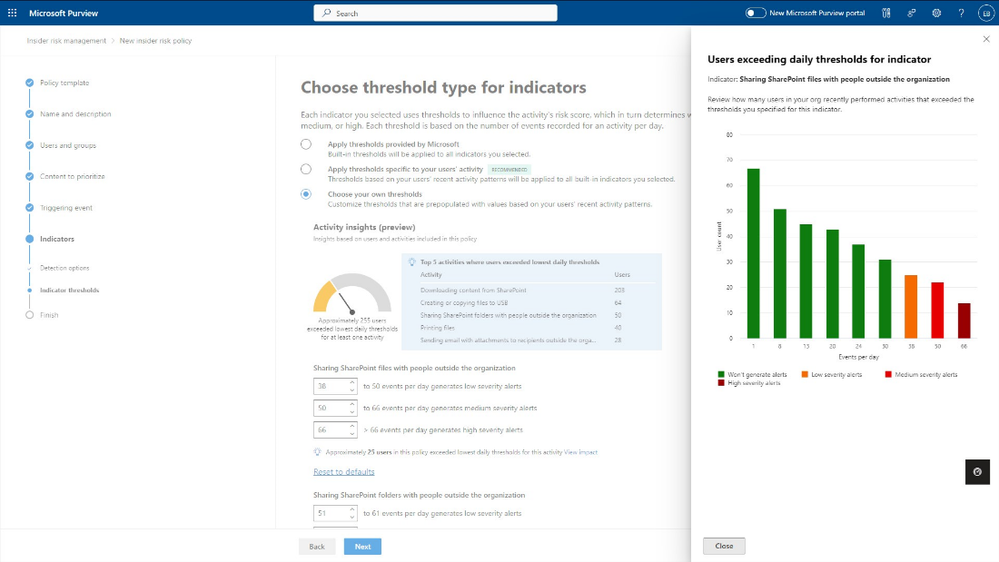
When instruments are finely tuned, music can be played smoothly. Similarly, data security solutions can be more effective and powerful when policy configurations are optimized for each organization’s unique risk appetite and business context. However, reaching an optimal stage can be time-consuming, as admins may need to experiment with different configurations, and each iteration can take several days to yield results. To address this challenge, Insider Risk Management now provides recommendations and sensitivity analysis to help admins set policy thresholds for certain user activities based on real-time analytics. This feature will save security teams time in fine-tuning policies and enable them to receive an optimal volume of high-fidelity alerts more quickly.
Explore more Insider Risk Management resources
We are thrilled to share these announcements with you. Here is a summary of next steps and other resources to help you and your organization get started with these capabilities:
- Join us at the Microsoft Purview breakout session: Secure and govern your data in the era of AI, or watch it on-demand, to explore other exciting announcements.
- Download Microsoft Data Security Index report to learn more about the trends and best practices for an effective data security program
- See how data security solutions in Microsoft Purview, including Insider Risk Management, are designed to help detect and respond to a corporate espionage incident.
- Learn more about Insider Risk Management in our technical documentation.
- Insider Risk Management is part of the Microsoft Purview suite of solutions designed to help organizations manage, govern and protect their data. If you are an organization using Microsoft 365 E3 and would like to experience Insider Risk and other Purview solutions for yourself, check out our E5 Purview trial.
- If you own Insider Risk Management and are interested in learning more about Insider Risk Management, leveraging Insider Risk Management to understand your environment, or building policies for your organization or investigate potential risky user actions, check out the resources available on our “Become an Insider Risk Management Ninja” resource page.
- Erin Miyake, Principal Product Manager, Microsoft Purview Insider Risk Management
---------
1 Data Security Index, Microsoft, Oct 2023
2 Internal incidents cause roughly a quarter of breaches, with more than half intentional, Forrester, July 2023
3 Microsoft internal data security research, Aug 2023
4 Gartner, Market Guide for Data Loss Prevention, Andrew Bales and Ravisha Chug, Sep 4, 2023 GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.