- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Announcing Updates to the M365 Attack Simulator
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Overview
The Microsoft 365 Attack Simulation team is pleased to announce the release of several new features in our phish simulation tool. This includes:
- an attachment-based phishing attack
- the ability to filter your simulation user targets by directory metadata like title, city, and department
- the inclusion of IP addresses and client data in the simulation detail report
- Simulation phish message simulations are included in your user phish submission reports
Attachment Attack
We know that phishing attacks that use attachments are very popular and an effective way for attackers to get malicious code to run on your endpoints. Teaching your users to be wary of attachments can reduce your overall risk. To help you educate your users of this risk, we've added a new type of simulation attack called Spear Phishing (Attachment) to the catalog.
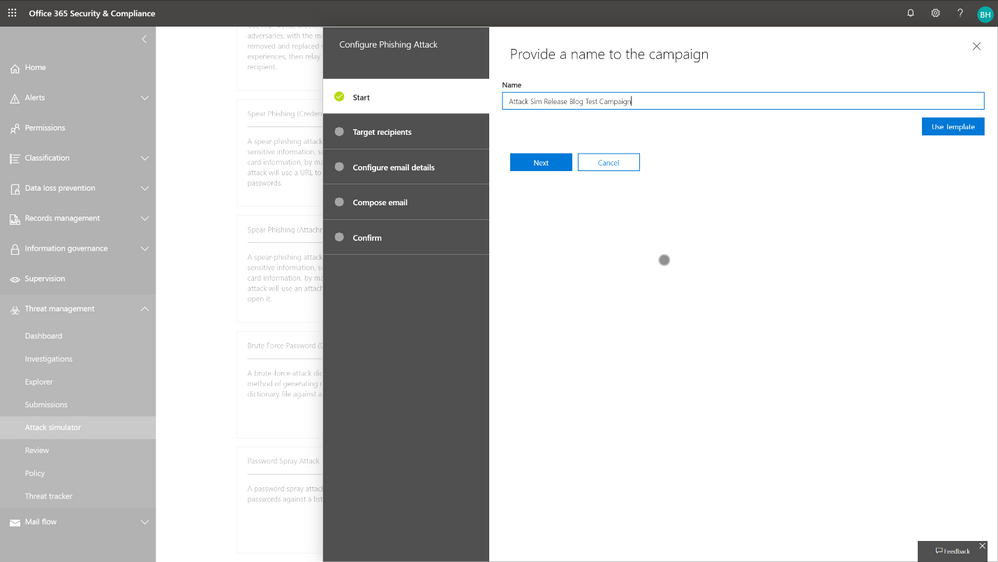
To launch an attachment attack, navigate to the home page of the Attack simulator:
Then, click Launch Attack and walk through the wizard:
First, give the attachment attack campaign a relevant, distinctive name.
Second, select users from your directory that you wish to target with the attachment attack.
Third, configure the attack with the sender, the name and type of the attachment, and the subject line of the email.
Fourth, enter a custom email template, or use one from the existing library. Remember that the point of the attachment attack is to get the user to open the attachment, so don't necessarily include a credential harvesting link, but do reference the attachment in the body of the email.
Lastly, confirm that you are ready to send the simulation off.
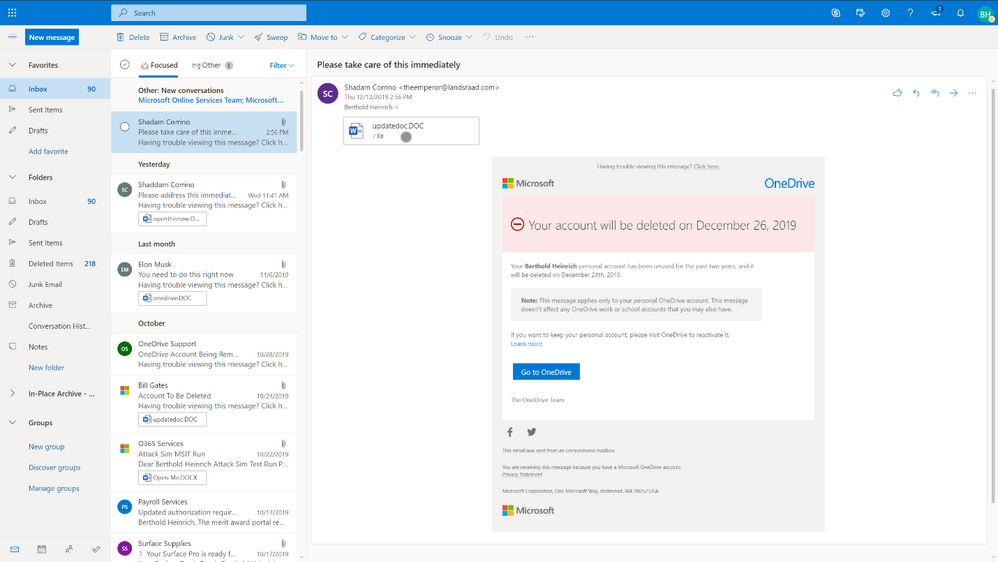
Within minutes, your users will receive the phishing email and will be able to see the attachment. This attachment does NOT contain any malicious content or executable code. Instead, it relies on a hidden image file which makes a call back to Microsoft's servers to indicate that the user has opened the file.
Here, you see the user has opened the file, which contains similar content to what you would see on the final page of a credential harvesting simulation. The user's name is populated, along with some educational messaging about the dangers of phishing.
If you have enabled the Outlook Reporting add-in for your organization, note that the user should go ahead and report this message as phishing.
Once they select report phishing, the user will be asked to confirm the report. Note below that we're including these reported messages in your report phish message pipeline via the Outlook reporting add-in so you can now track which of your users correctly reported this message as part of the simulation.
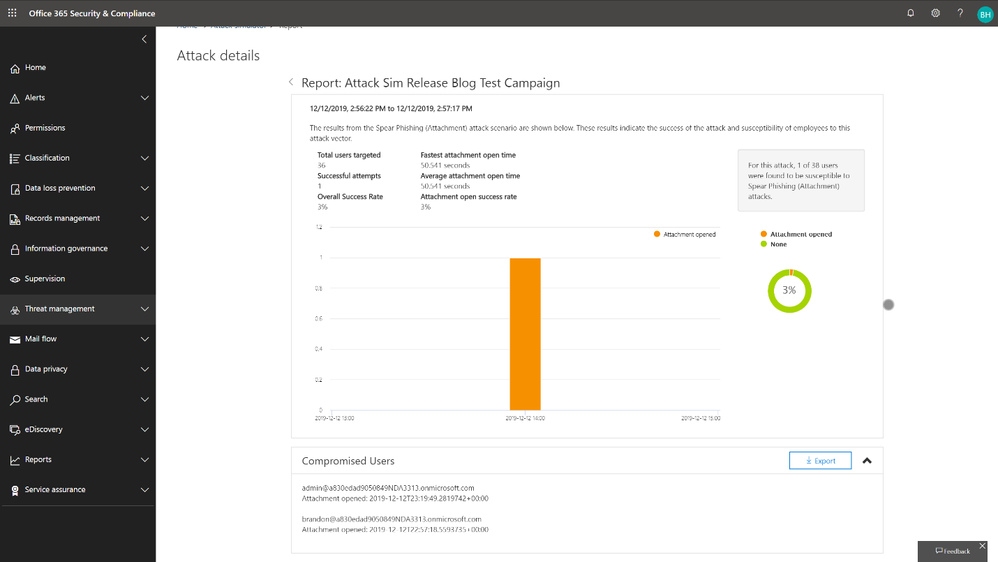
After the users have performed their actions, the simulation administrator can then review the final output of the campaign in the Attack Simulator portal.
Directory Filtering
Another quality of life feature we have added is the ability to perform an filtered search of your directory based on metadata like Title, Department, and City. This allows the simulation administrator to refine target groups based on existing directory data instead of having to manually select those users, leverage CSVs, or create custom directory groups. We encourage organizations to target high risk segments of their user population with more frequent simulations to further reduce your risk of getting phished.
Advanced Reporting Updates
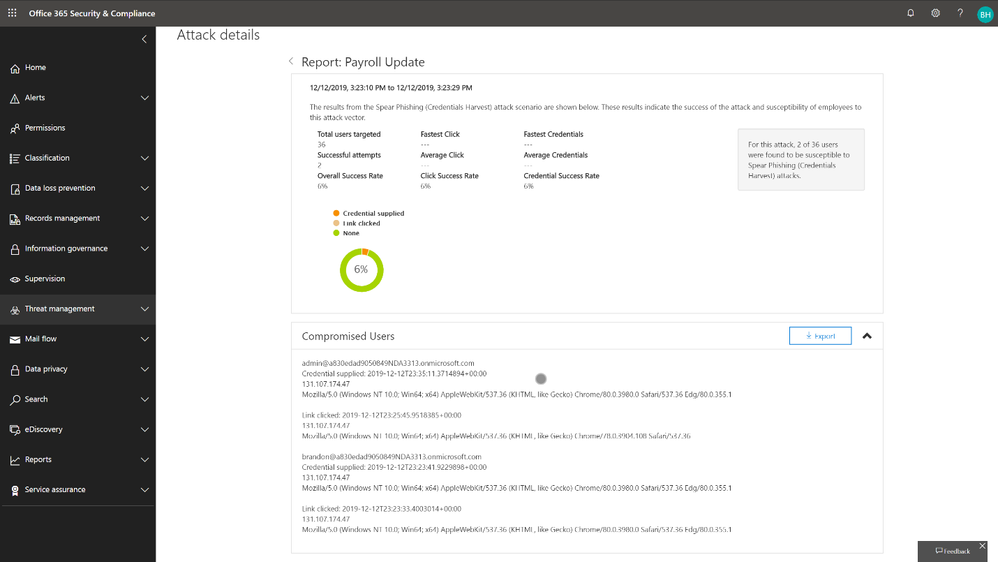
The final feature we've made available is the inclusion of detailed client information in the detail report of any given campaign, including username, action performed, datetime stamp, IP address, and client type information. This will allow you to better understand where your users are performing the risky actions.
Outlook Reporting Add-In Integration
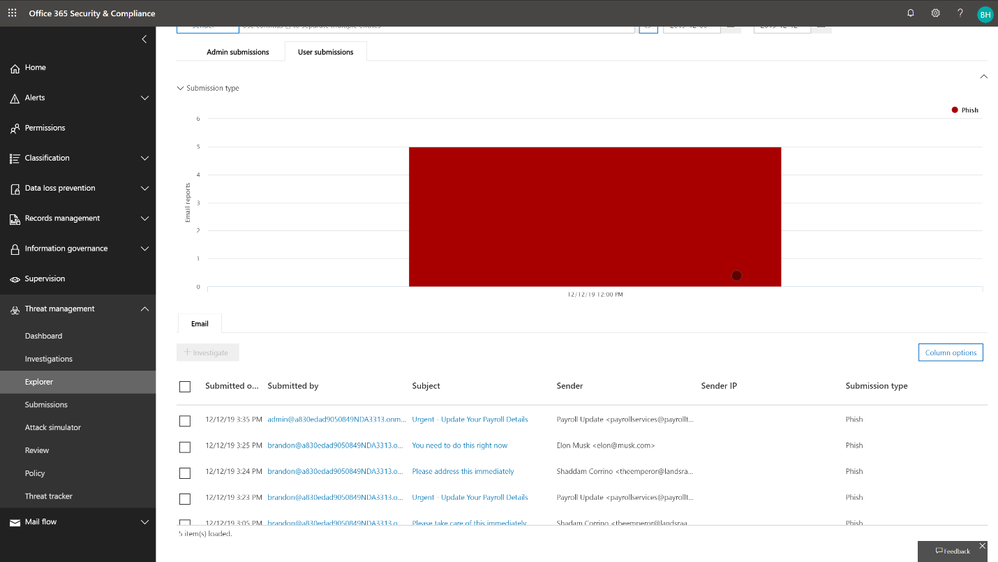
We're also including simulation phish messages in the normal reporting pipeline so that you can now track which of your users has correctly reported phish messages as part of the simulation exercise. This can be found by navigating to Threat Management-->Explorer-->View Submissions-->User Submissions.
Wrapping it up
So, there you have it – a whirlwind tour though the new updates to Office 365 ATP’s Attack Simulator. We’d like to encourage you to start taking advantage of the new functionality by the following the link (https://protection.office.com/attacksimulator) and we look forward to your feedback! More information on Attack Simulator can be found in the Attack Simulator documentation on Microsoft Docs.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.