- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Re: Min Diagnostic Event Categories for Azure Sentinel
Min Diagnostic Event Categories for Azure Sentinel
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 02 2021 10:36 AM
Hello
I've been trying to find some definitive recommendations on what event categories we should send in a diagnostic setting to the analytics workspace that the sentinel will ingest. I'm looking for only the categories that would have useful security information. Does anyone have some suggestions?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 03 2021 12:26 AM - edited May 03 2021 12:36 AM
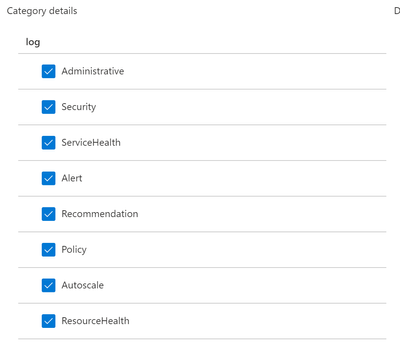
I would Say Security . You can find the description for each category below
Ref : https://docs.microsoft.com/en-us/azure/azure-monitor/essentials/activity-log-schema
Category | Description |
Contains the record of all create, update, delete, and action operations performed through Resource Manager. Examples of Administrative events include create virtual machine and delete network security group. | |
Contains the record of any service health incidents that have occurred in Azure. An example of a Service Health event SQL Azure in East US is experiencing downtime. | |
Contains the record of any resource health events that have occurred to your Azure resources. An example of a Resource Health event is Virtual Machine health status changed to unavailable. | |
Contains the record of activations for Azure alerts. An example of an Alert event is CPU % on myVM has been over 80 for the past 5 minutes. | |
Contains the record of any events related to the operation of the autoscale engine based on any autoscale settings you have defined in your subscription. An example of an Autoscale event is Autoscale scale up action failed. | |
Contains recommendation events from Azure Advisor. | |
Contains the record of any alerts generated by Azure Security Center. An example of a Security event is Suspicious double extension file executed. | |
Contains records of all effect action operations performed by Azure Policy. Examples of Policy events include Audit and Deny. Every action taken by Policy is modeled as an operation on a resource. |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 08 2021 11:43 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 09 2021 11:54 PM
In any case if you are using adavanced threat protection + analytics abnormal operations ( delete many files in a short time ) will be detected as security issues . If you build a good RBAC strategy leveraging least privilege and custom roles if needed you may have less false positives when adding administrative operations so yes that make sense.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 10 2022 02:15 PM