- Home
- Security, Compliance, and Identity
- Microsoft Entra
- MFA claim expired - Breaking web apps
MFA claim expired - Breaking web apps
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 17 2023 04:06 PM - edited Aug 17 2023 06:44 PM
Hi All,
Testing:
- Passwordless (Phone Sign-in baseline)
- Sign in Frequency (Shorter than tenant setting)
- Desktops are hybrid, receiving their PRT but no not use WH4B
- Tenant still has Remember Trusted device for X Days enabled
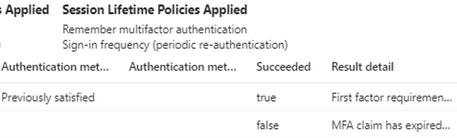
I'm seeing some strange behavior where Azure AD is showing the MFA claim has expired when trying to access web portals (Auth loops, webapp access issues (Outlook fine but not Teams), error messages). If I revoke the session completely and re-login to the native app pop-ups, things are fine again for a while. If the user closes the native auth window, the native apps limp along even with the MFA claim issue within the browser but the webapps are still broken. WebApps continue to SSO in with the token in this state.
Research is pointing that it might be the tenant wide remember trusted device settings, although I am not in a position to disable this global setting until after the test deployment. Disabling the SIF, seems to resolve the MFA claim expiry immediately, i'll check in a few days to see if that is still the case as it'd be outside the trusted device setting interval too.
I have a support request at the moment with the advice to enable persistent browser sessions which I'll test but don't think that is the core of the issue. Is their a way around this, have others had similar issues?
Thanks!
- Labels:
-
Conditional Access
-
MFA
-
Passwordless
-
SSO
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 08 2023 01:33 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 08 2023 02:15 PM
@anday unfortunately not, still pushing the ticket but nothing meaningful just yet
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 10 2023 04:40 PM
Notably, when I signed in to my computer using my yubikey, my account was no longer 'expired' for MFA on the device.
We can get around it currently by opening browsers in incognito or by signing out of the Edge browser and back in and choosing the 'Use another account' option. I'm glad I'm not the only person seeing this behaviour. I'll let you know if we get anything useful tomorrow!