First published on CloudBlogs on Jul, 26 2018
Howdy folks, Today, we’re turning on the public preview of Azure AD Activity Logs in Azure Monitor (Azure’s platform-wide monitoring service) — offering you long-term retention as well as seamless integration. These improvements and new capabilities offer you:

Howdy folks, Today, we’re turning on the public preview of Azure AD Activity Logs in Azure Monitor (Azure’s platform-wide monitoring service) — offering you long-term retention as well as seamless integration. These improvements and new capabilities offer you:
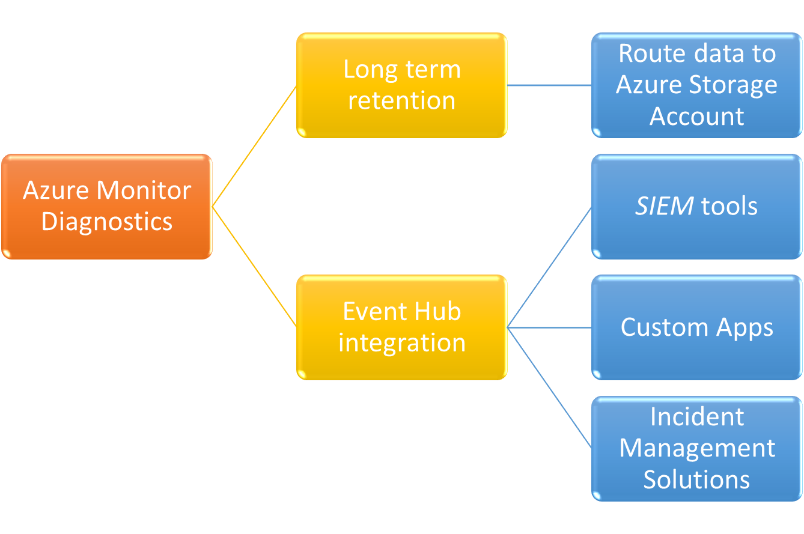
- Long-term retention by routing logs to your own Azure storage account.
- Seamless SIEM integration without writing or maintaining any custom scripts.
- Seamless integration with your own custom solutions, analytics tools or incident management solutions.

Figure 1: Azure Monitor Diagnostic settings for Azure AD Logs.

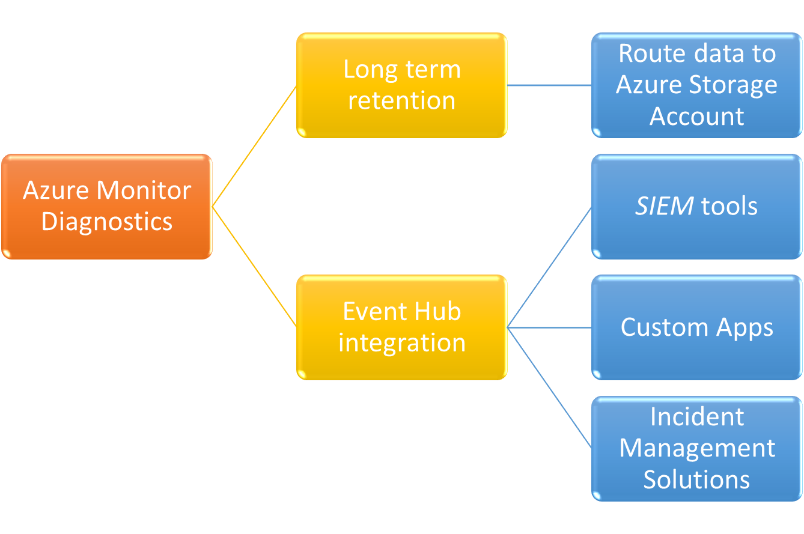
Figure 2: Sumo logic app showing Azure AD Logs (integrated through Azure Monitor).

Figure 3: Sumo logic app based on Azure AD Logs (integrated through Azure Monitor Event Hub).

Get started
To help get you started with Azure AD Activity Logs in Azure Monitor Diagnostics, we’ve put together some helpful resources- Overview of Azure AD Activity Logs in Azure Monitor Diagnostics —An in-depth look at the feature.
- Planning guide —Outlines the costs involved for using this feature.
- Archive data using storage account —Support to help you configure your Azure AD logs to be routed to your Azure storage account.
- Stream data to Event Hub —Support to help you configure your Azure AD logs to be routed to your Azure event hub.
- Configuration examples from our SIEM partners —Learn which SIEM tools are currently supported and who supports Event Hub integration.
What’s next?
As we work to bring this feature to general availability, we would really appreciate it if you could take a survey providing feedback on this feature . In addition, please add your voice to this feature through the Azure AD Reporting forum . Best Regards, Alex Simons (Twitter: @Alex_A_Simons ) Director of Program Management Microsoft Identity DivisionUpdated Jul 24, 2020
Version 6.0Alex Simons (AZURE) Microsoft
Microsoft
 Microsoft
MicrosoftJoined May 01, 2017
Microsoft Entra Blog
Follow this blog board to get notified when there's new activity