- Home
- Security, Compliance, and Identity
- Microsoft Defender for Identity
- New Users triggering "Resolve unsecure account attributes" for Password Not Required
New Users triggering "Resolve unsecure account attributes" for Password Not Required
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 01 2024 06:56 AM
Does Defender for Identity (Formerly Azure ATP) sometimes lose visibility on Users? I'd like to better understand how to remediate what are presenting as false positives. Here is what I'm seeing:
I'm noticing that some newly provisioned Users, synced to the cloud from on-prem AD, are being flagged for "Resolve unsecure account attributes" Microsoft Secure Score recommendation action - specifically for "Password Not Required". This is an all-or-nothing Recommendation for achievement, so 1 in 1000 can be the difference between compliance or non-compliance for the entire tenant.
These accounts are configured to require a password and are active on the network, however, this flag lingers for days or weeks.
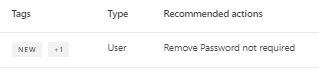
From the "Resolve unsecure account attributes" Recommendation's Exposed Entities tab.
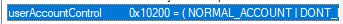
AD User Attributes confirm the configuration (0x10200) = ( NORMAL_ACCOUNT| DONT EXPIRE PASSWORD ) .
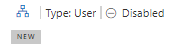
Defender object shows that the User is Disabled (incorrect)
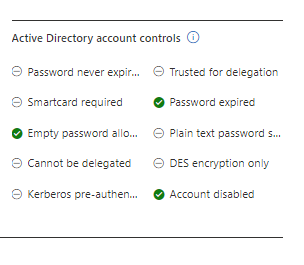
Defender's Active Directory account controls for the User show: