- Home
- Azure
- Azure Storage Blog
- Business Continuity with ABCC: Part 4: optimize security configuration
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Credits: This blog post has been reviewed by Utsav Raghuvanshi.
Hello everyone! This is Daya Patil here, continuing our series on business continuity with ABCC. In our previous session, we explored the concept of understanding the inventory of protected items in ABCC through Business Continuity with ABCC: Part 3: understand your protected items inventory - Microsoft Communi.... Today, we're going deeper into exploring the security optimization of protected items within ABCC.
Tailwind Traders case study
The escalating ransomware threats are a pressing issue for Tailwind Traders. They are persistently concerned about being adequately prepared and leveraging all essential security features to guarantee data recovery. In this section, we'll delve into how John, Tailwind's BCDR admin, can fulfill his upcoming objectives:
- Review security configurations for protected items
- Investigate best practices
- Enhance security setups for protected items.
View security level for protected items
John understands the security capabilities provided by Azure Backup at the vault level, ensuring the protection of stored backup data. These measures encompass the settings linked to the Azure Backup solution for the vault and extend to the protected data sources within it. However, he has often pondered: is it necessary to configure all these settings? Which settings are indispensable for critical resources? Among them, which one can effectively meet their organization's security requirements?
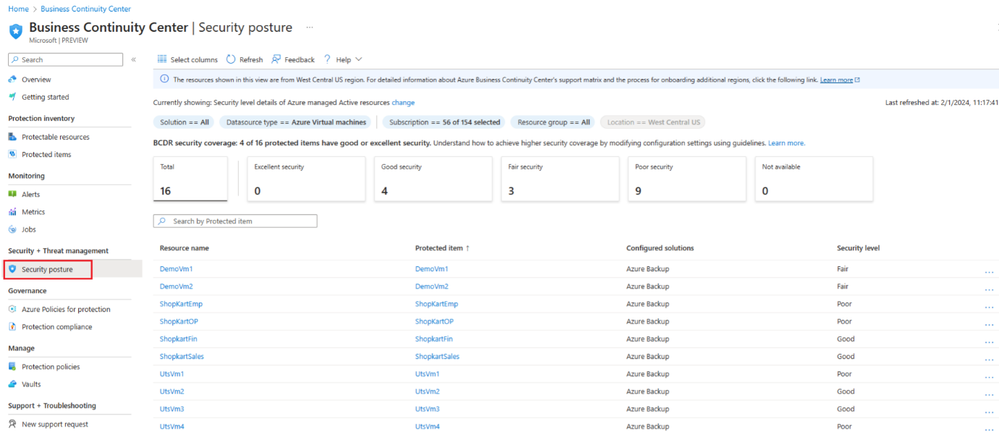
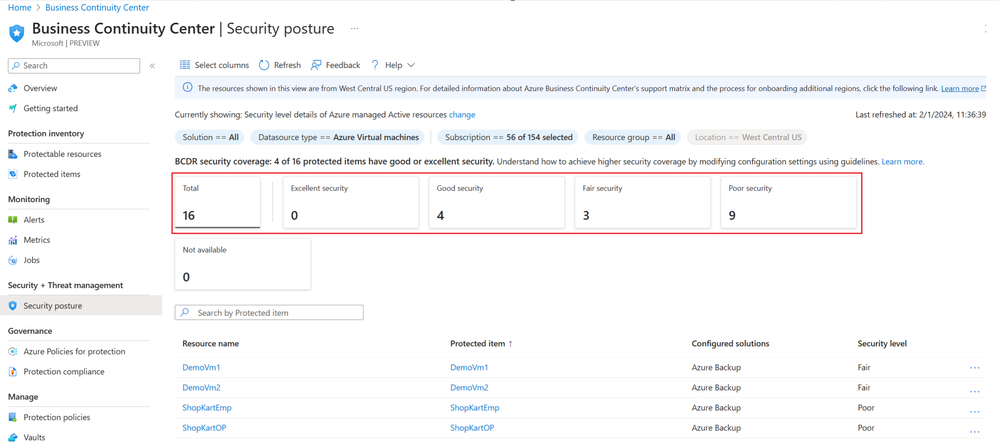
Caught in that uncertainty, John navigates towards the Security Posture view within ABCC. Alternatively, he can access this view by simply clicking on the "BCDR security coverage" tile situated on the ABCC overview page.
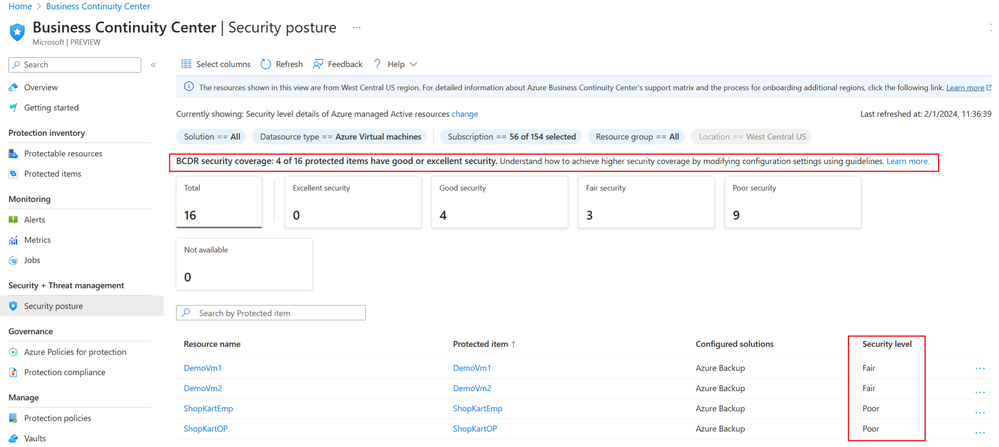
In the Security Posture blade, John notices a column called ‘security level’ which depicts a high-level summary of how well each item is protected using different security capabilities. He also notices that some of his items are identified as having ‘good’ or ‘excellent’ security levels. He wants to understand how these security levels are determined.
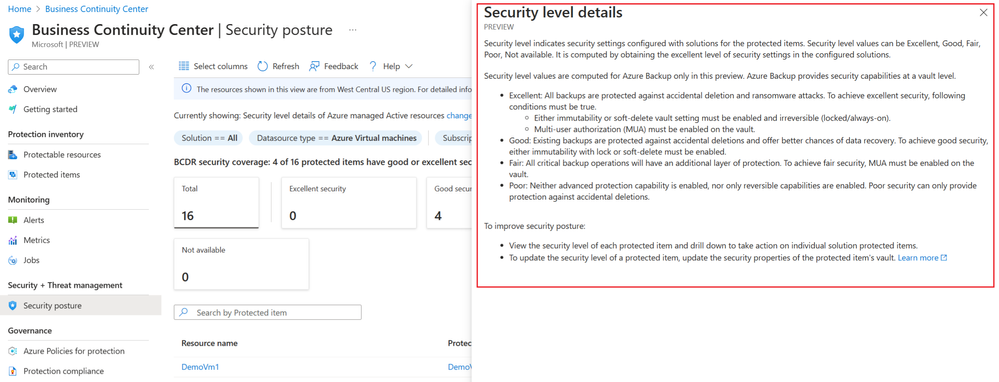
To find out more about security levels, he clicks the "learn more" link, which throw light on the significance of these security levels and how adjusting different security settings can enable him to attain varying levels of security. He also notes that security properties of a vault, and hence security levels, apply to all items protected in the vault.
Security levels for vaults used for Azure Backup and the protected data sources are categorized as follows:
- Maximum (Excellent): This level represents the utmost security, ensuring comprehensive protection. It is achieved when all backup data is safeguarded from accidental deletions and defends against ransomware attacks. To achieve this high level of security, the following conditions must be met:
- Immutability or soft-delete vault setting must be enabled and irreversible (locked/always-on).
- Multi-user authorization (MUA) must be enabled on the vault.
- Adequate (Good): Signifies a robust security level, ensuring dependable data protection. It shields existing backups from unintended removal and enhances the potential for data recovery. To attain this level of security, one must enable either immutability with a lock or soft-delete.
- Minimum (Fair): Represents a basic level of security, appropriate for standard protection requirements. Essential backup operations benefit from an extra layer of safeguarding. To attain minimal security, Multi-user Authorization (MUA) must be enabled on the vault.
- None (Poor): Indicates a deficiency in security measures, rendering it less suitable for data protection. Neither advanced protective features nor solely reversible capabilities are in place. The None level security only offers protection primarily against accidental deletions.
- Not available: For resources safeguarded by solutions other than Azure Backup, the security level is labelled as Not available.
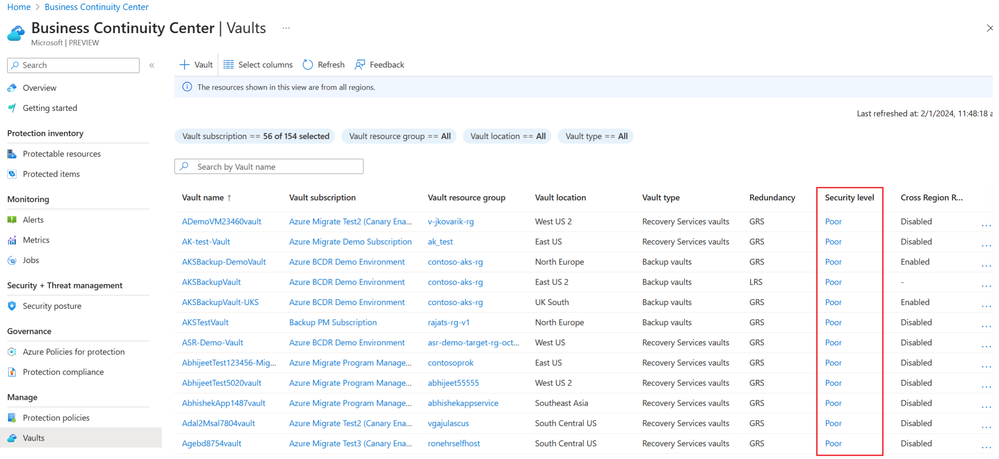
John can also see security level for each vault from ‘Vaults’ view in ABCC:
What a relief! Having received answers to all his inquiries, John is now completely clear. Moreover, within the view, he notices the count of resources categorized under each security detail using the Summary cards. These cards dynamically update based on applied filters at the top of the view, allowing further filtering and exploration of protected items with specific security levels simply by clicking on them.
Note: Currently security levels are applicable only for items protected by Azure Backup.
Customize the view
John notices similar options on the page to customize view like:
- Filters: John utilizes filters to tailor the displayed information to your specific requirements. Available filters include - solution, datasource type, subscription, resource group, location etc.
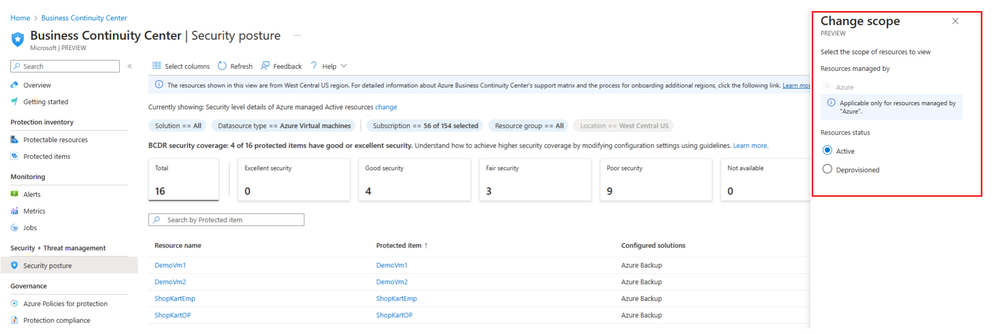
- Scope: John also notices the new scope feature in ABCC that enhances visibility into protection landscape across various platforms such as Azure and Hybrid environments. Clicking on “Currently showing: Security level details of Azure managed Active resources change" he discovers a range of available options, including:
- Resource status: Active, deprovisioned resources
- Search: John could also search by specific item name to get information specific to it.
- Select columns: Use Select columns from the menu available at the top of the views to add or remove columns.
Modify security level
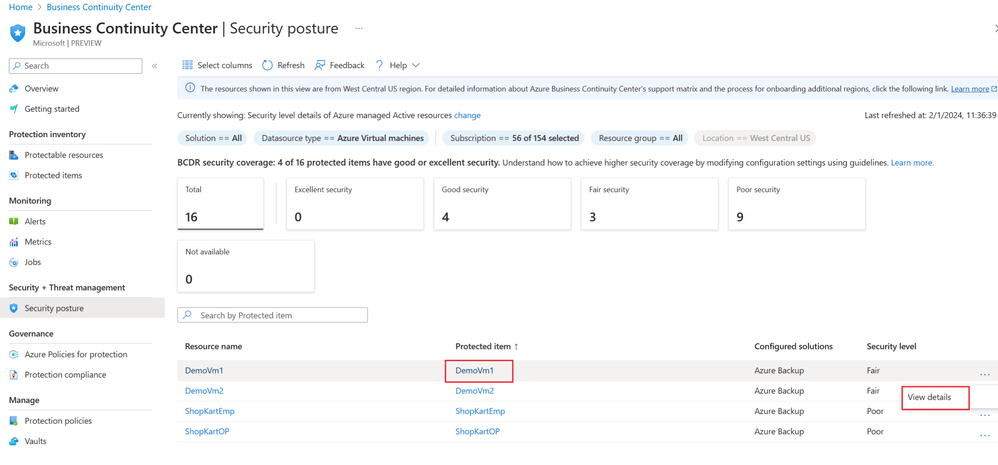
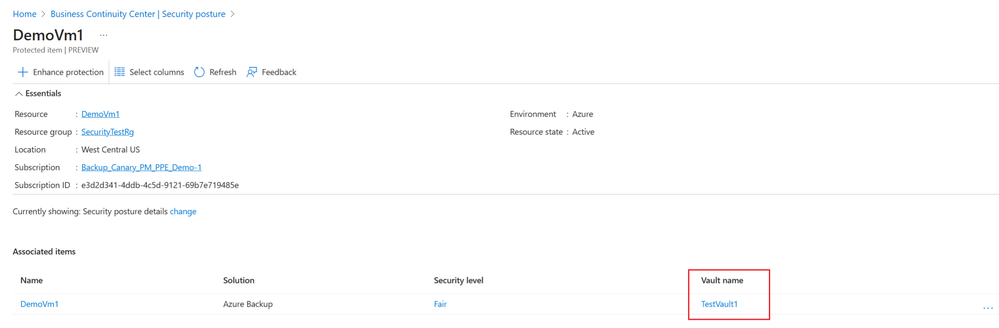
John realizes that some protected items require a higher security level than their current settings. To address this, on the Security posture view under Security + Threat management, John clicks on the ‘Protected item’. John can select the more icon … > View details action menu to navigate and view further details for an item.
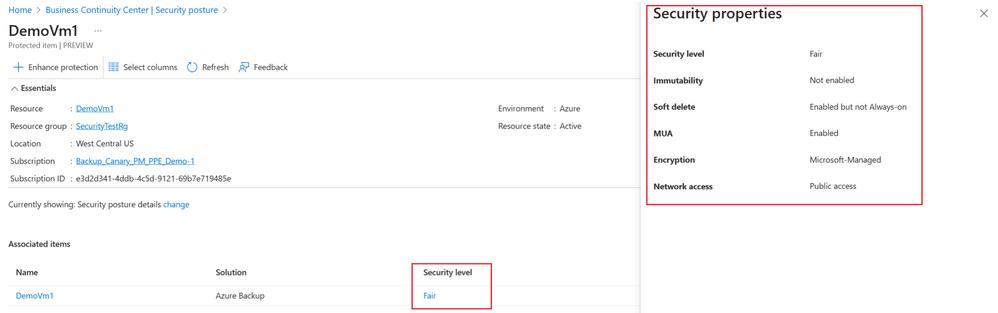
Within the item details page, John can easily observe the security level. Clicking on it provides him with insights into the security settings employed to achieve that level, along with their current values.
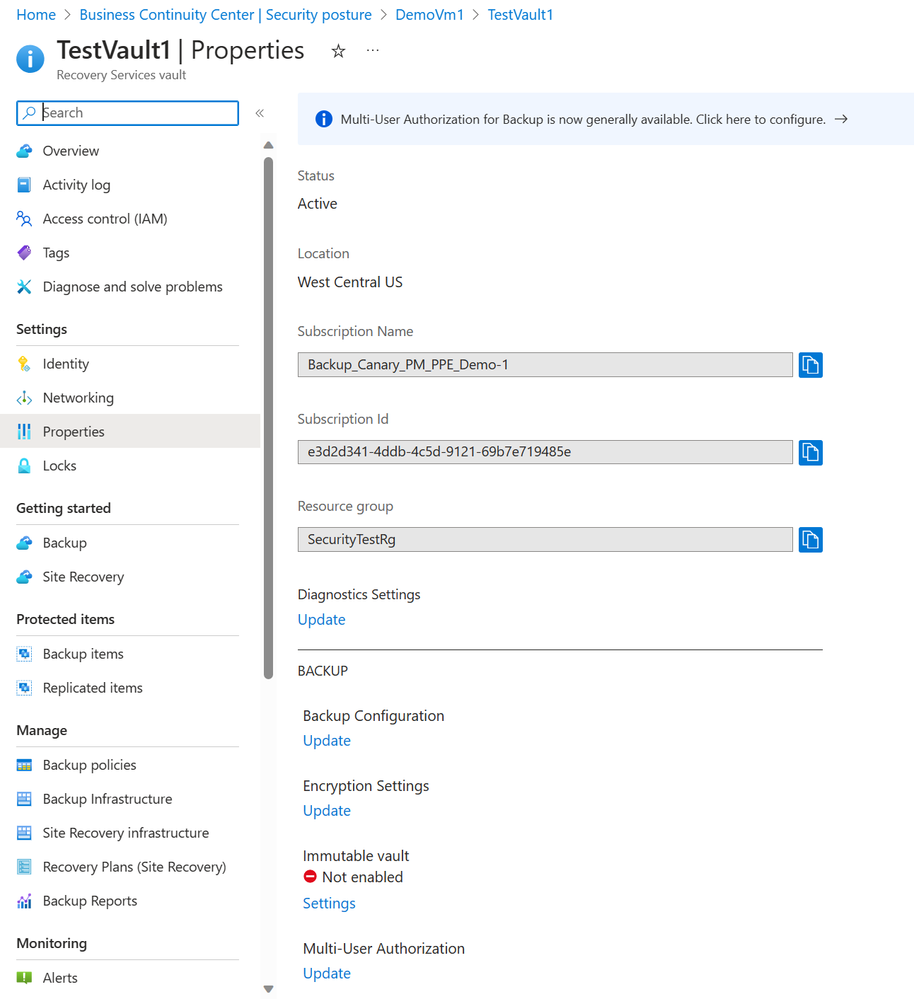
John also pinpoints the vault used for protecting the item. Clicking on the vault's name redirects him to the properties page of the vault.
On the vault properties page, John makes adjustments to the security settings following the previous guidance. Upon returning to ABCC, he observes that the security levels are now appropriately displayed for those items.
Note: When you modify the security setting for a vault, it gets applied to all the protected datasources by Azure Backup in that vault.
Learn about the view
Similar to other views, John notices the presence of built-in assistance within ABCC under the "Help" menu. Clicking on it reveals two valuable sections:
- Business Continuity Center: Presents a succinct overview of ABCC, outlining its different views and their respective objectives.
- The current view: Offers in-depth details about the current view, including information on filters, tiles, scope, columns, values, and more.
Having accomplished his goal of optimizing the security configurations, John utilizes the security posture views in ABCC. In the upcoming article, we'll explore John's journey of monitoring protection using ABCC.
Stay tuned………………
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.