- Home
- Windows Server
- Windows Server for IT Pro
- Microsoft's PrintNightmare update is causing a lot of problems with network printers
Microsoft's PrintNightmare update is causing a lot of problems with network printers
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 30 2021 09:33 AM
Dears,
the latest Windows updates is causing a lot of problems with network printers mapped on a print server.
Reference:
Manage new Point and Print default driver installation behavior
Managing deployment of Printer RPC binding changes for CVE-2021-1678 (KB4599464)
The two recent patches (KB5004945, KB5004760, or KB5003690) causes these two main problems:
1) unable for users without administrative rights to install new print drivers.
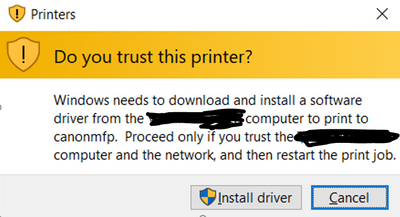
The end user receive this error
2) unable to use the print server with the new registry key RpcAuthnLevelPrivacyEnabled
**The system logs reports this error: 0x0000011b**
The two workarounds that you have to apply to survive and allow corporate users to be able to use the print server are:
1) Even if you have a GPO with "Point and Print Restrictions=disabled", you have to apply this registry key to allow non administrative users to install the latest print drivers from the print server
HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows NT\Printers\PointAndPrint
RestrictDriverInstallationToAdministrators = 0
2) Apply this registry key to disable the new default settings related to the print spooler vulnerabilities
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Print
RpcAuthnLevelPrivacyEnabled = 0
The above workarounds are only a temporary solution to survive and allow users to print.
What is unclear to me is what should be the right way to manage these settings in a corporate environment without any end user interaction.
So, if I want to be protected and apply the recent security fixes without asking the end users to do something, what should I do?
Microsoft states that you need to set "RpcAuthnLevelPrivacyEnabled" to "1" on both Client and Print Server in order to be protected, but if you do this, you can't print.
So, what should we do in a Corporate environment to be secure and print without any end user interaction about "driver installation" etc.?
Thanks in advance
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 04 2021 08:48 AM
We have the same problem, several users in our domain cannot print due to the 0x5 error. Impressive lack of support from microsoft in releasing a truly functional and secure update.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2023 10:34 AM
Thanks.