- Home
- PowerShell Community
- Windows PowerShell
- Configure AD FS 2016 and Azure MFA - How do I get the guid for Azure Multi-Factor Auth Client?
Configure AD FS 2016 and Azure MFA - How do I get the guid for Azure Multi-Factor Auth Client?
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 03 2018 12:58 PM - edited Apr 06 2018 12:48 AM
Hi All,
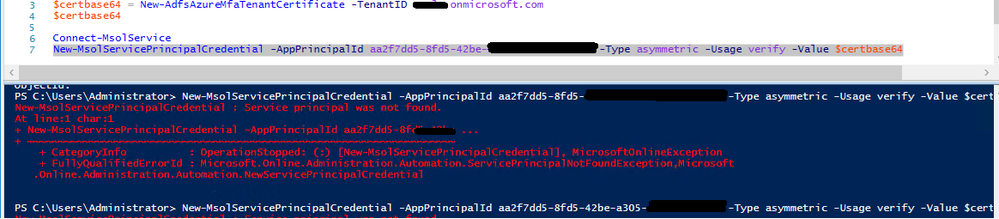
I am trying to Configure AD FS 2016 and Azure MFA as shown on the Microsoft site:
It says "981f26a1-7f43-403b-a875-f8b09b8cd720 is the guid for Azure Multi-Factor Auth Client" but doesn't show how we get this GUID.
When I try the command I get an error message I think is related to the GUID. How do I get the guid for Azure Multi-Factor Auth Client?
I hope you can help
Colin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 04 2018 12:09 AM
SolutionThe screenshot you posted uses a different GUID, make sure you provide exactly "981f26a1-7f43-403b-a875-f8b09b8cd720" as the value for -AppPrincipalID. As explained in the article, this is the id of the Azure MFA application that exists in your tenant:
Get-MsolServicePrincipal -AppPrincipalId 981f26a1-7f43-403b-a875-f8b09b8cd720
ExtensionData : System.Runtime.Serialization.ExtensionDataObject
AccountEnabled : True
Addresses : {Microsoft.Online.Administration.RedirectUri}
AppPrincipalId : 981f26a1-7f43-403b-a875-f8b09b8cd720
DisplayName : Azure Multi-Factor Auth Client
ObjectId : 81376720-790b-4752-bce1-a769de2bb39b
ServicePrincipalNames : {981f26a1-7f43-403b-a875-f8b09b8cd720, AzureMulti-FactorAuthClient}
TrustedForDelegation : False
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 02 2020 11:16 AM
Hello
I have Office 365 E3 plan, and i want to use ADFS with Azure MFA.
When i lunch
Get-MsolServicePrincipal -AppPrincipalId 981f26a1-7f43-403b-a875-f8b09b8cd720
I have thiss error :
Get-MsolServicePrincipal : Service principal was not found.
Thanks for your help
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 04 2018 12:09 AM
SolutionThe screenshot you posted uses a different GUID, make sure you provide exactly "981f26a1-7f43-403b-a875-f8b09b8cd720" as the value for -AppPrincipalID. As explained in the article, this is the id of the Azure MFA application that exists in your tenant:
Get-MsolServicePrincipal -AppPrincipalId 981f26a1-7f43-403b-a875-f8b09b8cd720
ExtensionData : System.Runtime.Serialization.ExtensionDataObject
AccountEnabled : True
Addresses : {Microsoft.Online.Administration.RedirectUri}
AppPrincipalId : 981f26a1-7f43-403b-a875-f8b09b8cd720
DisplayName : Azure Multi-Factor Auth Client
ObjectId : 81376720-790b-4752-bce1-a769de2bb39b
ServicePrincipalNames : {981f26a1-7f43-403b-a875-f8b09b8cd720, AzureMulti-FactorAuthClient}
TrustedForDelegation : False