- Home
- Windows
- Windows 365
- Re: Block Windows 365 portal-based Cloud PC sessions using Azure AD Conditional Access Policy
Block Windows 365 portal-based Cloud PC sessions using Azure AD Conditional Access Policy
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 30 2022 04:23 AM
Disclaimer: This blog post is provided as-is without any support statements and is meant to be generic guidance on the scenario addressed here. It should not be taken as a prescriptive guidance. Please validate in your environment before configuring.
Windows 365 enables connectivity to Cloud PCs via a number of client applications that can be run in Windows, Android, iOS and Linux operating systems. Each client supports different features, as documented here Remote Desktop clients feature comparison | Microsoft Docs and depending on the application used, users might have different end user experience such as Teams audio-video optimization. Due this disparity, administrators might want to block access from certain clients to provide a consistent user experience across their user base.
In this article, we will take a look how to configure Azure Conditional Access to prevent users from connecting to their Cloud PC using in-browser RDP session, while allowing the users to login to the portal and use other capabilities such as restart, restore, rename etc.
This blog post uses the CA article here as reference Enforce Azure Active Directory Multi-Factor Authentication for Azure Virtual Desktop using Condition...
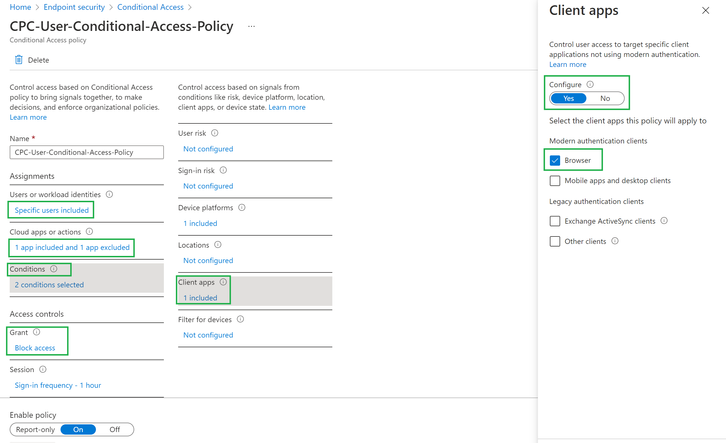
Create a conditional access policy with below configurations:
- User or workload identities – Include specific user(s) or group(s) for which the access needs to be blocked via HTML5 browser.
- Cloud apps or actions – Click on select under include view and search for Azure Virtual desktop (9cdead84-a844-4324-93f2-b2e6bb768d07) and add it. Click on exclude and add Windows 365 (0af06dc6-e4b5-4f28-818e-e78e62d137a5)
- Select Conditions, then Client Apps. In the Client Apps blade, set Configure to Yes and Select Browser option under Modern authentication clients list.
- Under Access controls section, select Grant and Block access
Result
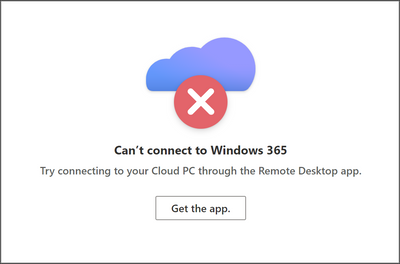
- Users will be able to login to windows365.microsoft.com which allows them to perform actions such as restart but won’t be able to launch connection as shown below.
Windows 365 Web Portal
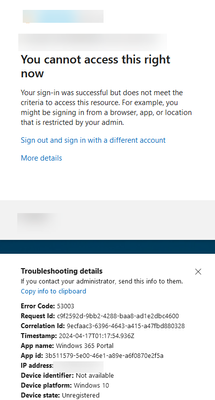
When the user clicks the Open in browser option, they will the below screen in a new tab
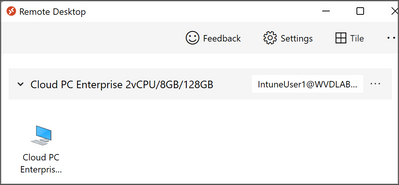
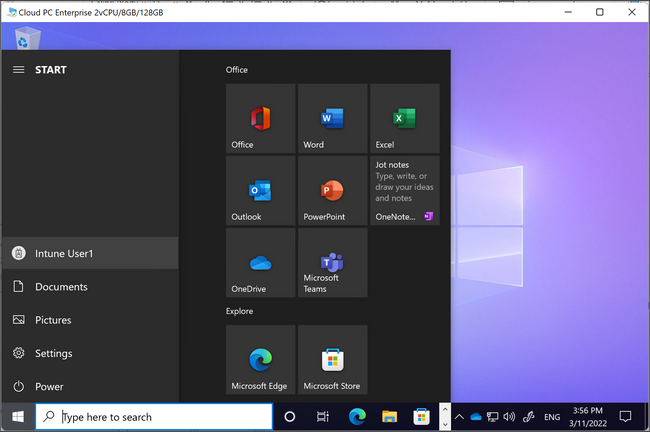
When the user launches the session from the RD Client, they will be able to successfully connect to the Cloud PC.
- Labels:
-
enterprise
-
General
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 30 2022 10:38 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2024 04:36 PM - edited Apr 16 2024 06:22 PM
@RavishankarN - I am getting a different result, I am completely blocked from accessing user action. Was this changed? Is there a way to access user action but block portal access?
Thanks