- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 07 2018 08:20 AM
1803 build 17134 is now available
Did it release as Semi-annual (Targeted) or Semi-annual?
windows-10 release-information
will it be the approximately 4 months before my rings begin to defer it as semi-annual or are they going to start installing it now if on the semi-annual branch???
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 09 2018 05:08 PM
The documentation is incorrect. 1803 is semi-annual targeted. If you have your deferral set to install feature releases as semi-annual it will be several months.
1803-semi annual targeted
1709-semi annual
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 10 2018 07:50 AM
"The documentation is incorrect."
that's cant be, Its Microsoft! they wouldn't release a feature update to 10 million devices and mess up the release communication (LOL)
I need MS to either fix their documentation or standby the release
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 05:22 AM
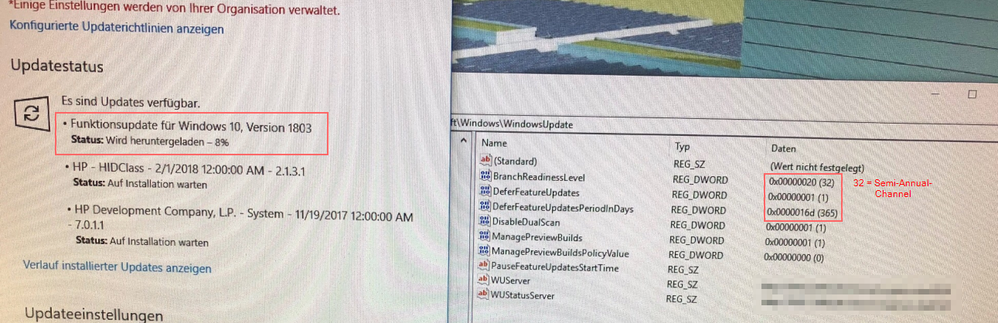
Take a look at this. Why is 1803 installed on a client with Semi-Annual Channel?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 06:33 AM
You aren't alone. I'm getting reports that 1803 is getting on machines that have semi-annual selected. It shouldn't even be near that machine.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 06:52 AM
Great and now? Microsoft please tell us a solution to stop this.... Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 06:56 AM
Use that to block it. (and come on Microsoft , I've lost count how many times deferrals haven't worked)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 05:52 PM
Hello,
The machines should not have been upgraded with that policy set, with a couple of exceptions
There are two ways this can happen.
- The dual scan scenario where the polices settings configuration is not set properly, we took changes to address this last summer, by adding a new policy but it’s possible that people have not figured it properly. The fix was to offer a new option but it’s possible that policy is not set.
- GP that sets Telemetry to Zero Exhaust
Is there a support case where machines were upgraded with that policy set?
Darrell Gorter [MSFT]
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 10:34 PM
Even with the dual scan issue these machines are set for "semi-annual". We are still at semi-annual targeted. There is no reason these machines should be getting 1803.
I have two other MVPs on a private list who are behind Windows update who got 1803 and they had semi-annual chosen as well.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2018 01:09 AM
Hello,
the Case No. is
- Service Request #: 118052418249642
- Service Request Title: Unwanted Installation of Windows 1803 - GPO with 365 Day delay is setup
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2018 03:05 PM
Fellow MVP, not behind a domain, therefore no WSUS/dual scan, telemetry on.
This is not the first time that feature releases have come down when they clearly should have respected the block.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2018 04:04 PM
Hello
We would like to see some log files and registry entries from machines that were upgrade to 1803 where you thought the feature update to 1803 was deferred.
Please Collect these registry values
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\DataCollection]
[HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\DataCollection]
and we would like to see the logs collected with this tool
https://aka.ms/wucopylogsexternal
Please Send the information to me
Darrellg.removethis.@microsoft.com
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2018 05:14 PM - edited May 25 2018 05:15 PM
Darrell,
Susan forwarded this to me as I have an affected machine. (I started the partner thread she cited.) Win10 Pro 32-bit virtual machine, domain environment, no WSUS. 64-bit machines in the same environment have not upgraded yet. Group Policy Result as follows:
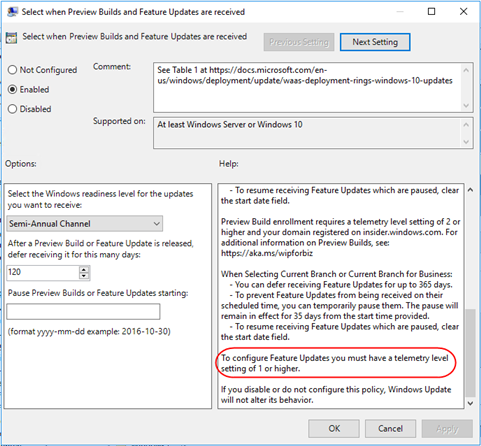
AllowTelemetry is set to Basic as shown in the group policy above:
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\DataCollection]
"AllowTelemetry"=dword:00000001
[HKEY_CURRENT_USER\SOFTWARE\Policies\Microsoft\Windows\DataCollection]
(Key exists but no values)
BTW I did see the note in Group Policy that I have to have AllowTelemetry=1 or higher:
However the setting of AllowTelemetry shouldn't matter on Pro anyway since 0 is the same as 1:
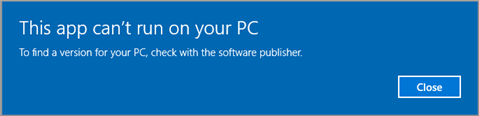
When I tried to run Copylogs.exe, I get this:
Must be 64-bit-only?
Mark Berry
MCB Systems
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2018 11:51 AM
Hello Mark,
We don't have a 32-bit version of tool available right now.
Can I get you to file a feedback request using the Feedback Tool
- Category: Install and Update
- Sub-Category: Windows update
Promote to a bug, Upload Logs.
Send me the Feedback ID or post to this thread
Thanks
Darrell
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2018 04:01 PM
Darrell,
I submitted feedback without signing in. (I prefer domain accounts and don't link my Microsoft account to most machines.) I told it to submit logs but I did not see the option to "promote to a bug." I did not get a feedback ID but it did create this empty folder:
C:\Users\<MyUser>\Documents\FeedbackHub\{b1b0d70e-7d3d-49bb-8d1e-af6c040ee2fe}
If you have a list of logs that's not too long, I can just zip them up for you.
Mark Berry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2018 05:43 PM - edited May 26 2018 05:44 PM
Please ZIP and share %windir%\Logs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2018 07:13 PM
Navjot,
Thank you for the suggestion. I have emailed Darrell the Windows\Logs folder as well as Windows.old\Windows\Logs.
Mark Berry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 29 2018 06:26 AM
Is there any News available.
I have set a Policy to my Clients that they dont check the MS Update Websites in order to stop the deployment. But this will lead to a lack of security. I want to use the normal semi annual channel with the acutal Build (1709 and not 1803) and defer the Installation like offered in the Policy. I have also set the telemetry to value 0 which is the same like 1 for Enterprise users.
Many thanks for any Feedback.
Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 29 2018 10:44 AM
The one set of logs showed RS4 was available prior to the machine joining WUFB with the deferral policy.
Send me the logs or make them available for download please
Thanks,
Darrell
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 29 2018 11:15 AM
You don't want to set telemetry to 0 as that ignores the Windows update for business settings. If you use the don't use dual scan setting - and are behind WSUS you should be fine.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 05 2018 03:15 PM
SolutionMicrosoft updated the docs to make it clear, that when Telemetry is set to Zero, the deferral policies do not take affect and you make get the feature updates.
Here are the links to the updated Docs
https://docs.microsoft.com/en-us/windows/deployment/update/waas-overview
Important Devices on the Semi-Annual Channel (formerly called Current Branch for Business) must have their diagnostic data set to 1 (Basic) or higher, in order to ensure that the service is performing at the expected quality. If diagnostic data is set to 0, the device will be treated as if it were in the Semi-Annual Channel (Targeted)(formerly called Current Branch or CB) branch. For instructions to set the diagnostic data level, see Configure the operating system diagnostic data level.
https://docs.microsoft.com/en-us/windows/deployment/update/waas-configure-wufb
Note Users will not be able to change this setting if it was configured by policy. Important Devices on the Semi-Annual Channel (formerly called Current Branch for Business) must have their diagnostic data set to 1 (Basic) or higher, in order to ensure that the service is performing at the expected quality. If diagnostic data is set to 0, the device will be treated as if it were in the Semi-Annual Channel (Targeted)(formerly called Current Branch or CB) branch. For instructions to set the diagnostic data level, see Configure the operating system diagnostic data level.
Thanks
Darrell Gorter