- Home
- Microsoft Teams
- Teams Developer
- Misleading Error Message 53004
Misleading Error Message 53004
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 10 2020 11:01 AM
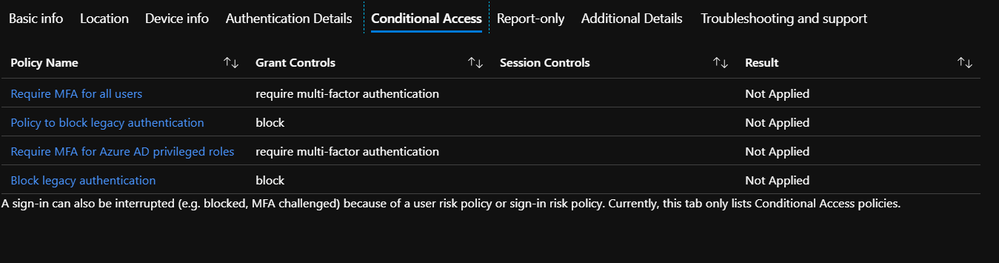
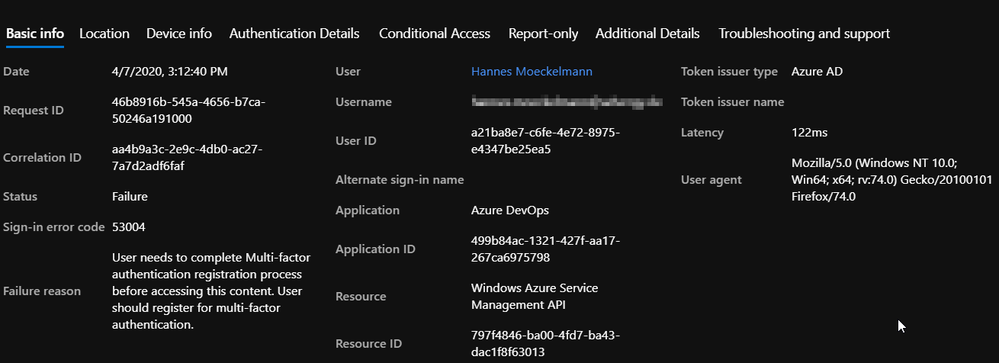
I wanted to document an issue I have spent a few months on (off and on) in hopes that the error messaging might be improved. The use case is that I can sign-in to Teams however, when I tried to switch orgs (guest access), I am seeing a "Your sign-in was blocked" error message on the screen with a body of, "We've detected something unusual about this sign-in."... I received the same experience when using the web app or the Teams client as well as both at work and at home. When I went into Azure, the failed authentication event said (example pasted at the bottom.) The actual issue was that there was an old unaddressed risky sign-in event that was never dismissed after it was addressed in August. Of course there is a business process gap however, if the both the user facing message and the Azure failed sign-in event had pointed me in the risky sign-in direction instead of an incomplete MFA registration I would have spent considerably less time trying to resolve this issue. I understand if this post needs to be redirected to a different group but I wanted to start by documenting it here to hopefully save someone else from burning their time and MS premier (though I did not actually find the resolution as a result of that ticket) hours on this.
- Labels:
-
Developer
-
Guest Access
-
Microsoft Teams
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 16 2020 09:48 PM
@Busted1942 Looking at the correlation id, the guest user was marked as High Risk by his home tenant and the solution is guest users home tenant should deflag that event.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 17 2020 04:50 AM
That is what the fix what. What can I read/learn to be able to decode correlation IDs like a pro as you seem to be able to?@Gousia_Begum
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2020 10:29 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2020 11:14 AM
Trigger a risky user sign-in event to show up for a test user in Azure Portal>Azure Active Directory>Security>Risk Detections and then try to change Orgs with that user in MS Teams.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2020 11:24 AM - edited Apr 16 2020 11:30 AM
thanks
i got other kind of issue, maybe i can shortly describe it.
external user(customer) cannot log in to our tenant (Teams/AzureDevOps) with his account.
when loggin in hes asked to provide MFA and so on. but he CANT - its not possible because he cannot login to set mfa..so we have a loop.
so i created another user in his tenant, logged into mine - works...so hes using this second account.
maybe you can advise me what to do...some users are asked to provide MFA some not.
in conditional access policy i have excluded external users
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2020 11:31 AM
Did you check risky sign-ins for an event with his username? Resolving the risky user sign-in was the resolution in my case when there was no other clues on where to look. You can find that under Azure Portal> Azure Active Directory> Security> Risky users...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 20 2020 06:14 AM
You are experiencing the same frustration I did and are being mislead by the same error message in my opinion. In my case, it was the account in my tenant trying to auth as a federated user into another tenant that triggered that error message, again, in my source tenant. When you checked for risky sign-ins, did you check in the user's source (Federated or guest) Tenant if they had a risky sign-in event or were you checking in your tenant where you are trying to share the resources from?
If you don't see a risky sign-in event in either tenant, I am not sure what else might be going on and my next step would be to open a support ticket. Again, where it me, I'd open it as an Azure auth incident be prepared for the likely hood of being bounced around from support group to support group for a month or two as you stay on top of them, not allowing them to close the incident and escalating as needed. It took me months to resolve this for our Tenant but I eventually got to a person who knew enough to give me a few clues to resolve it for myself.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 08 2020 03:29 PM
A thought occurred to me this week, could you have "Include Unknown Areas" checked in your named region? That could cause some traffic to fall into an unexpected conditional access policy.