- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- How to operationalize Microsoft Secure Score in your organization
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
With the public preview of Microsoft Secure Score now well under way we’ve received a ton of feedback and one of the things we’re consistently hearing is that the new features designed to help organizations:
- Better assess their current security posture
- Plan, implement and monitor their posture improvements
- Drive meaningful status and planning discussions with leadership
are exactly what our customers wanted us to prioritize for the next release. Another thing we’re hearing feedback on is that our customers need help operationalizing Microsoft Secure Score and making it part of their daily walk of life. We actually did a session on this very topic as Ignite 2019 but with recent chatter on the subject we thought now would be good time to provide a written version of the content.
When we created the session for Ignite we knew organizing the session around a Crawl, Walk and Run analogy would prove easiest for customers with varying levels of expertise, budget, etc. We also knew that this story could best be told by someone with hands experience and so we brought in one of one of our MVPs, Michelle Gilbert, who had successfully operationalized Microsoft Secure Score in some of the world’s largest and most regulated organizations. Full transparency, we later hired Michelle as a result of her great work here and in other areas!:)
Crawl - Starting the conversation
Before we get into the details on how to successfully implement a Crawl stage program it’s important to understand the Crawl stage goals which are:
- Ensure leadership and all stakeholders are aware of the importance and benefits of an ongoing security posture improvement program
- Receive a commitment from the team to implement some of the low hanging fruit Improvement Actions (i.e.: low complexity, low impact)
Summary of tasks
Here are the key tasks you will complete during the stage:
- Identify all the organization’s stakeholders
- Educate your stakeholders on security posture management and Microsoft Secure Score
- Develop plan of action to improve your security posture with a small set of easy improvements
How to make it happen
When you begin your journey towards operationalizing Secure Score you should treat it like a program that will not have an end date, and one that will continue and evolve over time. In this stage you will work on transitioning your organizations approach to security to a state where security posture management is becoming a top priority and implementing an ongoing program is on its way to mission critical status.
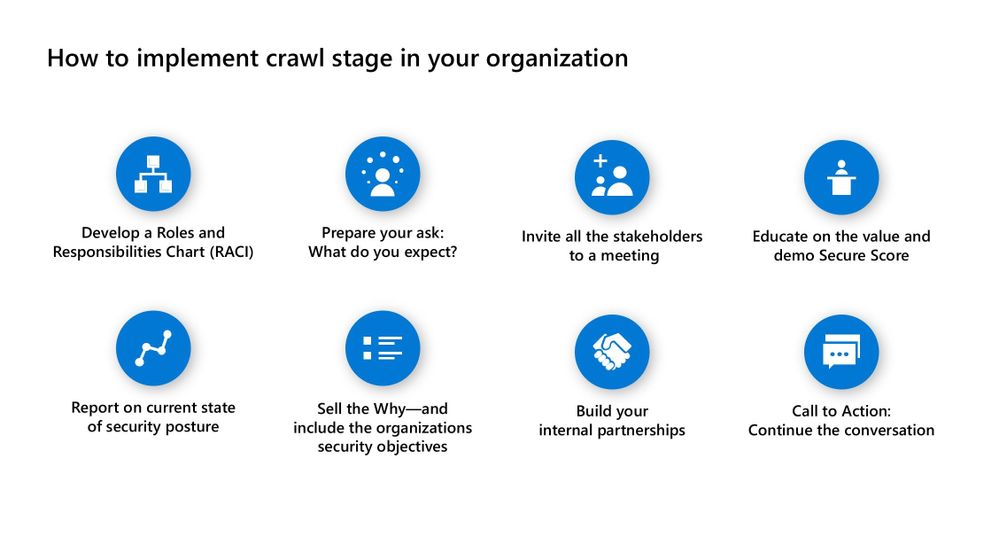
This type of project can’t be done alone so you must plan out who should be involved in the fight. You can call it a security committee, a board, or even task force team. Whatever you decide upon as a name is your call but keep in mind it will take time, commitment and tenacity to make the team productive. Like many new teams that you start, you should first develop a roles and responsibilities chart (RACI). This will help you identify who is responsible (assigned to or tasked), accountable (decision maker), consulted (other stakeholder or subject matter expert), and informed (dependent). Identifying the stakeholders is key to ensuring you have all the right people seated at the table and that they acknowledge their responsibility within the group. The team may include stakeholders from around your organization that are in charge of areas such as identity, data, apps, devices and infrastructure.
Once you have identified everyone, now you should prepare your ask. What do you expect from them in terms of time and commitment? This might be a monthly or bi-monthly commitment of time to review the latest threats in the market, security projects and of course your Microsoft Secure Score. At this point, the goal here is to get everyone in the room and gain buy-in. Invite your stakeholders to a meeting and educate them on the value of Microsoft Secure Score by walking them through all of its key experiences.
Next show them your organizations current security posture across each of the categories and then sell them on the Why! The Why can best be sold when you show how your organization’s existing security objectives can be met or even exceeded by using Microsoft Secure Score. Show the security teams a few low-cost and low complexity Improvement Actions that map to their goals and get them to commit to investigating or better yet implementing them. Next develop enthusiasm around how Microsoft Secure Score can be one of their best guides to achieving better security and then discuss how to build out the internal partnerships to implement the posture improvements. The final step in the Crawl stage is to provide a call to action and that’s to: Continue the Conversation. Ask for another meeting with the stakeholders to review their Microsoft Secure Score more thoroughly, follow up on the low cost and complexity Improvement Actions you identified at the first meeting, and to look for additional opportunities to further improve.
Challenges you’ll face
As you attempt to complete the Crawl stage you will encounter a series of key challenges including:
- Establishing committed long-term ownership
- Producing partnerships that are motivated to ensure results
- Culture change that recognizes posture management can be one of the most productive security projects
When it comes to ownership building a RACI document can be very helpful but actually identifying the owners can be difficult in large organizations and then in small organizations you may find extremely busy resources that are resistant to adding more work to their plates. Proactively fighting security threats requires culture change and it may require senior leadership to sponsor the initiative. To convince them join the fight here is a statistic I’m sure they’ll react well to: 93% of all breaches are preventable (Online Trust Alliance).
Walk - Building a long-term plan
When you complete the Crawl stage you should have developed a fair amount of awareness and possibly you’ve landed your first wins with the implementation of some low cost and complexity posture improvements. When you transition to the Walk stage you’ll establish your effort as ongoing project.
Your goal
In this stage your primary goal will be to build out a broader long-term plan focusing on higher stack ranked Improvement Actions.
Summary of tasks
Here are the key tasks you will complete during the stage:
- Assess organizations secure score and start to understand the posture you should strive for
- Build a prioritized list of Improvement Actions whose feasibility should be investigated
- Raise awareness of all high priority security gaps
- Develop an ongoing meeting cadence
How to make it happen
Implementing the Walk stage in your organization requires deeper more meaningful participation from the critical stakeholders as they will help you build out and execute the long-term plan. Invite them to a meeting with an agenda that includes specifics tasks that will be completed together during the session. These tasks will include getting a better understanding of your organizations secure score and identifying high value improvement actions to improve it. This process may take several meetings.
One of the questions customers constantly ask us is “What’s the right score for my organization?”. Sadly, the answer is “It depends.”. First, some Improvement Actions are not a good fit for all organizations. For instance, if you have apps that require the use of legacy protocols, you’re probably not going to be able to implement the “Disable Legacy Protocols…” Improvement Action. Second every organization is constrained by time and resources and many organizations will simply be unable to implement all of the viable options. Based on this, the reality is that most organizations are never going to reach anything near a 100% score.
Given this reality we think one of the best ways to understand the quality of your score is to compare it against other organizations. You can do this by going to the Comparison Card on the Microsoft Secure Score Overview page. From here you can compare your score against organizations that Microsoft thinks are most like yours (based on industry, size, licensed products) or you can do a custom comparison based on any industry, organization size, licenses or regions that you choose. With this comparison data you can decide for yourself whether your score is good, bad, or somewhere in between and the level of improvement you should be targeting.
Once the team is acclimated with the score and has developed a point of view on its quality it’s time for the team to do a thorough review of all the Improvement Actions to see where improvements should be made. During this part of process, you will walk through each Improvement Item one by one and edit their status. The status options are: To address; Planned; Risk accepted; and Resolved through third party.
You can update the status of an Improvement Action by clicking the Edit status and notes button from the Improvement Action’s details page. For each improvement action the team feels could be addressed within the next quarter mark them as “Planned”. For those that are more of a long-term goal leave them set as “To Address”. For those that you know you’re not going to be addressed within the next 12 months due to complexity, effort level required, cost, etc mark them as “Risk accepted”. Finally for any Improvement Action where the requirements are satisfied by a 3rd party solution mark these as “Resolved by third party”.
At the end of the Walk stage you will have effectively created an action plan that is baked into the tool and now you can begin improving your organization’s posture. To start this process, use the Share button on the Details page of each “Planned” Improvement Action to assign tasks to those who will own driving the implementation. The Share feature will enable you to create these tasks directly within Microsoft Planner or ServiceNow. In addition, the Share button can be used to initiate discussions within Microsoft Teams.
At this point all the stakeholders should have sense of the score they should be working towards, ownership should be well established and everyone should have a clear view of the security gaps exposed by unimplemented Improvement Actions. The next call to action is to ask the owners to commit to the longer-term effort where they will:
- drive their teams to implement the agreed upon Improvement Actions
- implement the improvements on a schedule
- commit to participating in ongoing meetings to keep the effort moving forward
- repeat the process
Challenges you’ll face
As you attempt to complete the Walk stage you will encounter a series of key challenges including:
- Identifying subject matter experts for some Improvement Actions can be difficult
- Resource commitments will be harder to come by as they will require longer reoccurring efforts
In the Walk stage you may find your organization lacks the expertise necessary to investigate and implement various Improvement Actions. The reality here is that you’ll just need to ramp up the team with training. In addition, because resources are always tight it may be hard to get team to prioritize new long-term projects. You’ll need to find creative ways to help ensure that the value of posture improvement is truly understood relative to other priorities. Showing teams, the attack vectors Improvement Actions can eliminate is a good way to approach this type of conversation.
Run - Embedding in your culture and making it a machine
When you complete the Walk stage, you’ll have a security posture improvement project that is in motion and making a difference. The project is still new and for the team it may still feel like a non-recurring motion. Here in the Run stage you’ll make posture improvement part of the organization’s DNA.
Your goal
In this stage your primary goal will be to update the plan over time and to use leadership oversight and accountability to maximize results.
Summary of tasks
Here are the key tasks you will complete during the stage:
- Review new Improvement Actions added to the tool
- Review previous decisions and see if the bar can be raised
- Hold the line on posture improvement gains
- Provide visibility to Executives and use them to drive accountability
How to make it happen
After you have begun executing your Walk stage plan you might feel like you can see an end to the project but the reality is it’s really just the beginning. On a quarterly basis you should check Microsoft Secure Score specifically for new and updated Improvement Actions. Each of these should be vetted and the current plan should be adjusted accordingly on a priority basis.
In addition, as the existing plan is executed your Improvement Action backlog will decrease in size making Improvement Action that once felt tactically unachievable something you could now consider. You should periodically review Improvement Actions marked “To Address” and “Risk Accepted” to see if upcoming capacity will enable them to be prioritized and added to your plan.
If you are designated as the posture management lead for the project, monitoring your status is a critical responsibility. To help you monitor your environment we have an Actions to Review Card that you can use to identify and remediate posture regressions. We recommend you monitor this space frequently as even a well configured organization tend to drift away from their desired state.
At some point in the Run stage you will want to make security posture management part of your leadership team’s walk of life as well. To do this you will develop a communication plan to roll out periodic status information to executives and leadership. From here you should find a means to inject posture management as a regular agenda item in recurring leadership level discussions.
Status emails and discussions with leadership can easily be organized around the information on the Cards on the Metrics and Trends report.
To demonstrate your progress, the Score changes card will prove even more interesting than the secure score itself. For instance it can help explain why your score dropped even though you may have been making great progress on your plan (e.g.: you scored 50 points this week per the plan but Microsoft added another 100 points worth of improvement actions to the system causing your secure score to decrease). There are three types of changes that are tracked in this space including:
- Points achieved (a reflection of work the team has recently accomplished)
- Points regressed (point loss due to configuration changes)
- New actions added (negative score impact due to new IAs being added).
You may also report on the secure score itself, but keep in mind there is a balance between usability and security so 100% isn’t necessarily the goal you should be striving for. A preferred method is to set up a projected score based on the Improvement Actions you’ve marked as Planned and then to setup custom zones that represent what Good and Okay scores are. We recommend you set Okay to be equal to the minimum bar your organization can accept risk wise and for Good to be what your team has decided is the right score based on a combination of baseline data and the threats your organization is facing.
Now that you’ve done these things repeat the process and try and do quarterly reviews with leadership.
Challenges you’ll face
As you attempt to complete the Run stage you will encounter a series of key challenges including:
- Some Improvements Actions requires significant work and resource commitments leading to full-on projects
- Its critical leadership understands the numbers nuances behind Secure Score. Break their thinking that 100% is a goal as its unattainable.
Wrapping it up
So, there you have it a white paper length blog that shows you how to make security posture management part of the DNA of your organization. We hope it provides the guidance you need to successfully implement it within your own organization. To start taking advantage of the latest public preview go to: http://aka.ms/securescorepreview. More information Microsoft Secure Score can be found at Microsoft Docs (Microsoft Secure Score).
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.