- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Conditional Access policies for Azure Information Protection
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Oct-2023 update: This blog does not have the latest information on Conditional Access, See the updated doc on Conditional Access policies and encrypted documents for more information.
First published on CloudBlogs on Oct 17, 2017
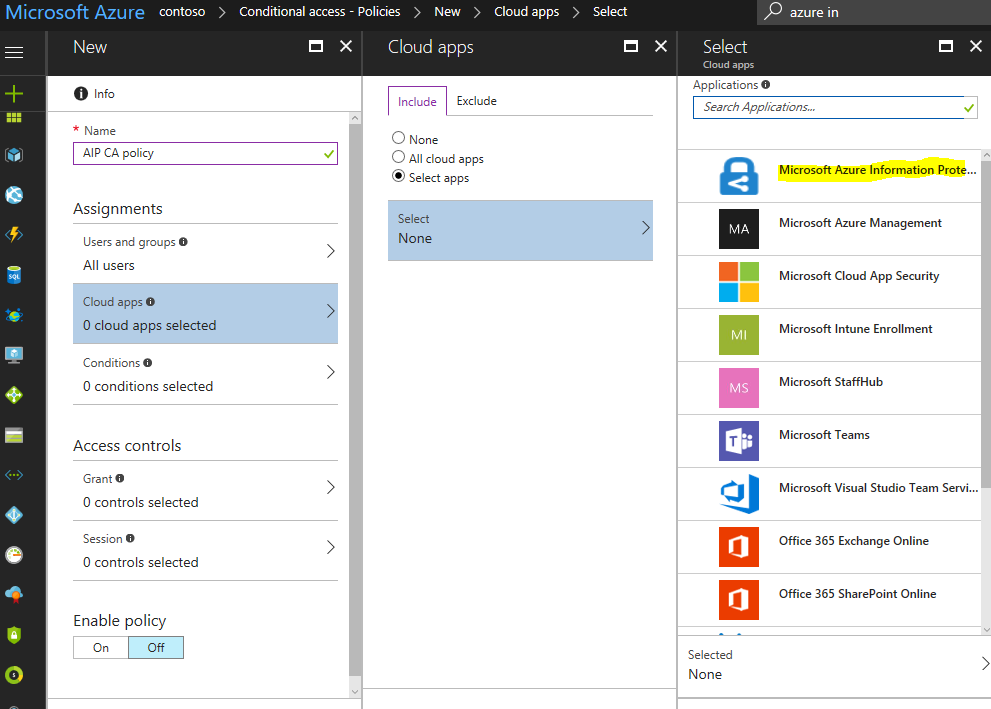
Hopefully, you saw at Ignite the awesome new set of capabilities that are coming with Azure Information Protection. Following up from the announcement that we would have a public preview of Conditional Access, we wanted to provide some more information about how this works and how you can quickly get started today! The preview of Conditional Access for Azure Information Protection (AIP) enables admins to configure conditional access policies help secure access to sensitive information.
How will this work?
Below is a list of some common scenarios that light up when conditional access policies are enabled for AIP-protected content:
- Require Multifactor Authentication : Enforce an MFA challenge to access AIP protected documents. This can help protect against the risk of stolen and phished credentials.
- Device compliance/Domain Joined : Allow access only if the user device is domain joined and/or is compliant as per company MDM/MAM policy (device compliance policies are configured in Intune).
- Risky-Sign in : Block access to sensitive content when a user has either High, Medium or Low likelihood of risky-sign in (i.e sign-in attempt was not performed by the legitimate owner of a user account).
- Trusted network : Block access when the user is not at work. In other words, you require access to sensitive content to be only from a network you trust.
Admins can now configure conditions and controls in the Microsoft Azure portal . Let’s walk through an example for each of these to help you in your thinking.
Figure 1: AIP now supports Conditional Access in Azure portal
Example 1: Require MFA to access AIP protected content
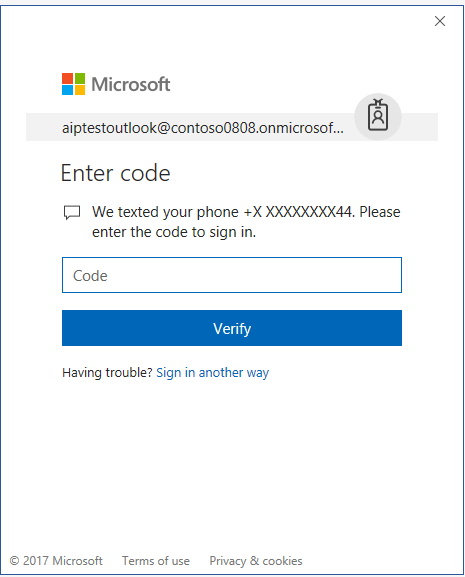
Let’s say your tenant admin has configured a Conditional Access policy such that all users require multi-factor authentication when accessing AIP protected documents on the Windows platform as shown below.
Figure 2: MFA control enforced here
Figure 3: Conditions can be platform specific
In this scenario, end users will receive an MFA challenge after entering their username/password when opening AIP protected document in Word on a Windows 10 PC. Note: MFA challenges are authentication level. This means users will not be prompted for MFA when opening protected content using other Office applications like Excel, PowerPoint on the same machine given they have done MFA already in Word. Also, if a user had to do MFA as part of their Windows login (either as part of first time MFA setup and/or first-time login to PC) they will not be re-prompted inside the applications.
Figure 4 MFA prompt inside Office applications
Figure 5 MFA prompt inside AIP iOS app
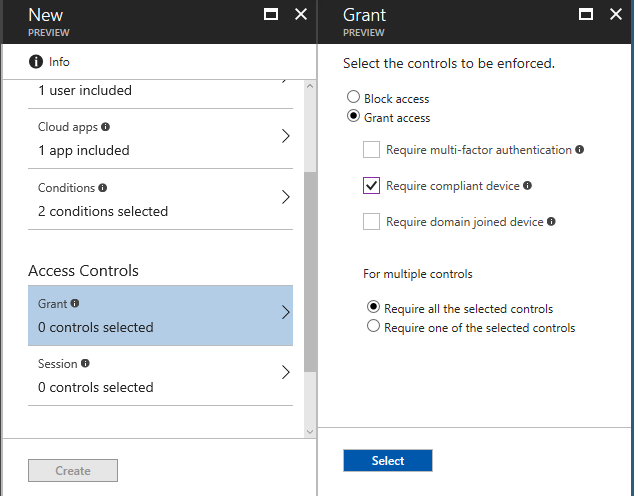
Example 2: Require a compliant device to access AIP protected content from mobile devices
Now imagine your tenant admin has configured Conditional Access policy such that some users (e.g. contractors in your company) require compliant devices when accessing AIP protected documents on mobile platforms.
Figure 6 ‘Require compliant device’ control applied
The admin also needs to configure device compliance policy in the Intune blade as shown below. In this example scenario, the admin has configured system security settings like ‘Require a password’ and ‘Min password length’. For details on device compliance policies and how to create them, check out the detailed blog post from the Intune team .
Figure 7: Device compliance policies created for different platforms in Intune blade
Once the device compliance policy is deployed, each device is checked for compliance as part of AIP app’s sign-in flow when opening protected files.
Figure 8 Error dialog in AIP Windows app when device is not compliant
Note: Users will be prompted to install application(s) like Intune company portal to verify compliance. Read this documentation for more information .
Example 3: Block Access to AIP protected content if user is not on a trusted network
As shown below, as an admin you can configure a policy such that users are blocked from accessing AIP protected content from a network location you don’t trust.
Figure 9 Trusted network policy enabled
The location is identified by the IP address of the client you have used to connect to Azure Active Directory. This condition requires you to be familiar with named locations and MFA trusted IPs .
Example 4: Block access to sensitive content when user has risky sign-in
As shown below admin can configure a conditional access policy such that users with ‘High’ risk sign-in will be blocked from accessing AIP protected content.
Figure 10 Sign-in risk level as condition in a conditional access policy
Special considerations for external users
Azure Active Directory Identity Protection can help you detect risky events in your organization.
Conditional Access policies, when applied to users external to your tenant, require that those users authenticate to your organization using a guest account for Azure AD B2B collaboration since options such as Multifactor Authentication need to be associated with such an account. In the absence of a guest account, the user will receive an error indicating they cannot be authenticated to access the content. If you think it is safe to assume that external users that will be granted access to protected documents will have such accounts provisioned ahead of time by your organization, then you can safely enable Conditional Access policies with Multifactor authentication for Microsoft Information Protection with a scope of all users internal or external to the organization. But if it is likely that this will not be the case for all external users (e.g. if your employees might be sharing sensitive documents in an ad-hoc fashion by granting external users permissions via labels with user-defined permissions without knowing whether those users have guest accounts provisioned) then we would recommend that you exclude external users from the Conditional Access policies by either selecting specific internal users and groups, or selecting the All users option and excluding all guests and external users.
For Conditional Access policies that involve device state options, external users must also be excluded.
For any updates and additional information on conditional access policies, see our FAQ for conditional access . As always, we’re looking forward to your feedback. Prerequisites: Azure Active Directory Conditional Access is a feature of Azure Active Directory Premium . Each user who accesses an application that has Conditional Access policies applied must have an Azure Active Directory Premium license.
Get started NOW!
It really is very easy to get started. We have a lot of information available to help you, from great documentation to engaging with us via Yammer and e-mail. What are you waiting for? Get to it!
- Download the Azure Information Protection client from our Download Center
- Start a trial and kick the tires
- Learn more about Information Protection
- Get deep technical and scenario documentation
- Vote on the User Voice forum to help us understand your priorities
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.