- Home
- Security, Compliance, and Identity
- Microsoft Defender for IoT Blog
- Azure Defender for IoT is now in public preview
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Summary: Agentless security for unmanaged IoT/OT devices
As industrial and critical infrastructure organizations implement digital transformation, the number of networked IoT and Operational Technology (OT) devices has greatly proliferated. Many of these devices lack visibility by IT teams and are often unpatched and misconfigured, making them soft targets for adversaries looking to pivot deeper into corporate networks.
Business risks include financial losses due to production downtime, corporate liability from safety and environmental incidents, and theft of sensitive intellectual property such as proprietary formulas and manufacturing processes.
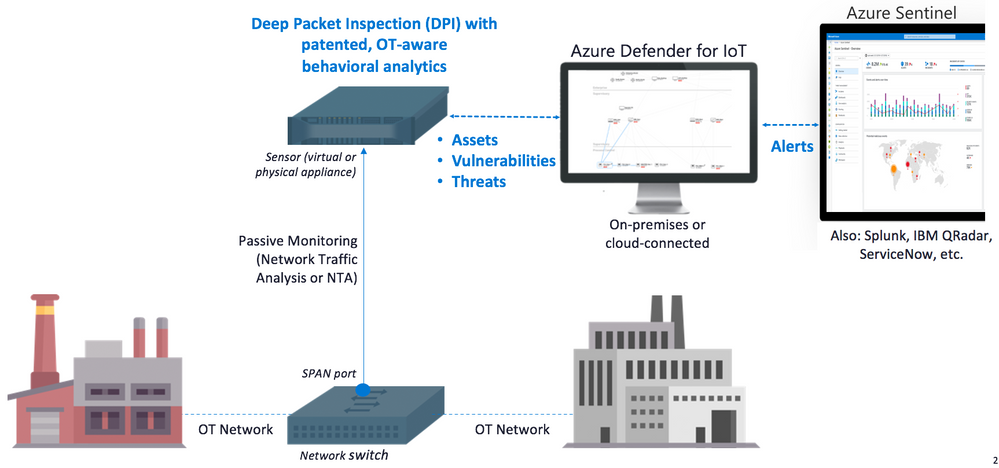
Incorporating agentless, IoT/OT-aware behavioral analytics from Microsoft's recent acquisition of CyberX, the new version of Azure Defender for IoT addresses these risks by discovering unmanaged IoT/OT assets, identifying IoT/OT vulnerabilities, and continuously monitoring for threats.
These new capabilities are now available in public preview for on-premises deployments, with the option of connecting securely to Azure Sentinel to eliminate IT/OT silos and provide a unified view of threats across both IT and OT environments. It also integrates out-of-the box with third-party tools like Splunk, IBM QRadar, and ServiceNow.
Introduction
Announced at Ignite 2020, Azure Defender for IoT delivers agentless security for continuously monitoring OT networks in industrial and critical infrastructure organizations.
You can deploy these capabilities fully on-premises without sending any data to Azure. Or, you can deploy in Azure-connected environments using our new native connector to integrate IoT/OT alerts into Azure Sentinel, benefiting from the scalability and cost benefits of the industry’s first cloud-native SIEM/SOAR platform.
Microsoft offers a number of end-to-end IoT security solutions for managed (or “greenfield”) IoT deployments, including Azure IoT Hub, Azure Sphere and micro-agents for embedded operating systems. However, most of today’s IoT/OT devices are “unmanaged” because they do not get provisioned, are not monitored, and lack built-in security such as agents or automated updates.
As a result, most IT security organizations have limited or no visibility into their OT networks. What’s more, these devices are often unpatched and misconfigured, making them soft targets for adversaries looking to pivot deeper into corporate networks.
Network security monitoring tools developed for IT networks are unable to address these environments because they’re blind to specialized industrial protocols (Modbus, DNP3, BACnet, etc.). They also lack an understanding of the specialized device types, applications, and machine-to-machine (M2M) behaviors in IoT/OT environments.
Key capabilities
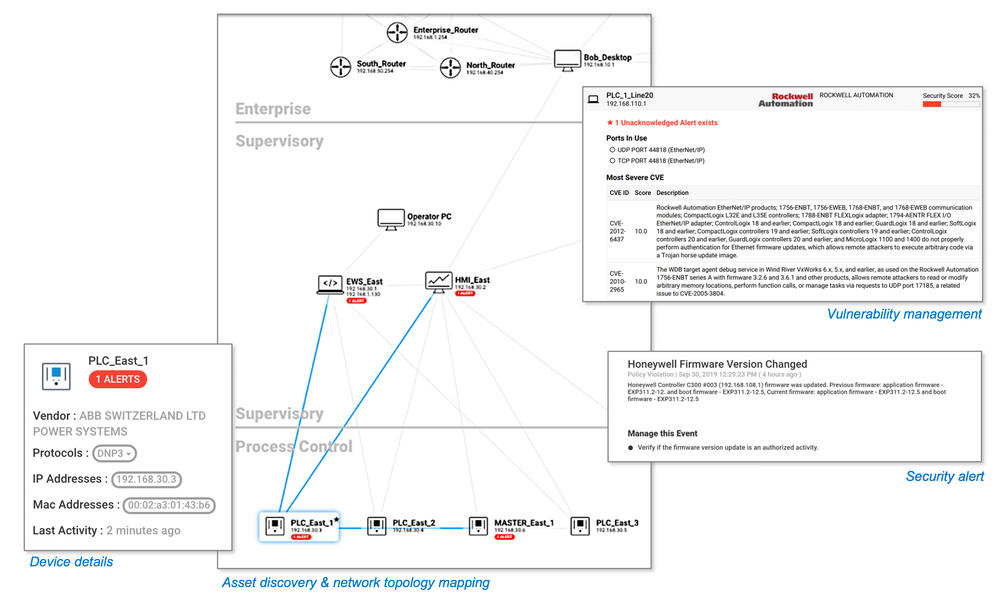
Azure Defender for IoT enables IT and OT teams to auto-discover their unmanaged IoT/OT assets, identify critical vulnerabilities, and detect anomalous or unauthorized behavior — without impacting IoT/OT stability or performance.
Azure Defender for IoT delivers insights within minutes of being connected to the network, leveraging patented IoT/OT-aware behavioral analytics and machine learning to eliminate the need to configure any rules, signatures, or other static IOCs. To capture the traffic, it uses an on-premises network sensor deployed as a virtual or physical appliance connected to a SPAN port or tap. The sensor implements non-invasive passive monitoring with Network Traffic Analysis (NTA) and Layer 7 Deep Packet Inspection (DPI) to extract detailed IoT/OT information in real-time.
You also benefit from out-of-the box integration with third-party IT security tools like Splunk, IBM QRadar, and ServiceNow. Plus, it’s designed to fit right into existing OT environments, even across diverse automation equipment from all major OT suppliers (Rockwell Automation, Schneider Electric, GE, Emerson, Siemens, Honeywell, ABB, Yokogawa, etc.).
Integration with existing SOC workflows is key to removing IT/OT silos while delivering unified monitoring and governance across both IT and OT. To help automate this complex security challenge, we’ve also beefed up Azure Sentinel with IoT/OT-specific SOAR playbooks and threat intelligence.
Combined with previous support in Azure Security Center for IoT for protecting managed IoT/OT devices connected via Azure IoT Hub, these new capabilities enable organizations to accelerate their digital transformation initiatives with a combined solution for both unmanaged and managed devices.
Rapid non-invasive deployment leveraging patented IoT/OT-aware behavioral analytics, available either for on-premises or Azure-connected environments.
Real-time OT threat alerts provided by Azure Defender for IoT (examples)
- Unauthorized device connected to the network
- Unauthorized connection to the internet
- Unauthorized remote access
- Network scanning operation detected
- Unauthorized PLC programming
- Changes to firmware versions
- “PLC Stop” and other potentially malicious commands
- Device is suspected of being disconnected
- Ethernet/IP CIP service request failure
- BACnet operation failed
- Illegal DNP3 operation
- Master-slave authentication error
- Known malware detected (e.g., WannaCry, EternalBlue)
- Unauthorized SMB login
Azure Defender for IoT provides holistic IoT/OT security including asset discovery, vulnerability management, and continuous threat monitoring, combined with deep Azure Sentinel integration.
Try it now at no charge
Try Azure Defender for IoT during public preview. This version includes the agentless security provided via the integration of CyberX, plus the ability to connect to Azure Sentinel. And please give us your feedback in the IoT Security Tech Community.
Learn more with these educational resources
- Watch our Ignite session showing how Azure Defender for IoT and Azure Sentinel are combined to investigate multistage attacks that cross IT/OT boundaries, using the TRITON attack on a petrochemical facility as an example.
- Watch our Tech Community webinar describing MITRE ATT&CK for ICS, an OT-focused version of the well-known MITRE ATT&CK framework originally developed for IT networks.
- Watch our SANS webinar featuring the head of Microsoft’s datacenter security program, about securing building automation systems using continuous OT security monitoring.
- Stay tuned for an upcoming webinar during which we’ll do a technical walkthrough of how to deploy and use Azure Defender for IoT.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.