- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Staying ahead of modern-day attacks Part 2: Defense-at-Scale approach with Office 365 ATP
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
In part 1 of this series, we reviewed the significant enhancements made to Office 365 Advanced Threat Protection (ATP) in recent months. In this blog, we’ll delve into the scale of threat signals leveraged by Office 365 ATP and highlight how that scale bolsters our ability to detect and protect against advanced threats quickly and accurately. Our strength of signal is one of the important elements helping Office 365 ATP provide the best security for emails, documents and collaboration. The foundation of Office 365 ATP is the Microsoft Intelligent Security graph which provides 6.5 trillion signals per day. This number is so large, it is hard to put into perspective but if you could analyze each of the 6.5 trillion signals at one signal per second, it would take roughly 200,000 years to analyze all the signals. With the power of machine learning, Exchange Online Protection (EOP) and Office 365 ATP do this analysis every day. Clearly, the information, learning, and intelligence gained from the Intelligent Security Graph is an impressive differentiator for our security services.
Office 365 ATP leverages these signals to detect malicious content faster and more accurately than any other service. We often reference the 400 billion emails analyzed by Office 365 every month which translates to more than 150,000 emails analyzed every second. Analyzing these emails provides trillions of signals that help our threat protection engines discern the good from the bad at a granular level, making the service agile and effective. Office 365 ATP has continued to improve even while the volume and sophistication of threats continues to escalate. Our approach to security has been so effective, currently, Office ATP has a malware catch rate greater than 99.9%. The rich data set helps fine tune our machine learning algorithms so that we can constantly enhance coverage for unknown and emerging threats in-real time.

Early detection of malicious content
Because of the volume of data analyzed every day; Office 365 ATP has better visibility into potential malware and phishing. The service can quickly identify suspicious content to protect users from a variety of malware and phishing attacks. For example, this malicious link was caught by Office 365 ATP only a few mins after it was launched. This phishing campaign tries to gather email account details of the recipients.

Note that while other engines had not yet detected the attack, Office 365 ATP flagged the URL as malicious early enough to protect users from clicking on it.

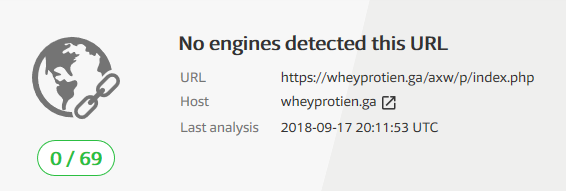
In another example, attackers were trying to trick users to provide their credentials. This type of phishing vector is rampant because gaining access to emails provides opportunities for attackers to access sensitive data or compromise other accounts owned by the victim.
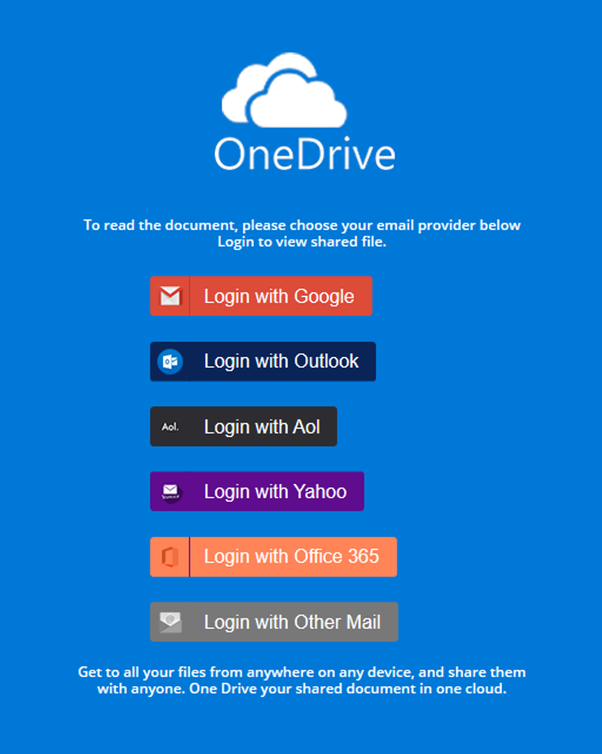 Figure 4. HTML page mimicking sign-in page for OneDrive
Figure 4. HTML page mimicking sign-in page for OneDrive
In this instance also, Office 365 ATP flagged it as malicious before any other engine was able to detect it.
Flagging suspicious content among a sea of legitimate content
Of the 400 billion emails analyzed by our threat protection engines monthly EOP and Office 365 ATP flag around 600 million email messages as malicious. That means only 0.0015% of all the emails analyzed are bad. Finding such a small fraction of malicious content among a sea of legitimate emails requires our engines to be smart and accurate. Office 365 ATP acquires that intelligence by learning from the huge amount of data that the Intelligent Security Graph provides. Such precision and granularity are also critical in accurately flagging malicious content and reducing false positives.
The detonation technology used to inspect attachments and links for malicious content also generates huge number of unique signals that can used to train our machine learning algorithms. These signals are shared across our services to improve the overall security posture and enhance their protection and detection capabilities.

The strength of signals that Office 365 ATP leverages makes it a powerful engine that provides intelligent detection and industry-leading protection against advanced attacks.
Experience Office 365 ATP
If you’re attending Microsoft Ignite, please join us to learn more.
- BRK4000 - Leveraging the power of Microsoft threat protection to secure the modern workplace across ...
- BRK4001 - Secure enterprise productivity with Office 365 threat protection services including EOP, A...
- BRK4002 - Securing your Office 365 environment from advanced phishing campaigns with Office 365 Adva...
- BRK2004 - The future of threat protection: Become efficient, cost effective, and more secure with Of...
- THR2037 Comprehensive threat protection for Office 365
- BRK3279 - So long and thanks for all the (email) phish
If you have not tried Office 365 ATP for your organization yet please begin a free Office 365 E5 Trial today and start securing your organization from the modern threat landscape.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
