- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity
- New Blog Post | What’s New: Azure Sentinel Update Watchlist UI Enhancements
New Blog Post | What’s New: Azure Sentinel Update Watchlist UI Enhancements
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Jun 16 2021
01:30 PM
- last edited on
Nov 03 2021
03:55 AM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 16 2021
01:30 PM
- last edited on
Nov 03 2021
03:55 AM
by
TechCommunityAP
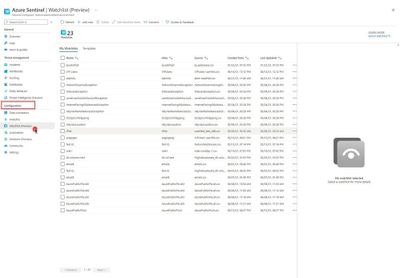
What’s New: Azure Sentinel Update Watchlist UI Enhancements - Microsoft Tech Community
Security operations (SecOps) teams need to be equipped with the tools that empower them to efficiently detect, investigate, and respond to threats across your enterprise. Azure Sentinel watchlists empower organizations to shorten investigation cycles and enable rapid threat remediation by providing the ability to collect external data sources for correlation with security events. Additionally, correlations and analytics help SecOps stay appraised of bad actors and compromised entities across the environment. Incorporating external data and performing correlation across analytics allows security teams to get a better view of their entire infrastructure and take steps to reduce risk.
Due to evolving and constant change in the cybersecurity landscape that we live in, it is very challenging for SecOps to stay appraised of new indicators of compromise.
Azure Sentinel Watchlists provides the ability to quickly import IP addresses, file hashes, etc. from csv files into your Azure Sentinel workspace. Then utilize the watchlist name/value pairs for joining and filtering for use in alert rules, threat hunting, workbooks, notebooks and for general queries.
Due to the constant change, security analysts need the flexibility to update watchlists to stay ahead. With that in mind, we are super excited to announce the Azure Sentinel Watchlist enhancements that empower security analysts to drive efficiency by enabling the ability to update or add items to a watchlist using an intuitive user interface.
- Labels:
-
Azure
-
Cloud Security
-
Microsoft Sentinel