- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity
- New Blog Post | Must Learn KQL Part 5: Turn Search into Workflow
New Blog Post | Must Learn KQL Part 5: Turn Search into Workflow
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 30 2021 07:44 AM
Must Learn KQL Part 5: Turn Search into Workflow – Azure Cloud & AI Domain Blog (azurecloudai.blog)
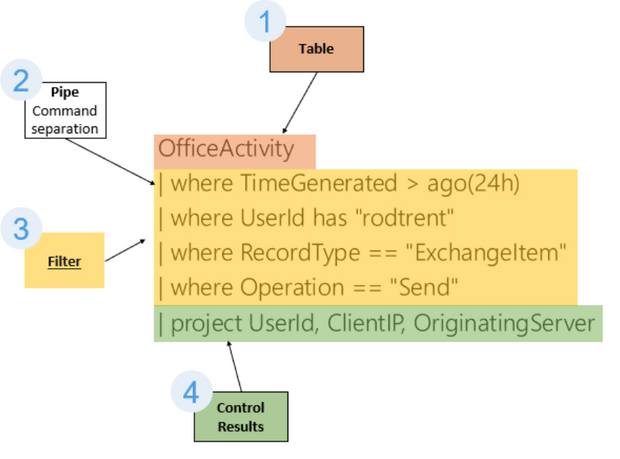
Now, that we’ve talked about using the Search operator in Part 4 to answer those three basic SOC analyst questions of: 1) Does it exist? 2) Where does it exist? and, 3) Why does it exist?, we can take that learning and the results of that type of query and meld it with the standard search query structure I talked about in Part 3.
In part 4, I ended with a query to locate activity by a user called “rodtrent“. I found that this rodtrent person had performed potentially strange activity in the OfficeActivity table (the table for Office 365 activity) that needs to be checked out. As shown, the search operator is a powerful tool to find things of interest. The results of the search operator query was thousands of rows of data. That’s inefficient.
So, now that we’ve found something interesting, we want to use the structure of the Search Query to pare down the results to minimize the effort and workload to identify that that something interesting is actually something notable and worth investigating.
- Labels:
-
Azure
-
Microsoft Sentinel