- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity
- New Blog Post | Hunting for OMI Vulnerability Exploitation with Azure Sentinel
New Blog Post | Hunting for OMI Vulnerability Exploitation with Azure Sentinel
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Sep 20 2021
10:16 AM
- last edited on
Nov 03 2021
04:04 AM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 20 2021
10:16 AM
- last edited on
Nov 03 2021
04:04 AM
by
TechCommunityAP
Hunting for OMI Vulnerability Exploitation with Azure Sentinel - Microsoft Tech Community
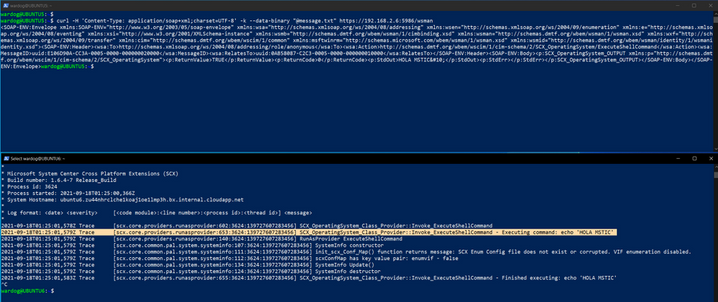
Following the September 14th, 2021 release of three Elevation of Privilege (EoP) vulnerabilities (CVE-2021-38645, CVE-2021-38649, CVE-2021-38648) and one unauthenticated Remote Code Execution (RCE) vulnerability (CVE-2021-38647) in the Open Management Infrastructure (OMI) Framework, analysts in the Microsoft Threat Intelligence Center (MSTIC) have been monitoring for signs of exploitation and investigating detections to further protect customers. Following the MSRC guidance to block ports that you aren't using and to ensure the OMI service is patched are great first steps. In this blog, we have some things to share about current attacks in the wild, agents and software involved, indicators for defenders to look for on host machines, and to share new detections in Azure Sentinel.
- Labels:
-
Azure
-
Cloud Security
-
Microsoft Sentinel