- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity
- Azure information protection custom policies not working
Azure information protection custom policies not working
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Jan 16 2018
02:50 AM
- last edited on
May 24 2021
02:02 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 16 2018
02:50 AM
- last edited on
May 24 2021
02:02 PM
by
TechCommunityAP
Hello,
I'm playing around with an Enterprise Mobility + E3 license and security and I was following the next tutorial/document from Microsoft: https://docs.microsoft.com/en-gb/information-protection/get-started/infoprotect-quick-start-tutorial
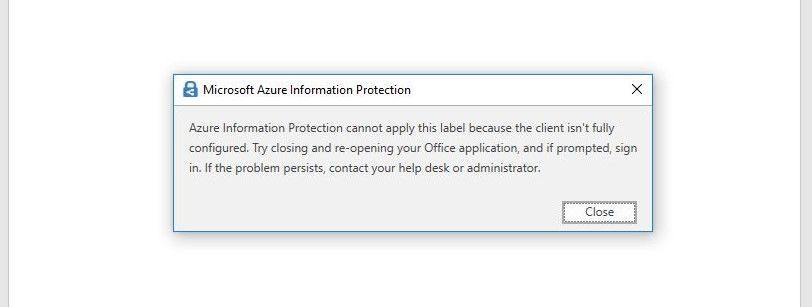
However, after completing every step the following error will pop up when trying to select a custom policy. I have tried creating different policies with different setups in vain:
I wonder what else is needed?
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 16 2018 02:12 PM
https://www.microsoft.com/en-us/download/details.aspx?id=53018
Select and run AzInfoProtection.exe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 02:14 AM - edited Jan 17 2018 02:17 AM
Hello Ortiz,
I'm afraid that didn't work, I originally used this installer by the way.
Looking at Microsoft's documentation, and as far as I know, it should be working as it is but I can't get it to work. Any ideas? Could something in the computer set-up be affecting the client?
Thank you for the help :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 02:35 AM
Please try the following to completely remove AIP client:
1. Uninstall AzIP client either in control panel or by running AzInfoProtection.exe /uninstall
2. Access Registry (RegEdit.exe) and delete: HKEY_CURRENT_USER\Software\Microsoft\MSIP
3. Clear IE cookies
4. Delete folder: C:\Users\<user name>\AppData\Local\Microsoft\MSIP
5. Clear Windows credentials and sign-out of Office account
6. Restart and run AzInfoProtection.exe again
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 04:05 AM - edited Jan 17 2018 04:15 AM
Thank you for that, unfortunately it still displays that error with custom policies.
I have had access to another device today and the very same error pops up there, so I'm assuming the problem must be in the setup.
EDIT: By the looks of it adding protection is causing the issue. The predefine policies which do not have protection activated (therefor are merely a visual thing) do work, however modifying them and adding protection "Azure (cloud key)" will cause this error to pop up.
Again, everything that is needed for this to work (according to the Microsoft documentation) has been done.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 04:51 AM
Ok then, please check requirements, mainly Office version required:
https://docs.microsoft.com/en-us/information-protection/get-started/requirements
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 05:02 AM
Do you have AD RMS enabled in your environment?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 05:33 AM
I'll get in touch with the provider and get it checked, I'll get back with an update regardless.
Regards,
Ion
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 06:09 AM - edited Jan 17 2018 06:16 AM
My apologies I did not see this post before, answering your question: No we don't, in fact, our Domain users are not linked in any way to those in Azure and 365.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 06:28 AM
Great. Are you able to right click a file in File Explorer and apply AIP protection (Classify and protect)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 08:04 AM - edited Jan 17 2018 08:06 AM
Hi,
If I try to apply the custom policy the following error will be displayed:
Failed: Rights management template not found
If I try to create a custom permission from the file explorer the following will be displayed:
Failed: Azure information Protection cannot apply this label because it encountered a problem trying to apply protection. If the problem persists, contact your help desk or administrator.
The predefined policies with no protection do work of course. I'll have a look at the first error which does look promising, if you have any thoughts about it however they're most welcome :)
Thank you for your help so far!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2018 08:16 AM
Good, I would check that Azure RMS Service and Templates in Azure portal, just to make sure everything is OK there. After that you can refresh templates on your machine following these steps:
https://docs.microsoft.com/en-us/information-protection/deploy-use/refresh-templates
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 18 2018 06:10 AM
Unfortunately I see nothing wrong with the templates. I wonder, is there anything within Office 365 setup that could be interfering with Azure RMS?
Only the firewall left to be check.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 18 2018 07:42 AM
I assume your Office 365 license supports Azure RMS, right?
If so, then most likely it's firewall or proxy blocking IPs or URLs like azurerms.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 18 2018 08:19 AM
Answering your question: Yes, we do have the needed licenses. I have also gone thru all of the requirements and setup again to make sure I haven´t missed something previously. I'll come back with an update (and hopefully a solution) to this post once the Firewall is sorted.
Again, thanks for the help!
Regards,
Ion
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 18 2018 04:20 PM
SolutionIn addition to checking the firewall isn't blocking IP addresses and URLs, check it's not terminating your TLS connection, which breaks certificate pinning. I've added a tip how to check for this client-side, if you don't manage the firewall yourself. See https://docs.microsoft.com/en-us/information-protection/get-started/requirements#firewalls-and-netwo...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 19 2018 01:42 AM - edited Jan 19 2018 06:24 AM
Hi Carol,
Spot on, the Microsoft certificate isn't displayed and in fact I can view a Fortinet message instead.
I also got a message from our vendor stating that they think something in the list might be performing packet inspections.
Once this is sorted I'll get back with more information to leave a record of it in case someone in the future runs into this post with a similar problem.
My most sincere thanks for all the assistance.
EDIT: The firewall was simply intercepting the SSL stream and replacing the certificate with its own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 19 2018 10:15 AM
Thanks for the update - really appreciate that, and also knowing that the newly added tip in the documentation worked for you. Hopefully, it will help the next person as well!
Firewall issues are always tricky to pin down, with unpredictable symptoms. Then the problem is compounded when you don't manage the firewall yourself and have to rely on others to check the requirements for you and make changes. This tip that was passed on to me (by Tom Moser in our Customer Success team) is a great way to either help eliminate this possible cause, or provide specific information to whoever manages your firewall.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 10 2018 05:47 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 05 2019 08:03 PM
Thanks for the info, this pointed me to my problem
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 18 2018 04:20 PM
SolutionIn addition to checking the firewall isn't blocking IP addresses and URLs, check it's not terminating your TLS connection, which breaks certificate pinning. I've added a tip how to check for this client-side, if you don't manage the firewall yourself. See https://docs.microsoft.com/en-us/information-protection/get-started/requirements#firewalls-and-netwo...