- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity
- Automatically Enable Azure Security Center Standard Tier for new Subscriptions
Automatically Enable Azure Security Center Standard Tier for new Subscriptions
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Nov 12 2018
02:00 PM
- last edited on
May 24 2021
02:35 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 12 2018
02:00 PM
- last edited on
May 24 2021
02:35 PM
by
TechCommunityAP
This article describes the steps for a scenario where Azure Security Center Standard tier needs to be automatically enabled for all new subscriptions. To enable this scenario the following components will be used:
- Azure Management Groups
- Azure Automation Account
- Azure Security Center PowerShell modules
In this scenario, all new subscriptions that are created under the Enterprise Management Group will automatically have Azure Security Center standard tier enabled:
The Azure automation account will be running every hour (it could be less according to your business needs) and if identifies a new subscription that has Security Center Free tier, it will upgrade to Standard.
Implementation steps
- In Azure Portal, click Automation Accounts.
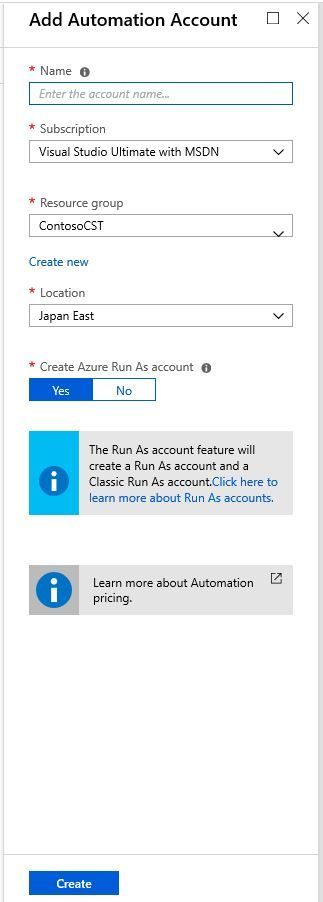
- Click Add and the Add Automation Account blade appears
- Type the name of the Automation Account, select the subscription, the Resource Group and the Location. Make sure the option Yes is selected under Create Azure Run As account and click Create button.
- The new automation account will appear in the list, click on it to edit.
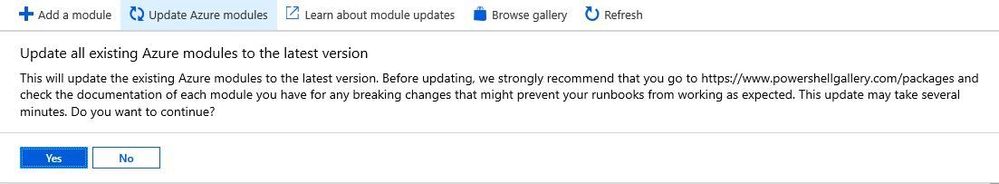
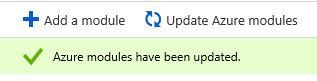
- Under Shared Resources section, click Modules and click Update Azure modules button.
- You may receive a warning like the one below, click Yes to proceed.
- Wait until you see the description that the modules were updated, as shown below:
- Open a new tab in your browser and navigate the following URL:
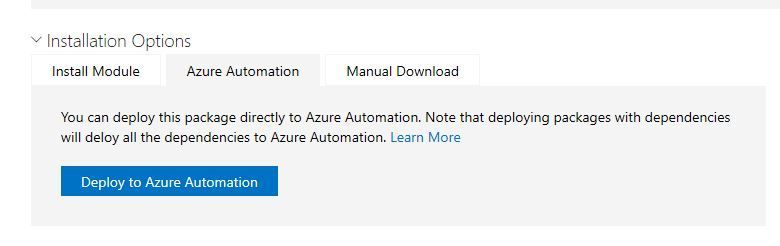
https://www.powershellgallery.com/packages/AzureRM.Security/0.2.0-preview
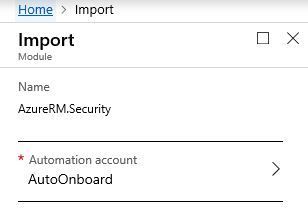
- Click Azure Automation tab and click Deploy to Azure Automation button.
- On the new blade that opens, under Automation Account option, select the Azure Automation Account that you are creating in this article:
- Click OK button, and once the OK button becomes gray out, close the blade.
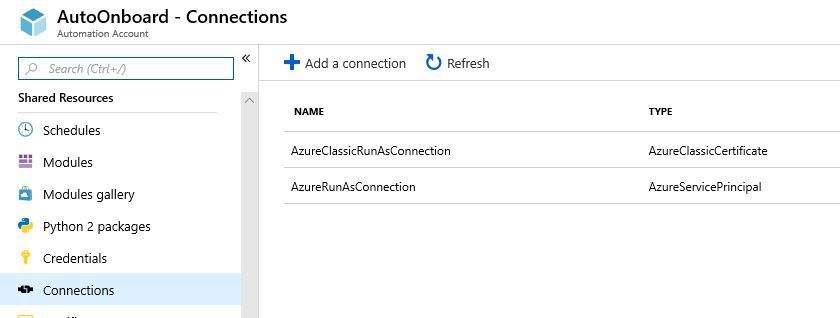
- Go back to the previous tab, where you have the automation account properties, and click Connections under Shared Resources section, and select AzureRunAsConnection:
- Copy the ApplicationID to the clipboard.
Note: this ApplicationID will be used later to provide the proper level of permission, which in this case is Security Administrator.
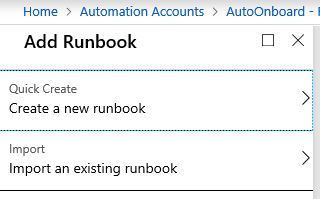
- Close this blade, and under Process Automation, click Runbooks.
- Click Add Runbook button and click Quick Create option.
- Under Name, type the name for this runbook, under Runbook type, select PowerShell and click OK button.
- Under the Edit PowerShell Runbook blade, type the code below:
$connectionName = "AzureRunAsConnection"
try { # Get the connection "AzureRunAsConnection " $servicePrincipalConnection=Get-AutomationConnection -Name $connectionName "Logging in to Azure..." Add-AzureRmAccount ` -ServicePrincipal ` -TenantId $servicePrincipalConnection.TenantId ` -ApplicationId $servicePrincipalConnection.ApplicationId ` -CertificateThumbprint $servicePrincipalConnection.CertificateThumbprint } catch { if (!$servicePrincipalConnection) { $ErrorMessage = "Connection $connectionName not found." throw $ErrorMessage } else{ Write-Error -Message $_.Exception throw $_.Exception } } #loop through all subscriptions Get-AzureRmContext -ListAvailable -PipelineVariable AzureRMSub | Set-AzureRmContext | foreach{ $tier = get-AzureRmSecurityPricing if ($tier.PricingTier -like 'Free') { Set-AzureRmSecurityPricing -Name "default" -PricingTier "Standard" } }
Note: after the Set-AzureRMSecurityPricing command, you can also add other commands to pre-configure some settings in Azure Security Center, such as the email contact. For more examples, read this blog post.
- Click Save button, and click Publish button
- Under Resources section click Schedules and click Add a schedule.
- Click Link a schedule to your runbook, click in the Schedule blade, and click Create a new schedule.
- In the New Schedule blade, under Name, type the name of the schedule, click Recurring button, and select the frequency that you want, and click Create button.
- In the Schedule Runbook blade, click OK, and close this blade.
At this point the Azure Automation account is created, the Runbook with the PowerShell script is configured, and the schedule is set. Now you need to grant Security Administrator permission to this account. Follow the steps below:
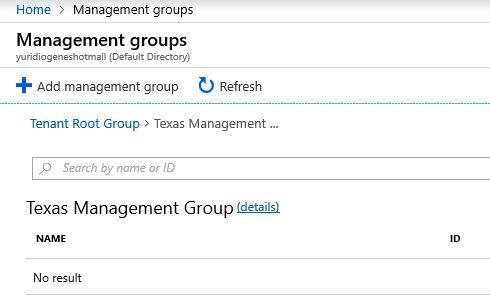
- In the Azure Portal, click All services, and type Management Groups.
- Click in the management group that will have the future subscriptions.
- Click details hyperlink besides the management group name.
- Click Access Control (IAM) option and click Add button.
- In the Add Permission blade, under Role, select Security Admin.
- Under select, type the name of the Azure automation account, and as you type, the account should appear. Click on it and notice that the account was added to the Selected members field.
- Click Save button.
- Confirm that the account appears as Security Admin rights as show the example below:
Authors
Yuri Diogenes, Senior Program Manager (CxE Security)
John Knightly, Senior PFE (Cybersecurity)
- Labels:
-
Security and Compliance Center