- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 28 2021 07:34 AM
Visual Studio 2019 16.11.5. WPF project .NET Framework 4.8. I can deploy via ClickOnce with a code signing certificate I purchased. When I add a Windows Application Packaging Project to my solution to create an MSIX and open the appxmanifest dialog, on the Packaging tab, I click "Choose Certificate..." and "Select from store...". The dialog says, "No certificate available". If I choose "Select from file...", choose the .pfx and enter the password, the dialog says, "The Manifest Desinger could not import the certificate. The certificate you selected is not valid for signing because it is either expired or has another issue. for more information see http://go.microsoft.com/fwlink/?LinkID=241478".
The certificate was purchased from SSL.com specifically for code signing and, as stated above, works for ClickOnce. The article above says this:
Validating Certificates
During packaging, Visual Studio validates the specified certificate in the following ways:
- Verifies the presence of the Basic Constraints extension and its value, which must be either Subject Type=End Entity or unspecified.
- Verifies the value of the Enhanced Key Usage property, which must contain Code Signing and may also contain Lifetime Signing. Any other EKUs are prohibited.
- Verifies the value of the Key Usage (KU) property, which must be either Unset or DigitalSignature.
- Verifies the existence of a private key exists.
- Verifies whether the certificate is active, hasn’t expired, and hasn't been revoked.
Inspecting the certificate through the certmgr mmc:
I don't see "Basic Constraints" in the certificate. Is that the problem? Do I have to specifically request this from SSL.com?
Enhanced Key Usage is set to "Code Signing (1.3.6.1.5.5.7.3.3)"
Key Usage is set to "Digital Signature (80)"
I'm not sure how to tell if a private key exists.
The certificate is active and not expired.
Please help. SSL.com swears we shouldn't need anything else. Self-signing is covered very well in documentation, but public certificates are barely mentioned.
Thank you,
Mike
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 29 2021 09:34 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 29 2021 09:55 AM
Thanks @TIMOTHY MANGAN Is it just me or does anyone else think it's nuts that there are no specs for public signing certificates for MSIX and that the tooling give you no indication of what's wrong when it doesn't work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2022 12:54 PM
@Mike_Yeager Hello Mike, I was wondering if you found a solution? I am facing the same issue and even though I shared my screen with the support staff of ssl.com while going through each step, they claim that the certificates are ok. I am missing Basic Constraints as well.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2022 01:17 PM
@itoinbgb Unfortunately no updates from Microsoft. It does work if you run the signing tools manually, but not through VS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2022 01:51 PM
Also be careful to re-review whatever instructions you have on which store to put that cert and what folders (or whatever they are called) within the store. Sometimes I've had to use the system store and sometimes the user store. Sometimes the Trusted Roots folder, and sometimes Personal.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2022 02:14 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2022 05:55 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2022 08:01 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2022 10:59 AM
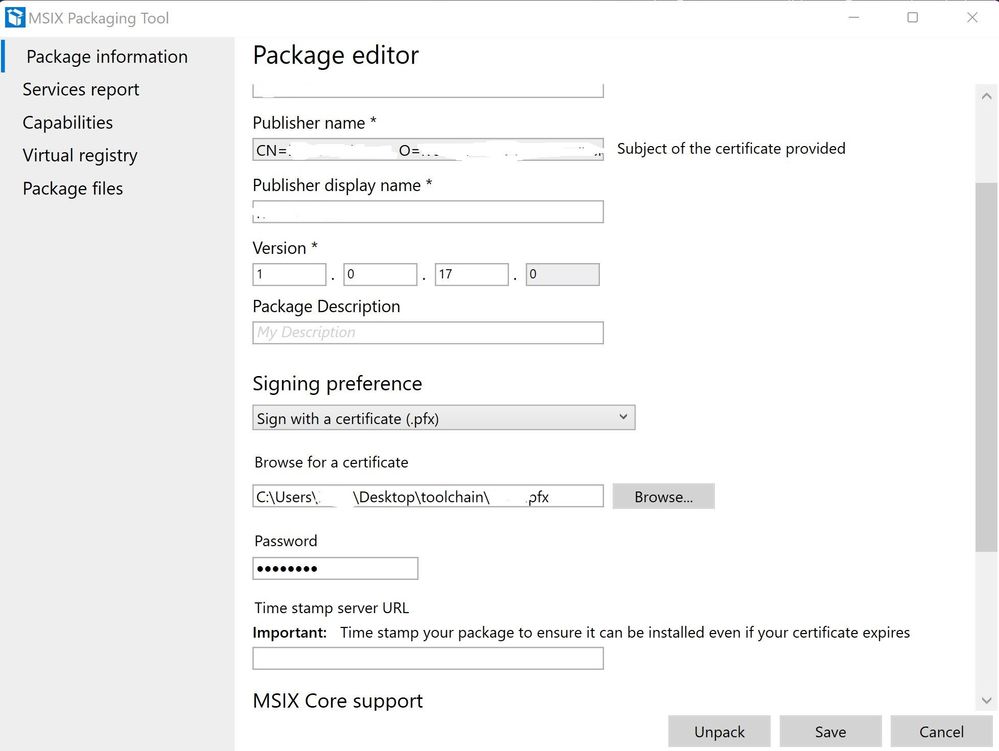
@Mike_Yeager I am using signtool as a workaround for msix bundles (appinstaller format), like this:
"C:\Program Files (x86)\Windows Kits\10\bin\10.0.22000.0\x64\signtool.exe" sign /fd SHA256 /tr http://ts.ssl.com /td sha256 /a /f "path_toCertificate\certificate.pfx" /p ******** "PathToPackage\Package.msixbundle"
This works fine for msixbundle, and for individual msix packages, I am using MSIX Packaging Tool:
I do hope this gets resolved eventually though, because this adds an additional step in the build process. Probably should buy another certificate from a CA that includes Basic Constraints.