- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 09 2020 08:03 AM
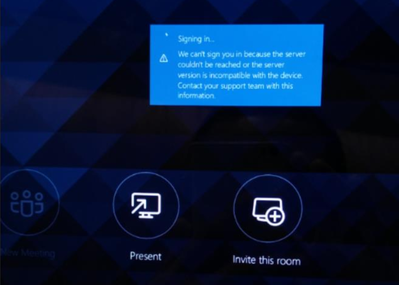
we can't sign you in because the server couldn't be reached or the server version is incompatible with the device
I receive this error to try to log in to an MTR, I manage to log in with a 100% cloud user. But with a user who is in an organization that uses ADFS gives me that error.
I need help with this error, if someone has had it, if the ADFS has something to do. Thank you. Sorry my bad English.
- Labels:
-
mtr teams
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 09 2020 11:47 PM
Did you check your certificates? Maybe the root/intermediate is missing on the device?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 10 2020 04:33 AM
When joining the domain the device will not need any type of certificate?
thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 10 2020 06:16 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 06 2020 02:04 AM - edited Feb 06 2020 02:17 AM
@Erwin Bierens @TeoDVz Is there any update on this, did you get it working? We also are trying to setup Crestron Flex devices and are also seeing the same issues as above. Using a cloud only account is not viable for us as we have no external mail routing in O365 cloud.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 06 2020 05:45 AM
Yes, I am in the last tests.
one-.
I uploaded the MTR console to the domain. Using the same user created when going through ADFS, I was in the login loop, checking the log I see that if you login to Microsoft Teams, but it gives an Exchange Autodiscover error.
two-.
The user assigned to the MTR is created and assigned an authentication policy.
Solution:
one-.
Connect to EXO by powershell.
two-.
New-AuthenticationPolicy -Name "Allow Basic Auth EWS on MTRs" -AllowBasicAuthAutodiscover: $ true
Set-User-Identity user@domain.com -AuthenticationPolicy "Allow Basic Auth EWS on MTRs"
NOTE: The name of the Policy may be the one you prefer. Let me know if it turned out.
regards
Noel Naveda.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 06 2020 08:06 AM
@TeoDVzThanks Noel. We have just set this but still not able to sign in but expect we may need to wait some time for the policy to take effect on the account. We will test again in the morning and report back. Thanks for your help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 20 2021 11:42 AM
Did you manage to get this working with the above change?
I also have the same issue.
Thank you for your help.