- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Re: Visualization Workbooks
Visualization Workbooks
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 01 2020 08:43 AM
Hey Community,
On our Cloud Sentinel env, i am trying to build workbooks, Under Visualization workbooks create two separate Incidents Column and build on Chart with that Incident. I would like to display incident from separate work-spaces in Separate column.
Query :
SecurityIncident
| take 20
Under Visualization DEMO workbooks,
On that All alerts generated on sentinel displays under output column. But we need to separate both core alert and outside org alert.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 02 2020 04:19 AM
@Vshah335 If I understand what you are asking for, you want to be able to have one column for those incidents created by Azure Sentinel and another for those created by other Azure security products like Microsoft Cloud App Security.
To do this, you need to get to the actual product creation which is hidden in the AdditionalData field and is called "alertProductNames". For some reason this is stored as a JSON array so need to extract that value and then expand it like this:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 05 2020 01:46 PM
Thanks Gary Bushey @Gary Bushey
I applied that Value under field name and it's works.
@Gary Bushey Do you have workbooks visualization template(not in-build in workbooks ) ? For only for Security Incident query. Just want to explore my self into it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 06 2020 03:31 AM
@Vshah335 The only one I have is the one that comes with Azure Sentinel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 07 2020 04:59 AM
| extend ProductName = (parse_json(AdditionalData).alertProductNames)
| mv-expand ProductName
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 07 2020 05:06 AM
@Vshah335 In the query below, you can then use ProductName.alertProductNames or ProductName.Owner or any other entry that is part of the AdditionalData field to get its data.
SecurityIncident
| extend ProductName = parse_json(AdditionalData)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 07 2020 06:44 AM
SecurityIncident
| extend ProductName = parse_json(AdditionalData, ProductNames.owner)
| mv-expand AdditionalData = " email "
Or
SecurityIncident
| extend ProductName = parse_json(AdditionalData, ProductNames.owner)
| where AdditionalData = " email "
I am running both query, but throw me error. Any Idea ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 07 2020 07:31 AM
@Vshah335 Needs to be more like
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 12:26 PM
I attached screen shot for need to Pharse down field called "Owner"
there are more elemnets, "Assign to" Userprinciplename" , " Object ID"
I tried Query u provided earlier, but won't get results what we need.
(Output only need on OWNER coloum "AssignTO " )
I hope you understand my question.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 14 2020 12:58 AM
Have you tried this? Also I don't see the screenshot you said you supplied.
SecurityIncident
| extend assignedTo_ = tostring(Owner.assignedTo),
userPrincipalName_ = tostring(Owner.userPrincipalName),
email_ = tostring(Owner.email)
| where isnotempty (assignedTo_)
| project assignedTo_, userPrincipalName_, email_
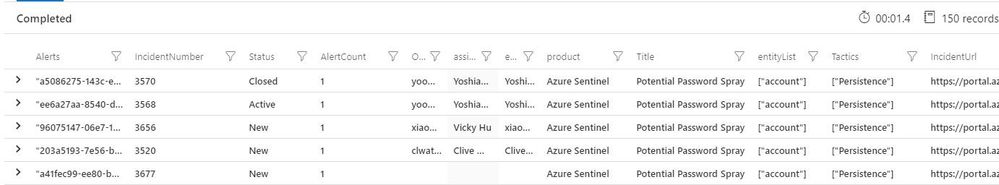
An example I use:
SecurityIncident
| where TimeGenerated > ago(7d)
| summarize arg_max(LastModifiedTime,*) by tostring(IncidentNumber)
| extend Alerts = extract("\\[(.*?)\\]", 1, tostring(AlertIds))
| mv-expand AlertIds to typeof(string)
| join
(
SecurityAlert
| extend AlertEntities = parse_json(Entities)
| mv-expand AlertEntities
) on $left.AlertIds == $right.SystemAlertId
| summarize AlertCount=dcount(AlertIds),
entityList=make_set(tostring(AlertEntities.Type)) by IncidentNumber,
Status,
Title,
Alerts,
IncidentUrl,
Owner=tostring(Owner.userPrincipalName),
assignedTo = tostring(Owner.assignedTo),
email = tostring(Owner.email),
product = tostring(parse_json(tostring(AdditionalData.alertProductNames))[0]),
Tactics =tostring(AdditionalData.tactics)
| project IncidentNumber, Status, AlertCount,Owner, assignedTo, email, product, Title, Alerts, entityList, Tactics, IncidentUrl
| order by IncidentNumber desc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content