- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Partial match with contains using watchlist
Partial match with contains using watchlist
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 07 2021 05:13 AM
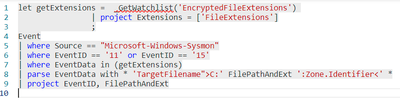
I am trying to create an alert when specific file extensions are found in any system, an alert is triggered.
For which I have file extensions in a watchlist, I want to write a query that reads data from the file creation event in sysmon and matches each extension with those in the watchlist if any of them exists in the watchlist an alert will be triggered.
So far this is what I am able to process, which is retuning an error saying, Tabular expression is not expected in the current context.
Event
| where Source == "Microsoft-Windows-Sysmon"
| where EventID == '11' or EventID == '15'
| where EventData contains _GetWatchlist('EncryptedFileExtensions')
| parse EventData with * 'TargetFilename">C:' FilePathAndExt ':Zone.Identifier<' *
| where FilePathAndExt matches regex@'([\.]\w+)'
| project EventID, FilePathAndExt
Any help would be appreciated, new to Kusto Query
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 07 2021 05:52 AM
let getUsers = _GetWatchlist('VIPUsers')
| project UPN = ['User Principal Name']
;
SigninLogs
| where AlternateSignInName in ( getUsers )
| summarize count() by AlternateSignInNameThis is an example of one way of doing this, using the 'VIPusers' template and Signinlogs - you can adjust to suit.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 07 2021 06:27 AM
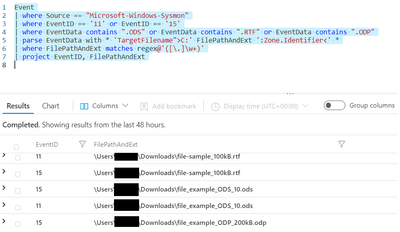
I did as you suggested but it doesnt seem to be returning any data, does in looks for matching partial data in the field like contains in this scenario? Modified query is:
However when I do so withouth watchlists the extensions exists and results are shown:
What could be the issue here?