- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Re: No option to tune analytics rule with Microsoft 365 Defender connector
No option to tune analytics rule with Microsoft 365 Defender connector
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:33 AM - edited Jan 04 2022 06:35 AM
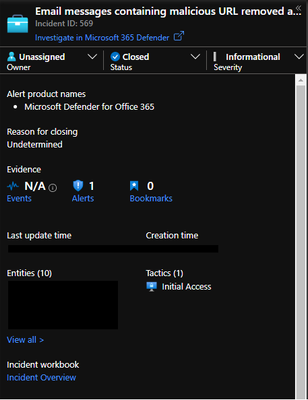
Greetings, i have been working with a few different customers and when trying to configure the Defender for O365 alert "Email messages containing malicious URL removed after delivery", however there is no option to add exlucions and minor tweaks to the analytics rule as it used to be when not connected via the Microsoft 365 Defender connetor.
The option to click "Create incidents based on *product name* alerts" does not exist after activating the Microsoft 365 Defender connector. Is there any way to do similar tuning anyway? I wish to not make informational incidents like the email messages, but still recieve the alert in the background and rather create an incident if more that 20+ of the same alert is recieved.
- Labels:
-
Alerts
-
Integration
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:36 AM
SolutionThe best way is to use automation rules to update these incidents based on certain conditions.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:44 AM
@Thijs Lecomte So the best way of solving this particular issue is to turn of the Microsoft 365 Defender connector for now and keep the connectors as they are separated. Since the M365 Defender connector is in preview i suppose there might be hope for this functionality in the future.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:47 AM
I haven't heard of any changes which would solve your issue. I guess the solution is automation rules... I don't think this will change
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:51 AM
The problem with using automation rules(as far as i know) is that the incident would still be created. I am working for a MSP and we are running a SOC which gets all incidents forwarded to them continously. I suppose i could try to create an automation rule that closes these incidents and put a check in the mail forwarding playbook to check if the incident is open or not(unless it does this by default)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:54 AM
You can setup priority for automation rules.
I close the incidents first and then only sync them
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 07:00 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2023 02:27 AM
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 04 2022 06:36 AM
SolutionThe best way is to use automation rules to update these incidents based on certain conditions.