- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- New Blog Post | Automating bulk onboarding of Azure IaaS and PaaS resources into Microsoft Sentinel
New Blog Post | Automating bulk onboarding of Azure IaaS and PaaS resources into Microsoft Sentinel
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 13 2022 09:58 AM
This blog was authored in collaboration with @Inwafula .
In recent years, cloud computing has grown in leaps and bounds due to its flexibility and agility in supporting business goals. Not surprisingly, the cloud also presents an equally attractive target for cyber attackers. This blog will focus on two key challenges as far as security monitoring goals for IaaS and PaaS resources on Azure are concerned:
- Securing current IaaS and PaaS digital estate by onboarding Microsoft Sentinel in bulk
- Automating newly created resources into Microsoft Sentinel
To address these challenges, the blog will cover the end-to-end process of onboarding Azure IaaS and PaaS resources into Log Analytics, enabling of related analytics(detection) rules and workbooks(dashboards), then attaching of automation playbooks to perform automatic remediation and SOC process activities.
Process Flow:
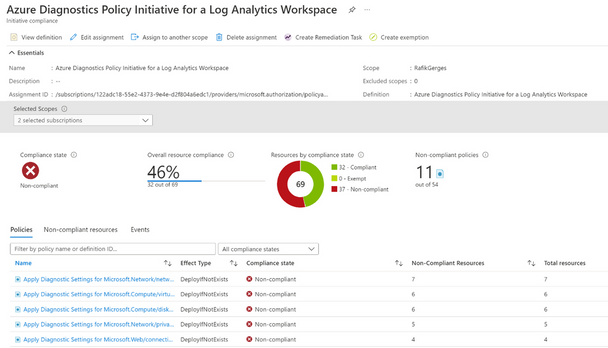
1. Onboard Azure IaaS and PaaS resources into a Log Analytics workspace enabled for Microsoft Sentinel.
2. Enable the built-in analytics rules associated with those resources, along with customized ones.
3. Creation of custom analytics rules
4. Attach automation playbooks to the analytics rules.
5. Enable workbooks available out of the box
Original Post: New Blog Post | Automating bulk onboarding of Azure IaaS and PaaS resources into Microsoft Sentinel ...
- Labels:
-
Analytics