- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Grouping Azure Sentinel - Azure Active Directory Identity Protection alerts
Grouping Azure Sentinel - Azure Active Directory Identity Protection alerts
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Oct 13 2020
01:45 AM
- last edited on
Jan 04 2022
12:16 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020
01:45 AM
- last edited on
Jan 04 2022
12:16 PM
by
TechCommunityAP
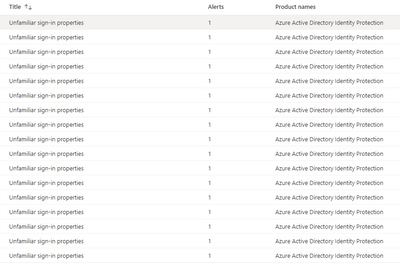
Is there a way to group Azure Active Directory Identity Protection alerts such as "Unfamiliar sign-in properties" in Azure Sentinel?
We are seeing hundreds of these alerts being raised on a daily basis and it is causing quite a lot of noise in the incidents panel of Azure Sentinel.
What would be really useful is a way to group all these alerts into a single incident, however, I do not see a way to do this.
Any guidance would be greatly appreciated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 04:03 AM
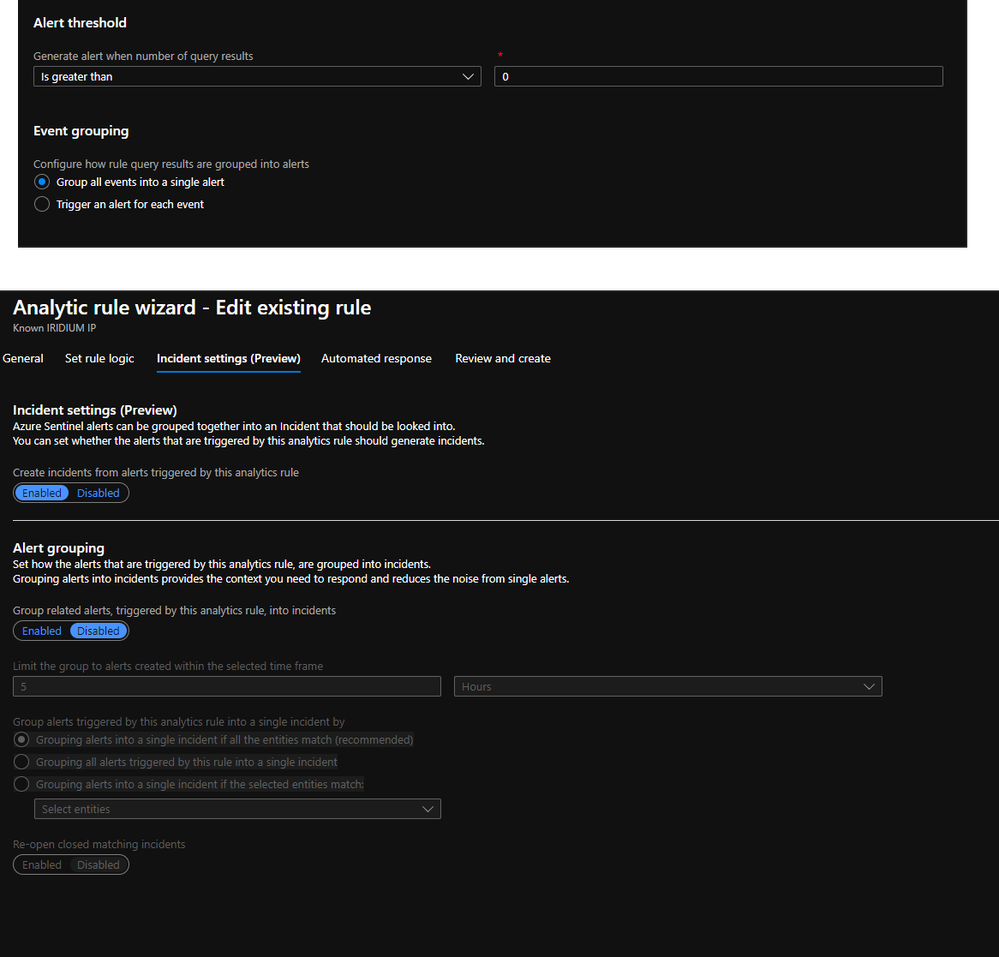
@TS-noodlemctwoodle If you modify the Analytics Rule, there's a couple spots in the wizard to configure alert grouping. The first is on the Set Rule Logic page. The other location is on the Incident Settings (Preview) page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 04:24 AM
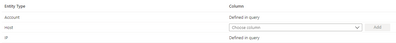
I have created a custom Scheduled rule and used this KQL to capture the same information that Identity Protection captures in the event.
SecurityAlert
| summarize arg_max(TimeGenerated, *) by SystemAlertId
| where DisplayName has "Unfamiliar sign-in properties"
| where AlertSeverity has "Low"
| project SystemAlertId, Entities, ExtendedProperties
| extend Entities = iff(isempty(Entities), todynamic('[{"dummy" : ""}]'), todynamic(Entities))
| extend ExtendedProperties = iff(isempty(ExtendedProperties), todynamic('[{"dummy" : ""}]'), todynamic(ExtendedProperties))
| mvexpand Entities, ExtendedProperties
| evaluate bag_unpack(Entities)
| evaluate bag_unpack(ExtendedProperties)
| extend userName = columnifexists("User Account", "")
| extend ipAddress = columnifexists("Address", "")I mapped the entities from the KQL in the rule
I grouped all alerts into a single incident
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 04:25 AM
@TS-noodlemctwoodle If you are referring to the Microsoft Security (Preview) rule to "Create incidents based on Azure Active Directory Identity Protection alerts" then the answer is no. The only thing you can change is what severity to include as well as to include or exclude specific alerts.
If you are referring to one you created yourself or another Scheduled rule than @Rod_Trent's answer is correct.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 04:29 AM - edited Oct 13 2020 04:29 AM
@Gary Bushey- I was indeed referring to the Microsoft Security (Preview) rule.
@Rod_Trentas @Gary Bushey says you can't edit the Microsoft Security (Preview) rules like you can with scheduled rules, so this wasn't possible, unfortunately.
I think I have overcome the problem now, I'm just testing it. :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 05:33 AM
My KQL definately requires some work to map the entities to each other. More R&D required :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 13 2020 05:39 AM
Make sure you also configure Incident Grouping, which will group everything into one incident.
IMO, you shouldn't Alert Grouping here, as one IDP should be one alert within Sentinel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2020 11:32 AM
I found the solution interesting. But if you are going to get the IP logs, through which table will these logs be retrieved?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 18 2020 11:22 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 27 2020 07:37 AM
Thank you very much for the information.
I am already using this feature and I am having good results.
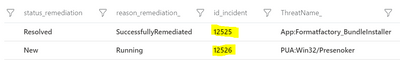
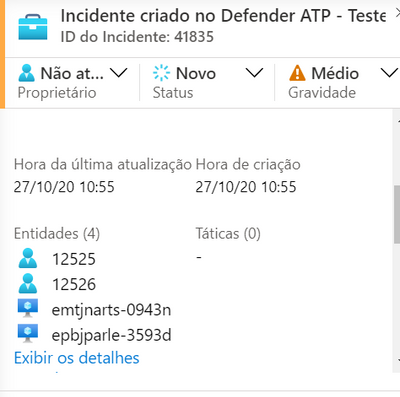
One problem I am experiencing is with a grouping function. I configured to group by [account]. When a query is executed, the logs point to two different users, but it generated only one ticket containing the two different entities in the same incident, even with a grouping option per [account].
The correct one should open two incidents, one for each [account], right?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 27 2020 10:00 AM