- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Re: Creation/exclusion audit in use cases
Creation/exclusion audit in use cases
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 14 2020 09:10 AM - edited Dec 14 2020 09:16 AM
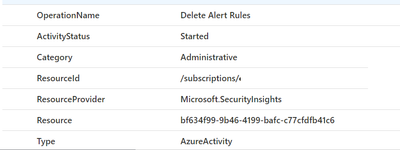
Good afternoon people! I need to do an audit process to identify which rules were created, changed or deleted, however, through the logs in the [AzureActivity] table, I can see only the rule id, which is not readable and identifiable.
Is there a way to find the name of the rule that has been modified?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 15 2020 08:11 AM
It was exactly what I needed, but I still run into a problem: the article crosses the logs of the table [azureactivity] and [securityalert] to identify the real name of the rule, but the point is that the table [securityalert] only brings logs of the rules that executed the query at some point, that is, if a rule is disabled or goes from enabled to disabled, it will not generate logs, therefore, if there is an exclusion or any change, it will not generate us in the table [securityalert] , thus not being able to know the real name of the table that suffers the action.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 16 2020 11:19 AM
Would a Workbook be a suitable way of auditing this data, showing the audit visually, or are you trying to create a Rule?
With a workbook we could probably check the REST API against the KQL data, the api will have "all" rules and the KQL any that have logged in the time period?
Another approach would be a playbook to get the api data into a custom log (daily?) and then compare against that?
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 16 2020 12:20 PM
Thanks for the reply.
In fact I want a rule that sends me at the end of the day a kind of "report" about all the changes / creation / deletion of the use cases.
The point X is that in the logs of these actions, thro ugh the table [AzureActivity], the real name of the rule does not appear, but an ID. I still haven't been able to find any way to identify the real rule behind the action.