- Home
- Microsoft Search
- Microsoft Search
- Re: Understanding security and privacy of Delve and intelligent experiences in Office 365
Understanding security and privacy of Delve and intelligent experiences in Office 365
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 25 2017 09:41 AM - edited Jan 26 2017 02:56 PM
Within Office 365, Delve is an intelligent service aimed at helping users stay in the know – to discover new, relevant information and people based on who they work with and the content they work on. Delve proactively discovers content across Office 365 and connects users to content and people, intuitively and in a personalized fashion. Powered by the Microsoft Graph, Delve brings you information from across Office 365 – OneDrive for Business, SharePoint Online, Exchange Online, Yammer, Office 365 Video and more. Delve will only show you content that you have access to—it always respects the permissions and security policies of that content.
We want to provide insight and clarity for the security and privacy that comes with, and backs, Delve in Office 365. And to be clear about what role the Microsoft Graph plays, examples of how it is used in Delve and throughout Office 365.
Security and Privacy
Delve is covered under the Office 365 Trust Center and meets all of the requirements of our highest level of compliance which Microsoft refers to as “Tier D” compliance, e.g., ISO 27001 and 27018 certification, SOC 1 and SOC 2 compliance. Delve is also licensed under the Microsoft Standard Online Services Terms which include commitments such as the EU Model Clauses. This, too, applies to the Microsoft Graph - the underlying intelligence service that uses advanced analytics to provide relevant, personalized insights via Delve and other user interface experiences throughout Office 365. You can read more within the public “Office 365 Compliance Framework for Industry Standards and Regulations" document (.pdf).
Customers own their Microsoft Graph data, which is stored in their partition of Office 365. The Microsoft Graph data has the same protection and security as other customer data stored in other Office 365 services.
Delve never changes any permissions on content or other information. Users only discover what they already have permission to see. Only you can see your private documents in Delve, unless you decide and act to share them. It is important content owners establish and maintain any required or desired access rights and permissions on the content/documents themselves. Documents are not stored in Delve, but rather they are only displayed within the Delve experience from where they are stored, for example OneDrive for Business or a SharePoint Online document library. People can't see each other's private activities, such as what documents they've read, what emails they've sent and received, or what Skype for Business conversations they've been in. People can see when others modify a document, but only if they have access to the same document. What you see when you open Delve is personalized to you, and no one else sees the same files, content, and activity you do.
It is possible to opt out of Delve at both the tenant level and the user level. Once opted out, users will not see the Delve tile in the Office 365 app launcher. Opted out users’ document activity (documents they are accessing) is no longer used to help others discover their content. Additionally, various services that surface content and recommendations from the Microsoft Graph to provide intelligence throughout Office 365 will simply not appear. They, too, may revert to previous non-Graph-based methods -- for example, search-based vs graph-based. One example, if you opt out, you would not see the new "Discover" tab within OneDrive for Business - yet the core of OneDrive for Business remains intact.
To learn more, please review these two important Delve security and privacy support articles; the first for admins and second for users: "Office Delve for Office 365 admins", "Are my documents safe in Office Delve?". Additionally, it is important to understand permissions levels in SharePoint and other content repositories; examine existing permissions if you perceive any unintended exposure.
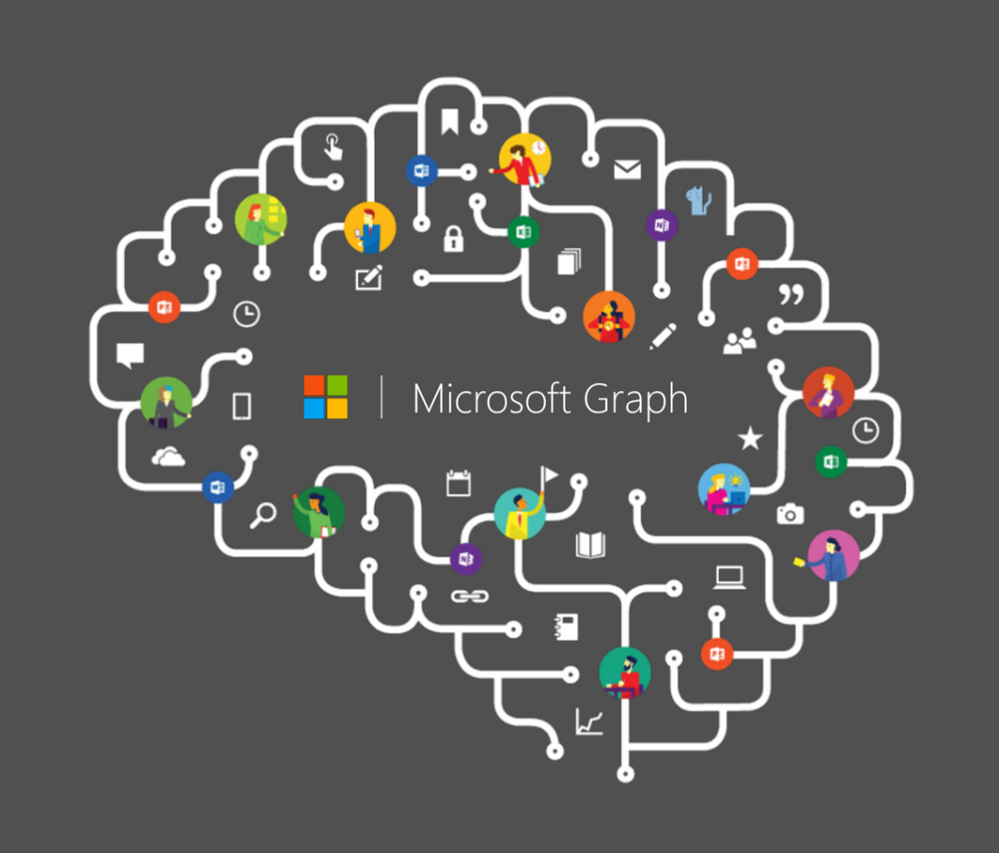
The Microsoft Graph – supporting the business user and the developer
The content, activity, people, and recommendations that surface in Delve and other intelligent experiences are powered by Microsoft Graph. The Microsoft Graph represents a collection of content and people, and the activity that happens across the entire Office suite. From email, social conversations, and meetings, to documents in SharePoint and OneDrive, the Microsoft Graph maps the relationships among people and information, and acts as the foundation for intelligent experiences, providing more relevant and personalized experience to each user. The Microsoft Graph uses sophisticated machine learning techniques to connect people to the relevant content, conversations and people around them.
A visual representation of the various content sources and signal Delve and the Microsoft Graph leverage to help make discovery or relevant content and people possible.
Review which types of content you can expect to see in Delve. And learn more about the Microsoft Graph.
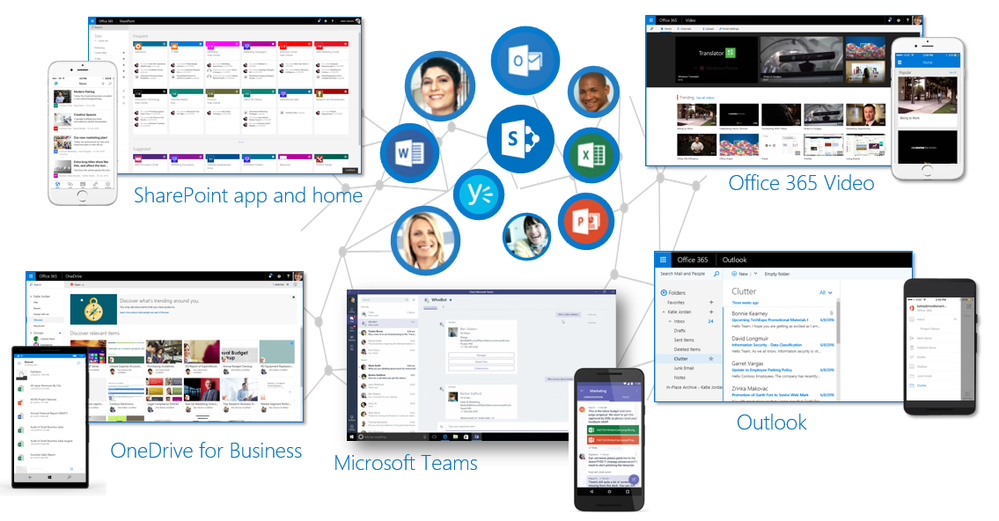
Intelligence beyond Delve, throughout Office 365 and beyond
The value of infusing intelligence within Delve, and throughout Office 365 applications, means you have access to intelligent information and insights right where you are working without leaving the app or experience where you are working. You’ll see intelligence in OneDrive for Business in the form of the Discover tab where you’ll find others’ files related to what you are working on. The home page of a SharePoint team site surfaces activities in the site, the SharePoint mobile app and the SharePoint home in Office 365 suggest sites of possible interest and recent activity, plus Outlook’s Focused Inbox, where the Graph helps identify and eliminate clutter in your email stream.
Screenshots on web and mobile where the value of intelligence from the Microsoft Graph surfaces throughout the various Office 365 workloads.
The effect of opting-out of Delve will reduce the intelligence and discovery experiences in Office 365. It is our recommendation to not opt out.
It is also possible to program your own custom solutions for any device with the intelligence from the Microsoft Graph. Developers leverage a single end point that provides access to a common set of simple, modern APIs. Using the Microsoft Graph API, developers can consume Office 365 data in their apps to create custom, personalized experiences for their users. You can learn more about developing with the Microsoft Graph at https://graph.microsoft.io. And the same data access security and privacy model, as articulated above, remains with custom applications that use the Microsoft Graph API. Custom applications querying the Microsoft Graph do so under the security context of the user and will only return content to which the user has been given permissions.
Delve and intelligence customer evidence
As you move from learning about Delve and the Microsoft Graph, into how you and your company can best introduce the value and capabilities to your users, it’s helpful to review how other companies chose to move forward, helping them to overcome a variety of challenges facing them. Below are two recent examples of companies that committed to putting Delve and the Microsoft Graph to use in production, into their evolving digital workplaces.
Marks & Spencer | M&S is a global, multichannel retailer with more than 1,330 stores selling innovative food and quality clothing to people living in many different cultures. They wanted to find a way to unite the company. To promote unity, they sought the right technology tools to support a new business culture— one that is modern, agile, connected and collaborative—that’s defined by a digital mindset across a single global company.
Alongside their company portal, serving 80,000 employees, Delve provides intelligent people discovery. “We plugged Delve into our company directory, so employees can look for individuals and see their managers and who they work with. We view Delve as a quick and easy way to find current data to keep us moving at a fast pace in this fast-paced business.” says Carl Dawson, IT Director.
Please review the full Marks & Spencer case study + video.
Weleda | Based in Arlesheim, Switzerland, Weleda has offices and partnerships in more than 50 countries. They needed to connect employees to the relevant content, conversations, and people around them. By “embedding Delve-like functionality into our intranet, it helps employees stay better connected to the colleagues, information, and projects that mean the most to them,” says Vladimir Filev, Enterprise Architect. Weleda employees are using Microsoft Office 365 to work closely with colleagues worldwide, transforming an email-driven workplace into an inclusive, connected culture that promotes individual achievement to improve global productivity and drive innovation.
“Because Delve has such a great search engine,” Filev continues, “I’m able to keep track of contacts and files across multiple projects I’m involved with. In terms of personal time management, I find Delve very helpful.”
Please review the full Weleda case study.
Intelligence rests on trust
Microsoft is committed to security, privacy and compliance. Your data is your data – and it is you who has control of who can see it and who can access it. Through transparent service operations, we seek to gain and earn your trust every day. We are accountable to you.
Thanks for keeping us accountable,
Mark
Additional related resources
- SUPPORT ARTICLES
- “Share files or folders in Office 365”: https://support.office.com/en-US/article/Share-files-or-folders-in-Office-365-1fe37332-0f9a-4719-970...
- "Are my documents safe in Office Delve?": https://support.office.com/en-us/article/Are-my-documents-safe-in-Office-Delve-f5f409a2-37ed-4452-8f...
- "Office Delve for Office 365 admins": https://support.office.com/en-us/article/Office-Delve-for-Office-365-admins-54f87a42-15a4-44b4-9df0-...
- “ Understanding permission levels in SharePoint”: https://support.office.com/en-US/article/Understanding-permission-levels-in-SharePoint-87ecbb0e-6550...
- BLOGS
- "Connect to expertise and content with new people experiences throughout Office 365" [9/26/16]: https://blogs.office.com/2016/09/26/connect-to-expertise-and-content-with-new-people-experiences-thr... (this is also the one MS Tech Summits stream on-demand)
- "Enriching the mobile and intelligent intranet with team news, apps for Android and Windows, and more" [9/26/16]: https://blogs.office.com/2016/09/26/enriching-the-mobile-and-intelligent-intranet-with-team-news-app...
- "SharePoint - the mobile and intelligent intranet" [5/4/16]: https://blogs.office.com/2016/05/04/sharepoint-the-mobile-and-intelligent-intranet/
- “ Today at Connect()—introducing the Microsoft Graph” [11/18/15]: https://blogs.office.com/2015/11/18/today-at-connect-introducing-the-microsoft-graph/
- “ Office - Microsoft Graph: Gateway to Data and Intelligence” [Connect 2016]: https://msdn.microsoft.com/en-us/magazine/mt790189.aspx
- VIDEOS
- "Discover what's new and what's coming for Office Delve" on-demand BRK2044 session recording: https://myignite.microsoft.com/videos/1359
- "Discover what's new and what's coming to the SharePoint Mobile and Intelligent Intranet" on-demand BRK2029 session recording: https://myignite.microsoft.com/videos/1302
- "Explore new personalized, intelligence powered search experiences in SharePoint, Delve and Office 365": https://myignite.microsoft.com/videos/1363
- "The Mobile and Intelligent Intranet: SharePoint sites and PowerApps": https://youtu.be/x8tgKBXmmPg
- "Updates to the SharePoint app, team sites and publishing experience": https://youtu.be/W4J6hZtove0
- Labels:
-
Delve
-
Office Graph
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 25 2017 10:40 PM
great post thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 26 2017 05:05 AM
Great post @Mark Kashman ! The "Intelligence beyond Delve, throughout Office 365 and beyond" section was great additional information for me.
p.s. the link "understand permissions levels in SharePoint" references an URL on my Microsoft OneDrive, which is not accessible for people outside your organisation.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 26 2017 02:57 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2017 09:05 PM
Great post, @Mark Kashman. Thanks for the insight and update on Delve's compliance maturity. I have check the January 2017 version of the OST, and Delve is not presently listed with Data Protection Terms - is expected to be added in February? Or perhaps later? Do you have any visiobility here? - Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 30 2017 01:46 PM
My orgs change management board refuses to turn this on without being able to test first. We need a way to turn on for only certain users, even if that is turning on for the tenant then disabling for everyone in the org except IT. Can the Off for Documents be manipulated for a user via powershell??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 10 2017 10:21 AM
Hi Robert. Give this a review and see if it helps. The team is Oslo is reviewing how to enable this more from within our UI or starardizing via PowerShell; but the below has been performed a number of times with success for pilot purposes...
How to setup a Delve pilot by having Delve/Graph on, and then programmatically opt-in a subset of users during a pilot/trial phase; via the User Profile property. External blog post with CSOM examples, by Nicki Borell (b-nibore@microsoft.com): http://www.sharepointtalk.net/2016/11/opt-in-as-default-for-delve_40.html?m=1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 10 2017 10:22 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 11 2017 02:45 AM
Brillian Post Mark, very very informative
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 18 2017 02:23 AM
Here some additional insides also about the myth of the People suggestion in Delve: http://www.sharepointtalk.net/2017/03/delve-and-office-graph-inside-out-part.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 16 2017 05:02 AM
Quite a common concern customers have is that they want to enable Graph, but don't want Delve to surface documents others around them are working on.
In Delve, each user can switch this off for their own profile. Users can also hide specific documents from surfacing in Delve using a HideFromDelve site column.
For some customers that is still not enough. For such customers, a possible workaround could be to add the “SharePoint:isDocument” Crawled Property to the “HideFromDelve” Managed Property
O365 Admin -> SharePoint admin center -> search -> Manage Search Schema
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 16 2017 06:09 AM
That's true. Where I was, Delve really freaked out a lot of people to begin with, during a SharePoint rollout, senior managers wanted it disabled almost straight away. That's when I asked this question at the time - Disabling Delve?
After explaining exactly how it works and that Delve doesn't change anything, it was accepted and the subsequent training was upfront about Delve and what it does. We also talked about this in the Product Spotlight: Delve by the way.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 16 2017 08:22 AM
I totally agree that once users are educated, their concerns with regards to what Delve surfaces gradually diminishes. However, many companies don’t invest adequately upfront in training their users. Then all it takes is one senior manager to stumble across sensitive documents their co-workers are currently working on in Delve, and thereafter Office Graph will be disabled indefinitely.
From a customer perspective (in my experience) they would far rather mitigate risk when enabling Office Graph initially without having to make an all or nothing decision. In such scenarios, tweaking the HideFromDelve managed property in the search schema should be a very simple exercise - I say “should” because I haven’t personally tested it. Theatrically it “should” work :smiling_face_with_smiling_eyes:!
With this approach you could also implement the completely opposite intended behaviour to surface only “approved” content in Delve by adding the HideFromDelve site column to all document libraries where you "want" to surface content in Delve, with the default value for the HideFromDelve site column set to "False" instead of True.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 16 2017 08:40 AM - edited Jul 16 2017 09:10 AM
I must mention one caveat though - this approach will only hide content in Delve which has been tagged as a “Document” document during the crawl process. If the “SharePoint:isDocument” is set to “False” (No) during the crawl, the effective value for the “HideFromDelve” property for item crawled will thus also be set to “False”, so that item could thus still surface in Delve.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 16 2017 12:42 PM
Some granularity I think would be appreciated, HideFromDelve is good to have but more central control either user or on a site/document library basis might be helpful.
I get the impression that disabling Office Graph is discouraged really and that's probably why there aren't more options. It's like a deterrent with the all or nothing approach. Office 365 after all without Office 365 Graph is going to be rather backwards!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 26 2017 11:04 AM
I would say it's catch 22 and the way works now is likely necessary in order to deliver the next wave of auto classification for content in terms of Information Sensitivy from a Security and Compliance perspective. The Graph API is probably needed to do this. If content is automatically secured based on classification policies, this becomes irrelevant.
For example a policy could dictate that contain specific words or phrase, and such documents cannot be shared to "Everyone" for example. Other policies could be created to protect information is any site classified as HBI, etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 04 2017 07:24 AM
Delve just created a bit of shock for us. My contractor called and told me that she can see all documents that she is supposed not to see on her page. That includes HR forms, invoices, and other things. These are documents that are on my One Drive and is not shared with anyone. Is there a way to disable this feature enterprise wide?
By the way, why is the default security settings on One Drive set to the lowest security level. Also, when you turn on new features give your customers an option to turn in on and not just turn on without their permission especially for features like Delve. I understand you want higher rate of adoption. But often times it is creating too much head ache for IT admins.
Thanks
Rajesh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 04 2017 07:52 AM
Yes, you can turn this off or just opt-out but it's not necessarily that simple. First, check out this:
Office Delve for Office 365 admins
In the 'Control access to the Office Graph' section, you will see the steps to disable Office Graph in the tenant, which powers Delve. Bear in mind, Office Graph does a lot more than just Delve and you loose considerable functionality by taking this path.
If you read some of the resources in this discussion, you will see Delve never changes any permissions and only surfaces what users have already been given access to. By disabling Office Graph, users can still access these documents by other means, so it's better to look at the underlying issues and deal with those.
Check that documents haven't been saved to the 'Shared with everyone' folder in OneDrive, as that would open them up to everyone. Otherwise, there must be some permissions to grant access or have been shared in some way for the contractor to have been able to see the documents. If there is no indication on further inspection why this is happening, I'd consider logging a service request, as it just doesn't sound right.
Another option is to opt-out of Delve as covered here -
Are my documents safe in Office Delve?
Hope you get to the bottom of this. I know it can be a shock with these incidents but Delve is really a great feature once understood and everyone knows what to expect from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 04 2017 10:27 AM
Thanks for the quick response. My OneDrive default settings is to not share anything with anyone. Anything that is shared has to be explicitly configured. However, I think documents that were outside of this was showing up on Delve. I must say that I have to cross check on this one and will do that.
By the way, do you have some practical examples or uses cases for enabling Delve? If it is such a powerful tool, we certainly want to know what value it can add to us. However, the first experience of it was not good.
Regards
Rajesh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 05 2017 06:49 AM
No problem, I'd start here which has a nice set of resources - Discover relevant content and people. You might want to check out some Ignite presentations as well, such as:
Build your personalized and social intranet with SharePoint, Yammer, Delve, OneDrive and Teams
How Graph powers intelligent experiences in SharePoint and Office 365