- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Windows Information Protection & the Windows Home edition conundrum
Windows Information Protection & the Windows Home edition conundrum
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 29 2018 07:06 AM
There doesn't seem to be a full answer to this problem, so I'm sounding it out here in case anyone has any bright ideas.
The crux of the problem, is that there's no "Edition" filter that we can apply within Intune enrolment or compliance policies (or Azure Conditional Access)...
Explaining why this is a shortcoming:
Due to the nature of this organisation, typically BYOD (personal devices) can be limited to browser-only access to SharePoint / OneDrive online through Azure Conditional Access Session Control; however there is an emerging use case for offline access on BYOD (the org already has a precedent of soft-managing BYO devices, so this part isn't a problem), but a requirement to ensure the files are kept securely.
This is where I feel WIP would provide suitable gap-filling capabilities; but there's quite a significant pre-requisite: It requires Windows 10 1607 Pro edition (or higher). The 1607 part of that isn't a big problem, as Intune can cater for version limits within enrolment policies, but there's no Edition filters/requirements.
This means we can set up WIP and MAM, and have all the nice secure controls applied to any BYO devices running Win 10 Pro, however as soon as someone enrols a Win 10 Home device, it simply ignores all of that and allows free-reign over non-encrypted files.
Seems like a bit of a hole to me.
I'm trying to come up with workarounds to this gap, things like attempting to apply a BitLocker compliance policy specifically to Home edition devices, which of course will fail and mark the device as non-compliant (which can subsequently be filtered in Azure Conditional Access), but this isn't an elegant solution.
Anyone else have any ideas, or also feels there's something missing here?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 31 2018 12:53 AM
I guess you already tried this: device restriction settings in MS Intune profiles?
https://docs.microsoft.com/en-us/intune/device-restrictions-configure
On Windows 8.1 and later you can enforce encryption of files
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 13 2018 02:03 AM - edited Feb 13 2018 02:09 AM
WIP is appealing for BYO scenarios since it only applies to corporate data / apps, rather than wholesale applying overbearing policies to every part of the device, specifically causing constraints in the context of encryption (requirement for MS accounts; requirement for InstantGo hardware certification etc).
It appears the trade-off of not implementing the overbearing policies is an incomplete picture, if those on a Home edition can simply bypass the policies - and there's no way to conditionally stop them.
Despite there being an "operatingSystemEdition" field within the hardwareInformation properties of managedDevices in Graph, Intune isn't filling this in, so we can't even create dynamic groups based on OS edition.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 08 2018 11:45 AM
We have exactly the same experience and I hope someone can explain how we can control also the Windows Home edition.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 18 2018 09:24 AM
+1 - nothing more to add!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 21 2018 05:46 AM
Where did you find that WIP only supports Windows 10 Pro and higher? For as I know is that WIP also Home Edition supports. With WIP you can manage your corporate data on Home edition. This only with MAM without enrollment. MDM is another story, but WIP and MAM without Enrollment on a Home edition is supported and works the same as a Windows 10 Pro edition.
Link for more information: https://docs.microsoft.com/en-us/windows/security/information-protection/windows-information-protect...
Quote from the link:
"Windows Home edition only supports WIP for MAM-only; upgrading to MDM policy on Home edition will revoke WIP-protected data access."
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 21 2018 06:00 AM
But if you have any additional info on how to enforce WIP on home edition, we'd be happy to hear about it! ;)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 21 2018 07:57 AM - edited Jun 21 2018 07:58 AM
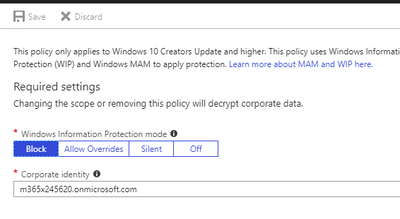
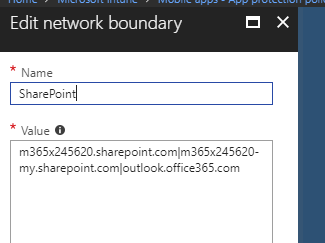
That is strange. So, the same policy works on Pro but not on a Home edition device? With the same user account? I have here a Home edition test virtual machine. Windows 10 1803 is on this machine installed. If I enable the MAM without enrollment for Windows 10 then WIP will activated on the Home Edition machine. I have allowed IE, Edge, Word, Outlook, Onedrive and OneNote. I have also included these network perimeters: <domain>-my.sharepoint.com|<domain>.sharepoint.com|outlook.office365.com.
This is it.. More is not needed and your BYOD is managed by MAM without enrollment policy based on Windows Information Protection.
See here the settings:
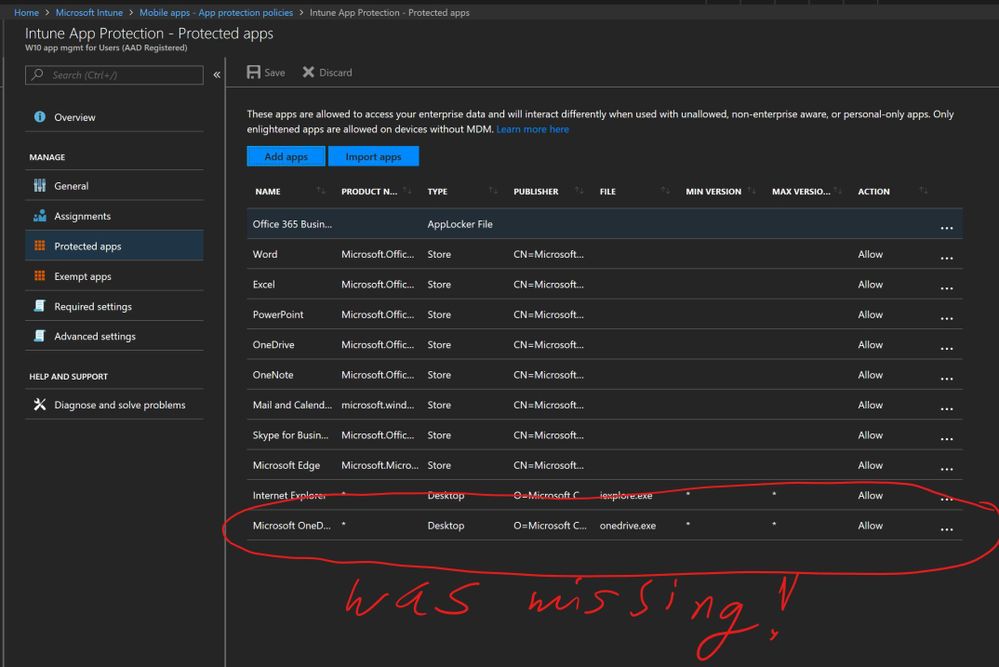
The protected apps:
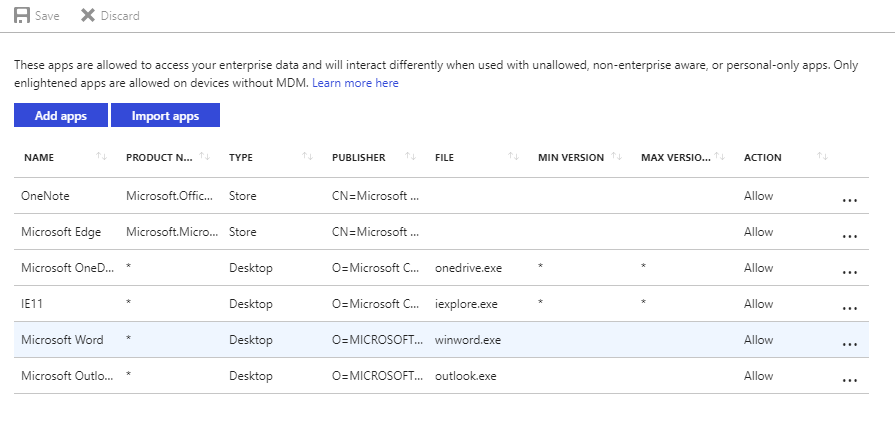
and the network perimeter:
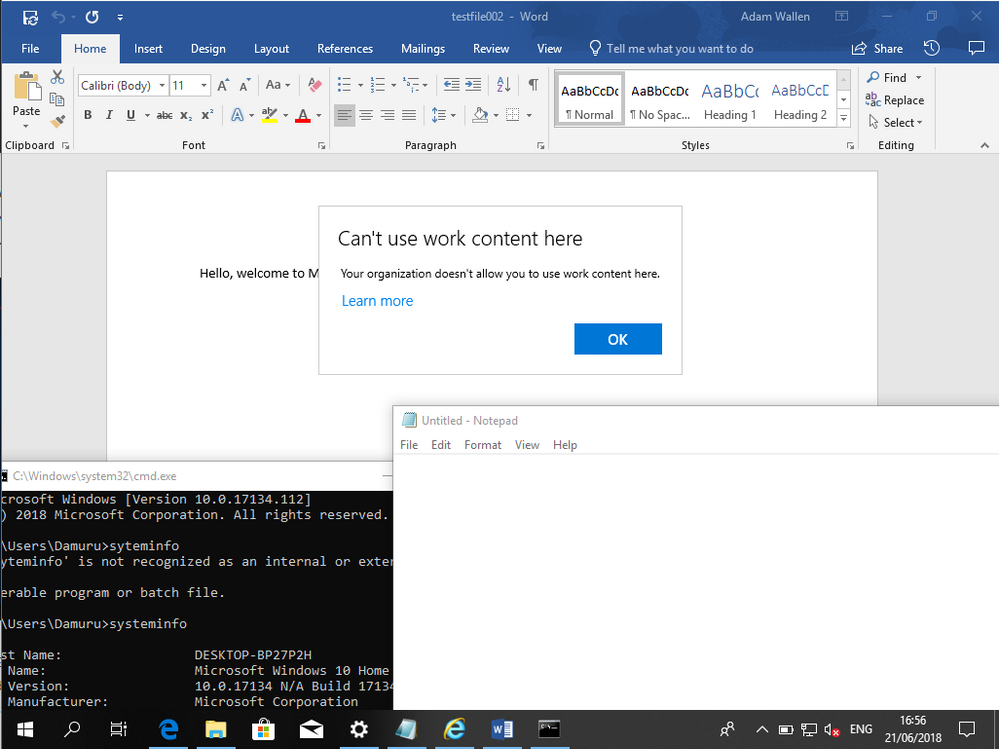
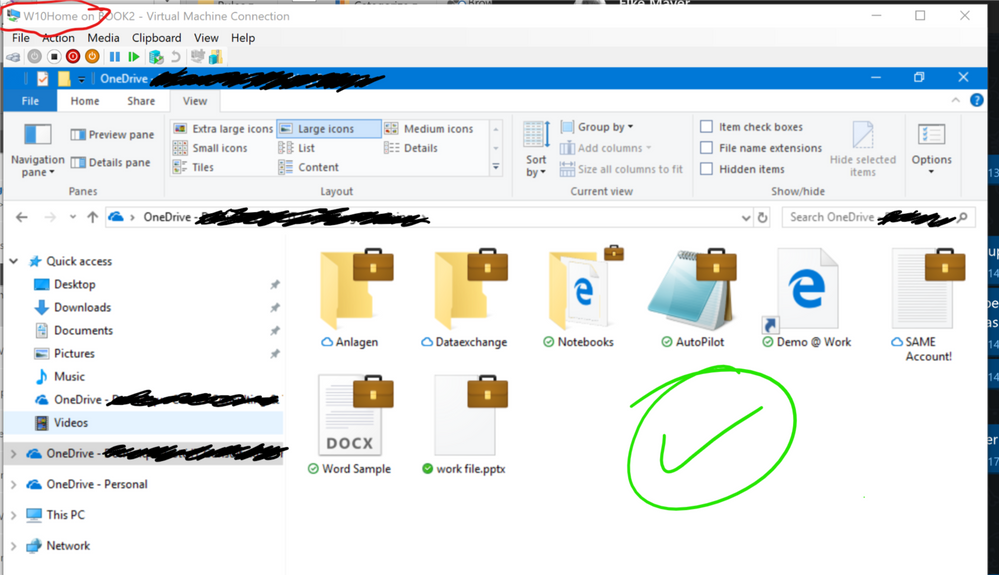
And this is on a home edition:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 21 2018 11:32 AM
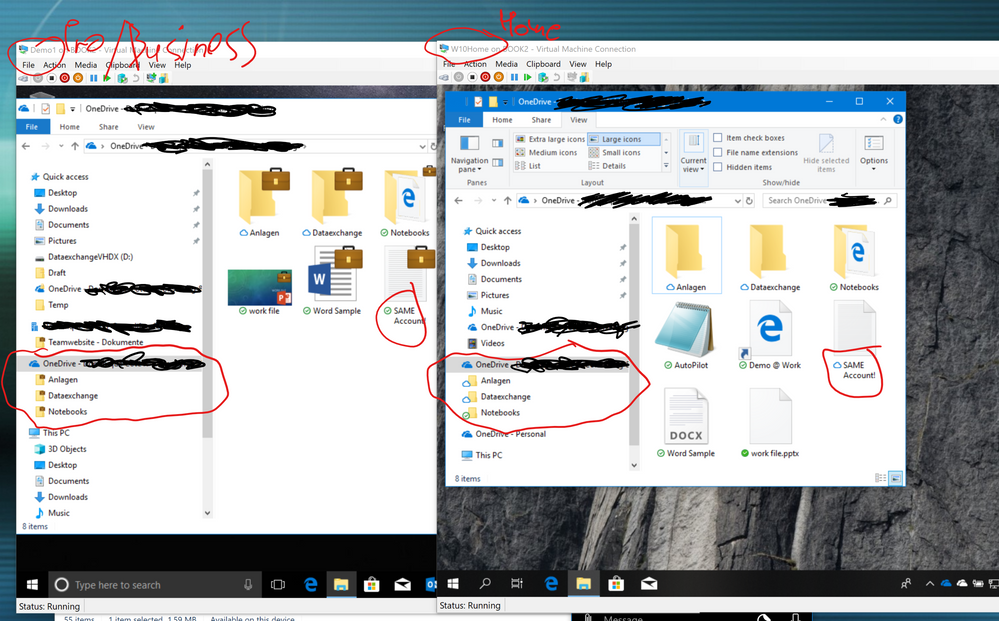
This is a direct comparison. For visibility, I turned the "show briefcase" policy on. Left=Pro/Business, right=Home. Same account, same tenant, same builds even.
The basic polices I setup are pretty much the same as yours. But something is stopping Home from honoring MAM+WIP policies. Or it's plain broken. And nope - no MDM in sight anywhere. And even if there were, that Home just lets me extract work files unencrypted is unacceptable. Under ANY circumstances.
So how did you make yours work and mine/ours doesn't? Any ideas?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 22 2018 01:44 AM
Thanks for your response and screenshot.. How did you add the corporate user account? Via Word/Outlook or via the settings -> work/school account? It makes no difference, actually.
What I did you can find it here. I have blogged the steps what you have to do for MAM-WE on a Windows BYOD. The screenshots are from a Home Edition machine.
Maybe this will help? :) Otherwise you have to try a new Home Edition machine?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 26 2018 09:13 AM - edited Jun 26 2018 09:30 AM
Apologies - my bad. In TWO ways.
First: I simply didn't add OneDrive DESKTOP app to my policy:
I should've known better. Here's why:
We use Microsoft 365 Business. The WIP policies it comes with include some protected apps by default, among which is the OneDrive STORE app, but not the desktop next-gen sync client. I have no idea why M365B doesn't include ODfB Sync by default, but it mislead me. Again. Because already solved this problem a few months ago. :rolling_on_the_floor_laughing:
Anyways, I added the ODfB desktop/sync client to the list, and voila:
And SECOND: The W10 Pro VM I used to test above ^^ is actually AAD-joined - which I didn't know. A colleague of mine was using it for other purposes and joined it. So it was following a different set of policies: For enrolled devices, right? That policy obviously works just fine, so it naturally showed WIP protection active. I just validated my findings with a new, un-enrolled (AAD registered, not joined) W10 Pro VM and was able to get the same, expected (!) behavior on Pro and Home.
So, all is good, WIP on W10 Home DOES work. Which makes this an awesome and low-cost option for any kind of BYOD / work from home requirement. Sorry to bug you but, sometimes you just need a sounding board to validate what you're doing - or not. ;)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 27 2018 01:15 AM
No problem Dominique, I was a pleasure to help you. Now I understand why WIP did not work on the Home Edition. I am glad that you have resolved the problem. Cheers!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 02 2018 06:56 PM
Hi Dominique,
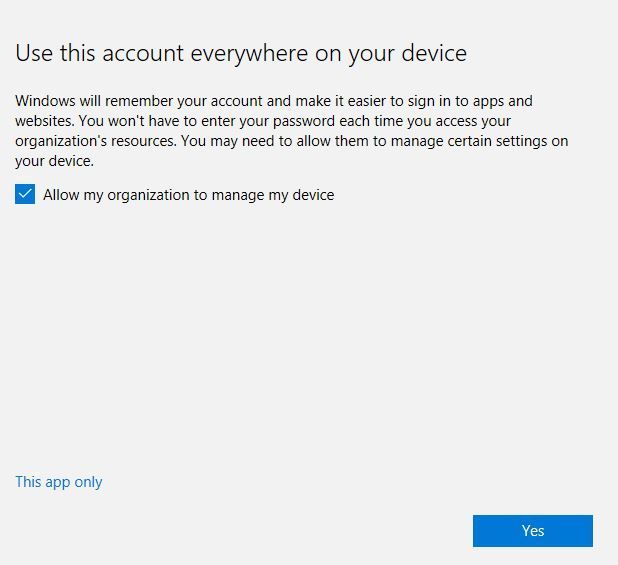
but what happens when the user skips the device registration?
say if he chooses to use 'this app only' as below:
in this case win home will bypass the WIP policy.
I'm wondering if there a way to enforce the WIP policy on windows home?
it's also mentioned here: https://social.technet.microsoft.com/Forums/office/en-US/890ed582-6b11-4c0c-bdff-580867a1fec2/wipwe-...
Regards,
Stan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2020 01:35 AM
Did you ever find a method to ensure that the Intune Company Portal was installed and WIP in place on home edition clients?
I know this is quite an old thread but currently this is the closest I have found to my question.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 18 2020 02:31 AM
@richochet If you're trying to block access from non-compliant devices (ie. ones not following WIP policies), you can use Conditional Access. CA will deny access to company resources at the cloud level - making it independent of the device used. Whether the device is compliant with your policies is only one criterion - there are many more, too. So for an environment where company-owned Windows Pro isn't the global standard, CA is probably the best approach IMHO. CA is included in M365BP, M365E3 and E5.