- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- White Glove , Second time around
White Glove , Second time around
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2019 02:56 PM
Hi
Upon testing of white glove with Windows 10 1903 builds , we are seeing that second time around on the ESP page the device is sitting at "registering your device for mobile management". This is despite deleting the device from Intune and resetting the TPM chip in the BIOS.
Any ideas ?
- Labels:
-
Intune
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 05 2019 07:46 PM
Did you first use "Wipe" without retain enrollment
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 11 2019 01:40 AM - edited Jun 14 2019 03:41 AM
@Darren_Bradley I didnt know we were already able to use the White Glove deployment options.
I have the same issue with a Windows 10 version, created last friday with the Media Creation tool 1903.
And will try the Wipe option as mentioned by @Neil_a_Consultant and come back in a hour orso.
<update after 1 hour>
Wipe is not working since it has no Intune device id yet when importing the device.
Tried to reimport it (deleted all stuff related to the device) synced the devices and trying again.
<update after reimport>
Machine failed again, but i am able to wipe it. So waiting for the actions to complete...
<update after wipe>
It looks like it is 1 step further and fails (but says Succes in the Red screen).
That is the Prepare the device for MDM (my own translation, got a dutch win10 here).
Clicked on retry multiple times and after the 3rd time it passed the first part and stopped during the next phase (device phase). No info at all. The Red screen again with the Succes message.
Wiping the device again to see if it makes any difference.
<day2>
I removed the device from customer tenant and it is now imported in my own tenant.
Removed the Intune company portal in the ESP (guess this one is my issue right now) and waiting now.. But it seems like it never wants to install an app. Even increased the ESP wait time.
<day3>
So after all kind of checks and tests, i removed all test apps in my test tennant.
Now it will pass the 2nd part, but no Seal option yet (still see a Red screen with a Succes-msg), so my guess is that MS still has to do some things.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 08 2019 07:45 AM
@Patrick Stalman Couple things... If you are doing Hybrid AD join, the device needs to write back to AD i believe, so try doing a Start-ADSyncSyncCycle on your AADConnect box. Also, you can get logs by turning logging on in the Auto Pilot Profile, then after a failure insert a USB drive click the log button and the logs will be written to the USB drive. Just wait like 30-60 secs for the logs to fully write and take a look. This is not documented to my knowledge but someone posted the info on a thread somewhere.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 08 2019 07:50 AM
Cheers , the devices are Azure joined only but I am aware of the write back as we are also using Windows Hello for business.
We actually seemed to have "fixed" this now but subscribing the machine to the Semi Annual update channel in intune which "blocks" any updates during the enrolment. If we select the update to be insider the device will reboot prior to reseal.
We have not tested this again with 18362.207 but we will do when I get the chance.
Useful information about the log files though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 09 2019 02:43 AM
I see there is some log talk here for AutoPilot.
If you have failures you can also press SHIFT + F10 and in the CMD prompt type:
Mdmdiagnosticstool.exe -area Autopilot -cab c:\Autopilot.cab
and then Xcopy it to a USB.
Adam
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 09 2019 03:05 AM
Cheers , We use the Shift F10 to install the 18362.207 update prior to running White Glove from the Media Creation 18362.30 version due to the Offline Store "BUG". We also use it to connect via the WIFI instead of the LAN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 05 2020 08:56 AM
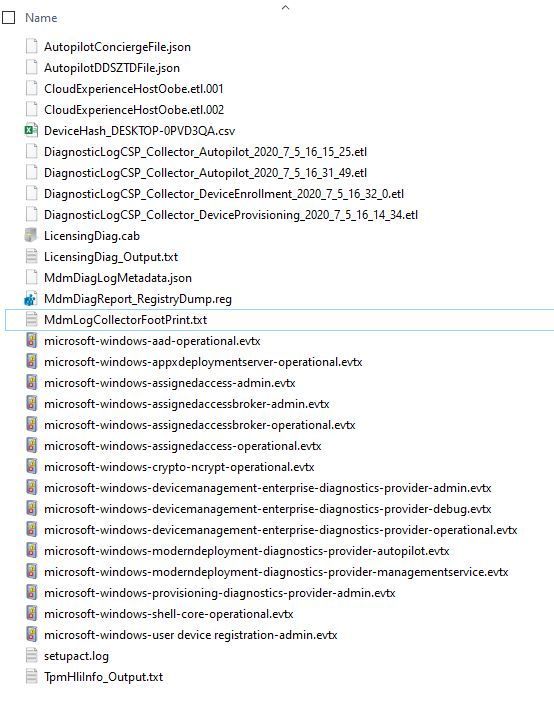
Is there a particular file to potentially look into?
The CAB file generated has a lot of files within it:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 06 2020 01:19 AM
@RaviLu - Hey,
I guess there may be a few you would need to review if you're not sure where something is failing. Below should give you a good indication of where to look:
Notes: For ETL files are event tracing logs (diagnostic logs), you will need Windows performance analyser tool - But I doubt you'd need to go as in-depth so you probably won't need to look at these.
| File name | Usefulness | Comments |
| CloudExperienceHostOobe.etl.* | Low | ETL trace files. |
| LicensingDiag.cab | Low | If you’re running into Windows activation issues, you might care about this, but otherwise, it’s not useful for Autopilot troubleshooting. |
| AgentExecutor.log | Low | This is picked up from the Intune Management Extensions log folder (C:\ProgramData\Microsoft\IntuneManagementExtension\Logs) but I’ve never found anything useful in it. |
| AutopilotConciergeFile.json | Low | At this point, this file is not used. |
| AutopilotDDSZTDFile.json | High | This file contains the Autopilot profile settings being used for the device. |
| CertReq_enrollaik_Output.txt | High | This file only exists when the TPM area is included. It provides a simulation of the TPM attestation process and logs the results, so it’s useful to see why the “real” TPM attestation might be failing. |
| CertUtil_tpminfo_Output.txt | Medium | This file only exists when the TPM area is included. It provides more details about the TPM chip or firmware used in the device. |
| DeviceHash_*.csv | High | This contains the serial number and full hardware hash for the device. While that hash might not look useful to you, it tells us a lot about the device, including the version of Windows 10, patches that are installed, TPM firmware version, and a lot more stuff. |
| DiagnosticLogCSP_Collector_Autopilot.etl | Low | ETL trace files. |
| DiagnosticLogCSP_Collector_Autopilot.etl.merged | Low | ETL trace files. |
| DiagnosticLogCSP_Collector_DeviceEnrollment.etl | Low | ETL trace files. |
| DiagnosticLogCSP_Collector_DeviceProvisioning.etl | Low | ETL trace files. |
| IntuneManagementExtension.log | High | This log will capture excruciating detail about the installation of Win32 apps being deployed via Intune. (Use one of the ConfigMgr log viewing tools, e.g. CMTrace.exe, to view this.) |
| LicensingDiag_Output.log | Low | This captures the output of the LicensingDiag.exe command that generated the previously-mentioned LicensingDiag.cab. |
| MDMDiagHtmlReport.html | Medium | This is the same report you can get from the Settings app that provides more details on all the MDM policies that have been applied to the device. |
| MdmDiagLogMetadata.json | Low | This records the areas that were specified on the MDMDiagnosticsTool command line (or those added automatically). |
| MDMDiagReport.xml | Medium | This is a machine-readable XML version of the HTML report above. |
| MdmDiagReport_RegistryDump.reg | Medium | This dump the contents of a variety of registry keys that are useful to determining the state of the machine, including MDM enrollment details, Autopilot details, and related info. Support technicians may use this to find related information in Intune. |
| MdmLogCollectorFootPrint.txt | Low | This shows everything that MDMDiagnosticsTool tried to collect and put into the CAB file. |
| microsoft-windows-aad-operational.evtx | High | This event log shows Azure AD join and Hybrid Azure AD Join-related info. |
| microsoft-windows-appxdeploymentserver-operational.evtx | Low | This event log shows details from UWP app installations. |
| microsoft-windows-assignedaccess-admin.evtx | Low | This event log contains events related to kiosk configuration. |
| microsoft-windows-assignedaccessbroker-admin.evtx | Low | This event log contains even more events related to kiosk configuration. |
| microsoft-windows-assignedaccessbroker-debug.evtx | Low | This event log contains even more events related to kiosk configuration. |
| microsoft-windows-assignedaccessbroker-operational.evtx | Low | This event log contains even more events related to kiosk configuration. |
| microsoft-windows-assignedaccess-operational.evtx | Low | This event log contains even more events related to kiosk configuration. |
| microsoft-windows-devicemanagement-enterprise-diagnostics-provider-admin.evtx | High | This event log covers MDM enrollment (including failure reasons) and other pertinent MDM activities. |
| microsoft-windows-devicemanagement-enterprise-diagnostics-provider-debug.evtx | Low | This event log is usually empty. |
| microsoft-windows-devicemanagement-enterprise-diagnostics-provider-operational.evtx | Low | This event log has lots of MDM-related activity in it, but I’ve never found any of it to be of any value. |
| microsoft-windows-moderndeployment-diagnostics-provider-autopilot.evtx | High | This is the key event log used by Autopilot, and one that you’ll almost always want to look at. |
| microsoft-windows-moderndeployment-diagnostics-provider-managementservice.evtx | Low | This event log has some Autopilot-related activity in it, but this is more “housekeeping” stuff that isn’t typically useful. |
| microsoft-windows-provisioning-diagnostics-provider-admin.evtx | Low | This event log contains events related to the application of provisioning packages (PPKGs), which are used to configure some Windows default settings. Typically you can ignore this one. |
| microsoft-windows-shell-core-operational.evtx | Medium | This is the event log that the shell uses for most things, including tracking the OOBE process, registering apps when a user signs in, etc. |
| microsoft-windows-user device registration-admin.evtx | Medium | This event log shows details around Hello for Business and related configuration details. |
| setupact.log | Medium | If you are familiar with the logs created by Windows Setup, you’ll recognise this one. This logs all the stuff going on in OOBE, and can be useful for troubleshooting any OOBE weirdness. |
| TpmHliInfo_Output.txt | High | This log (which is created even when not specifying the TPM area) contains basic details about the TPM in the device: the manufacturer, the firmware level of that TPM, whether it has a required EK cert, etc. |