- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Use of Managed Open In in general apps
Use of Managed Open In in general apps
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 21 2021 05:49 PM
My company uses ios terminals as COPE (Corporate Owned, Personally Enabled).
Therefore, I want to use Managed Open In because I don't want the company information to be leaked to the outside.
If it is OutLookApp or OneDriveApp, I think that it can be controlled by the app protection policy, but will it be out of control for other apps?
For example, I would like to use the Managed Open In of the Google Drive app and Gmail app.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 22 2021 01:06 AM
Hello @_ShinyaKobayashi
As far as I know most of the supported applications have already been added to the App protection policy Public apps list (that includes non-Microsoft apps), meaning if the Google apps are not included there it most likely means that those applications cannot be controlled via Microsoft Endpoint Manager proprietary policies using "Intune App SDK".
So there is probably no good way to include Google apps using the same tools as Microsoft apps.
There is a list of supported apps listed here: Supported Microsoft Intune apps | Microsoft Docs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 22 2021 02:04 AM
Hello @Alo Press
Thank you for your response.
Are you talking about the attached part?
If so, the Google Drive App doesn't seem to support it.
I will think about future measures.
Regard
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 22 2021 03:05 AM
@_ShinyaKobayashi Yeah, exactly!
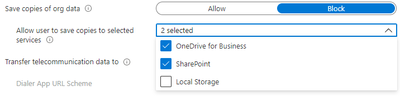
One way to work around that is to set "Save copies of org data" to Allow or
add the Local Storage option to "Allow user to save copies to selected services"
This does pretty much break the DLP logic but might "solve" your immediate problem of missing access to Google Drive.
Reference to config information: iOS/iPadOS app protection policy settings