- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Problem with Conditional Access rule Use app-enforced Restrictions for browser access.
Problem with Conditional Access rule Use app-enforced Restrictions for browser access.
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 26 2020 06:45 AM - edited Mar 26 2020 06:46 AM
- Labels:
-
Conditional Access
-
Intune
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:19 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:19 AM
Yes
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:21 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:31 AM
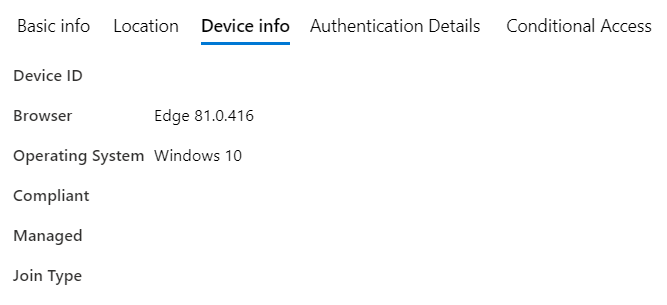
But when i look at the device, Hardware under Monitor and look at the Conditional Access properties i see this.
3/27/2020, 8:32:06 AM
Conditional access
Activation lock bypass code
Azure AD registered Yes
Compliance Compliant
EAS activated Yes
EAS activation ID ***********************
EAS activation time 16-12-2019 1:56:19 p.m.
Supervised No
Encrypted Yes
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:34 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:35 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:41 AM
If you run the command dsregcmd /status, you can find the deviceID.
Does this correspond with the device you have in Azure AD?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:48 AM
Yes i tested it on a other device and there works a expected.
The device id i got from dsregcmd is the same as in Azure.
I'd like to know why this partical device doesn't show the device info properly and how to fix it, whithout resetting the device. I have had two other devices with the same issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:51 AM
What does the 'device state' say?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:52 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:53 AM
EnterpriseJoined : x
AzureADJoined: x
...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:55 AM
+----------------------------------------------------------------------+
| Device State |
+----------------------------------------------------------------------+
AzureAdJoined : YES
EnterpriseJoined : NO
DomainJoined : NO
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 01:56 AM
If you try using the 'old' Edge or IE, does it report back then?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 02:07 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 03:51 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 03:52 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 04:10 AM
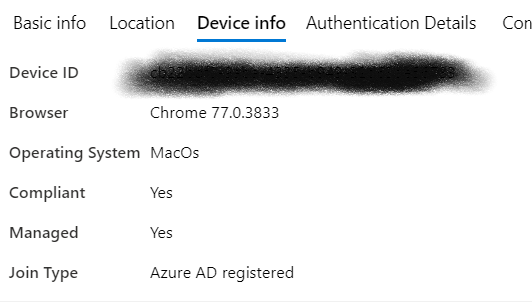
@RonaldvdMeer seems that something is wrong with the AAD registration as no Device ID is send and without that compliance status isn`t checked (and fails).
You should compare the outcome of dsregcmd /status as Thijs says, from a working Windows device with a none working. See if there is a difference which can point you in the right direction.
You can also try
dsregcmd /leave
dsregcmd /join
Restart the laptop and try again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020 04:32 AM
I will do that next Monday. I am working from home right now due to..... You know.
I will roll out a new device. See what happens.
I will get back to you next Monday
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 31 2020 01:18 AM
I did not see any difference between the dsregcmd status of a working device and the device that didn't work.
dsregcmd /leave did work
but dsregcmd /join didn't i got the message failed to complete task.
The only option left after that was a clean install of the device.
After complete rollout of the device the conditional access rules work as expected.
So problem is solved, although i am curious how this could have happened.