- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- How to restrict Unsupported browser
How to restrict Unsupported browser
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2022 06:31 AM
Hi,
We want to freeze them if any one use unsupported browsers on mobile devices. is this possible please suggest possible way?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2022 07:21 AM
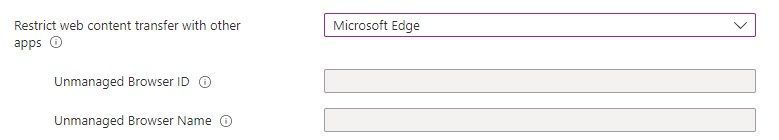
@Andy1192 I'm not sure what it is you want to achieve. What do you mean with "Freeze them"? If I had to guess, you are looking for a solution to restrict web content transfer from managed apps to unmanaged apps. Have a look at App Protection Policies. The links is for Android, but you can do the same for iOS. You can restrict web transfers to Edge, or an unmanaged browser.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 27 2022 01:58 AM - edited May 27 2022 02:00 AM
@Oktay Sari, I was thinking the same thing. @Andy1192 is probably looking for app protection, which would be the best solution. Other options crossed my mind, though.
For Android devices, you can block undesired apps completely, by assigning Managed Google Play app as "Uninstall". That's not possible on iOS, unfortunately.
For iOS devices you can list "restricted apps" in a compliance policy and then block access with conditional access if they are found.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 27 2022 04:18 AM
@Oktay Sari Hi thank you so much for your response. What we are looking any mobile device using an Unsupported version of the browser on a mobile device their access should not allow
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 27 2022 06:00 AM
Hi @Anandkumar you're welcome. There are a couple of options (not many) but the outcome depends on the device state. Some options will only work if the device is managed with Intune, others will also work for unmanaged devices. What is your scenario like?
Managed devices:
- Like @NielsScheffers mentioned, you can either use compliance policies for iOS or for Android devices by assigning the app as Uninstall.
- Conditional access policies (with Require approved client app) **
- Like I mentioned before, with an App protection Policies
- Microsoft Defender for Cloud Apps (requires extra licensing)
Unmanaged devices:
- MAM Policies (App protection Policy)
- Conditional access policies (with Require approved client app) **
Please note: The CA with require approved client app requires devices to be registered with AAD and a broker app. Furthermore, this method not only blocks unsupported browsers, but any app that is not on the approved apps list!
You can also configure the CA to require approved apps, AND/OR app protection policy. See this link for more info on that.
Hope this helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 30 2022 01:31 AM
@Andy1192, @Anandkumar did this help? If so would you be so kind to mark it as completed? If not, please let us know what your scenario is like and perhaps we can help you get going.
Thx! Oktay