- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Enroll W10 devices automatically using Group Policy
Enroll W10 devices automatically using Group Policy
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 18 2021 10:56 AM
Hi, I am testing W10 device auto-enrollment using GroupPolicy, following this article https://docs.microsoft.com/en-us/windows/client-management/mdm/enroll-a-windows-10-device-automatica...
Step number 7 in the article, we have tried to change the value to Enabled for Enable Automatic MDM enrollment using default Azure AD credentials group policy (Computer Configuration > Policies > Administrative Templates > Windows Components > MDM) by Group Policy but When we check the value in local Group Policy on the targeted devices, it always shows as Not Configured even after GPO was pushed successfully. We wondered what the registry for this policy is and it seems to be this one. \HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\CurrentVersion\MDM\ AutoEnrollMDM (article https://admx.help/?Category=Windows_10_2016&Policy=Microsoft.Policies.MDM::MDM_JoinMDM_DisplayName)
The value on all the targeted devices shows as 1 (enabled). Can I assume that the setting was changed successfully? The thing is, some of our devices were enrolled successfully but some weren't and we are trying to figure out where it's going wrong.
Many thanks in advance for your help
- Labels:
-
Intune
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 18 2021 11:52 PM
SolutionHello @GoodNightVienna!
I recommend that you use this command to view the policies applied to a device (run from local device):
- Start CMD/PowerShell as an admin
- Run: RSOP.msc
- Navigate to the specific location as per your need
As you are using Group Policies to enroll your devices I assume that you want your devices to be hybrid Azure AD-joined.
- Are you using Azure AD Connect to sync your devices to Azure AD?
- Are you synchronizing correct OU's in AD?
- Are all the failing devices Windows 10 or do you have any down-level devices (W7, W8, W8.1)?
I recommend below as part of your troubleshoot:
- Find a failing device in Azure AD and have a look at the "Registered" column. If you do not have a timestamp in the column, this would be your main issue which will mess up the MDM-enrollment as well.
- Have a look at this article to find more info about how you could troubleshoot the Azure AD Hybrid-Join issue: Troubleshooting hybrid Azure Active Directory joined devices | Microsoft Docs
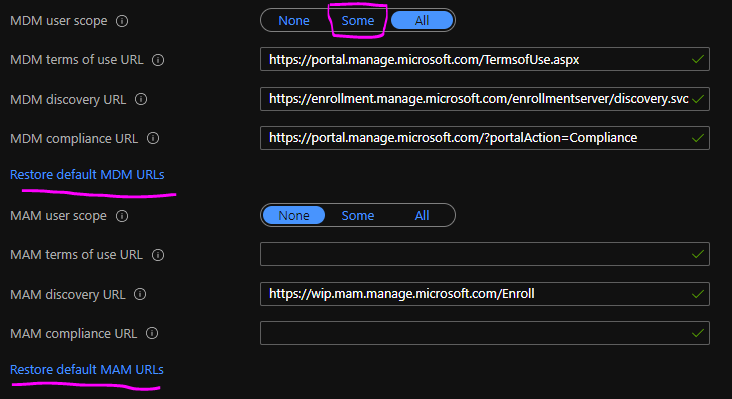
- Make sure that the MDM automatic enrollment settings are set correctly: Configure - Microsoft Azure
- Make sure that your end-users has an Intune license assigned
Have a look at above and let us know if you require further help. I am happy to help.
//Nicklas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 19 2021 05:29 AM
I would check the perquisites for devices not joined, like Windows version, Intune License, Event Viewer.
Check this guide:
https://allthingscloud.blog/automatically-mdm-enroll-windows-10-device-using-group-policy/
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 22 2021 03:04 AM
Hi @NicklasAhlberg!
Thank you very much for your reply. I ran the command mentioned in your reply and saw what I wanted to see! It is indeed ‘Enabled’ and I am happy![]()
I didn’t mention in my original post but I can confirm that
• Our test devices are hybrid Azure-AD joined (when we ran dsregcmd /status, under Device State, we can see AzureADJoined:Yes, DomainJoined:Yes)
• OUs are synced to Azure AD (my successfully enrolled laptop is in the same OU as the failing ones)
• All the test devices are W10 1909 or later
• EMS E3 licence is assigned to the test users
• Auto-enrollment is activated for those users who are going to enroll the devices into Intune
• Azure AD allows the logon user to enroll devices
• The MDM discovery URL during auto-enrollment is https://enrollment.manage.microsoft.com/enrollmentserver/discovery.svc
• Microsoft Intune allows enrollment of Windows devices (Enrollment restriction only applies on personal)
• Auto-enrollment settings are configured under Microsoft Intune
Error findings
Device 1
AzureAdPrt> No (however, KeySignTest= PASSED)
There are two entries in Azure portal> Devices
1. Join type= Azure AD registered, Registered 3/4/2020
2. Join type= Hybrid Azure AD joined, owner = N/A, Registered= Pending
Event viewer> ID76 Auto MDM Enroll: Device Credential (0x0), Failed (Unknown Win32 Error code: 0x8018002b)
Device 2
Join type= Hybrid Azure AD joined, owner = N/A, Registered 9/6/2019, Activity=3/15/2021
Event Viewer> ID76 Auto MDM Enroll: Device Credential (0x0), Failed (Unknown Win32 Error code: 0x8018002b)
Device 3
AzureAdPrt> No
No entry in Azure Portal> Devices. All other devices in the same OU appear in Azure AD as Hybrid Joined but not this one!
If you have any ideas to fix the issues above, I would really appreciate it. Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 22 2021 03:10 AM
Thank you for your suggestion. Most of the prerequisites are ok but there are a few errors. I put the details in my reply to NicklasAhlberg. Any ideas to fix those would be appreciated. Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 22 2021 03:18 AM
Hello!
- Click both "restore" buttons and make sure that the logged on users on the failing devices are part of the "some"/allowed group. This issue usually occur due to a combination of the users not being allowed to join devices to AAD and a faulty setup of Azure AD Connect.
- Windows 10-1803 did not consolidate device object when they went from registered to being join/hybrid joined. It is usually OK to delete the wrong device from AAD manually.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 31 2021 08:36 AM
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 18 2021 11:52 PM
SolutionHello @GoodNightVienna!
I recommend that you use this command to view the policies applied to a device (run from local device):
- Start CMD/PowerShell as an admin
- Run: RSOP.msc
- Navigate to the specific location as per your need
As you are using Group Policies to enroll your devices I assume that you want your devices to be hybrid Azure AD-joined.
- Are you using Azure AD Connect to sync your devices to Azure AD?
- Are you synchronizing correct OU's in AD?
- Are all the failing devices Windows 10 or do you have any down-level devices (W7, W8, W8.1)?
I recommend below as part of your troubleshoot:
- Find a failing device in Azure AD and have a look at the "Registered" column. If you do not have a timestamp in the column, this would be your main issue which will mess up the MDM-enrollment as well.
- Have a look at this article to find more info about how you could troubleshoot the Azure AD Hybrid-Join issue: Troubleshooting hybrid Azure Active Directory joined devices | Microsoft Docs
- Make sure that the MDM automatic enrollment settings are set correctly: Configure - Microsoft Azure
- Make sure that your end-users has an Intune license assigned
Have a look at above and let us know if you require further help. I am happy to help.
//Nicklas