- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Enable 'Require domain users to elevate when setting a network's location'
Enable 'Require domain users to elevate when setting a network's location'
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 01 2021 05:07 AM
Hi
From the security recommendations on my test machine I can see that it recommends me to
"Enable 'Require domain users to elevate when setting a network's location'"
First I tried creating a device configuration using settings catalog and administrative templates
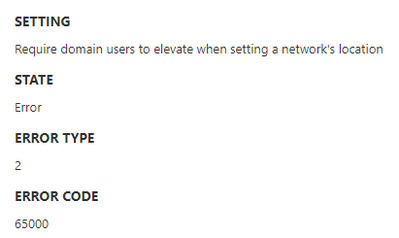
Then I got an error: Error type 2: Error code: 65000
So I checked the device and saw that the registry key was missing and created a proactive remediation script that creates the missing registry key on the device.
But I still have the same error, and the security recommendations still shows me to activate it. Not sure what I can do as none of the recommended solution actually make the security recommendation go away and they Administrative templates always errors out.
Option 1 - Set the following Group Policy:
Computer Configuration\Policies\Administrative Templates\Network\Network Connections\Require domain users to elevate when setting a network's location
To the following value: Enabled
Option 2 - Set the following registry value:
HKLM\SOFTWARE\Policies\Microsoft\Windows\Network Connections\NC_StdDomainUserSetLocation
To the following REG_DWORD value: 1
- Labels:
-
Intune
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 01 2021 05:32 AM
@JimmyWork There was a similar post on Tech Community last month, does this offer any help?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 01 2021 06:34 AM - edited Sep 01 2021 07:55 AM
Thank you for answering.
The error code is the same but this is an old registry file and it is available in the Feeds.admx on the computer.
Running Windows 10 Enterprise 21H1.
If I create this as a single administrative template instead of a catalog settings I get Not Applicable.
Creating the registry file also does not correspond to the security recommendations as they still report the settings is not turned on after multiple days.
When checking the logs on the computer I can see the following.
MDM ConfigurationManager: Command failure status. Configuration Source ID: (XXXXXXXXXXXXXXXXXXX), Enrollment Name: (MDMDeviceWithAAD), Provider Name: (Policy), Command Type: (Add: from Replace or Add), CSP URI: (./Device/Vendor/MSFT/Policy/Config/ADMX_NetworkConnections/NC_StdDomainUserSetLocation), Result: (The system cannot find the file specified.).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 02 2021 11:57 PM
Short update
If I manually activate the GPO on the local computer then everything works.
When activating the GPO locally it creates the same registry file I create manually but it will still give the same error when using settings catalog device configuration or admin templates device configuration.
I have made a ticket with Microsoft regarding this because something is of, the file is there I can enable it manually but it's still errors out in device configuration etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 07 2021 01:49 AM
SolutionThis is now solved.
The device needs to be in the Windows 10 insider channel for this settings to be applied.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 07 2021 01:49 AM
SolutionThis is now solved.
The device needs to be in the Windows 10 insider channel for this settings to be applied.