- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Enable RDP to take remote of Intune managed devices, Firewall blocking the connection
Enable RDP to take remote of Intune managed devices, Firewall blocking the connection
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Dec 08 2022 09:13 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 08 2022 09:13 PM
Hello Experts,
I need to enable RDP to take remote of Intune managed devices, could you please suggest the best solution through Intune, looks like the firewall
blocking the connection.
- Labels:
-
Intune
-
Mobile Device Management (MDM)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 09 2022 07:21 AM - edited Dec 09 2022 07:23 AM
Hey !@Deleted
We have the same issue and we are working on it, if we find something, we'll share with you !
For now, here's the procedure we are trying :
https://www.prajwaldesai.com/disable-remote-desktop-access-using-intune/ "Do it for enable it"
https://www.reddit.com/r/Intune/comments/vy69k8/enable_remote_desktop/
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 09 2022 08:15 PM
Hi @Deleted
Have you tried using Intune - EndPoint Security - Firewall - Create New Policy - Windows 11 - Microsoft Defender Firewall Rules
I have done the opposite recently (Locking Outbound Ports on Browsers), it worked like a treat.
Hope this helps!
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 09 2022 11:15 PM
I'm working with a customer to enable RDP on some AAD joined, Intune managed devices in the company. This is the configuration I'm testing at the moment:
- Enable RDP on device: Configuration Profile, Administrative template:
Allow users to connect remotely by using Remote Desktop Services - Enabled
Require user authentication for remote connections by using Network Level Authentication - Disabled
- Allow RDP/3389 through Windows Firewall: Device Configuration Profiles - Endpoint protection
Firewall rules - Allow TCP/3389
- Add users in local "Remote Desktop Users" group:
Endpoint security - Account protection - Local user group membership. Add users (not AAD groups) in "Remote Desktop Users" group.
There is a couple of drawback from this configuration.
- Managment - I dont want this configuration to all Windows clients in the company. An AAD groups with devices must be maintained.
- I my testing, adding AAD group in the Endpoint security - Account protection - Local user group membership policy is not working, only users can be added.
- All users added in the policy "Local user group membership", are added in the local group "Remote Desktop Users" on all devices assigned to this policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 12 2022 11:35 PM
@Moe_Kinani Could you please elaborate more on this/ if possible share all screenshots
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 13 2022 05:41 PM - edited Dec 13 2022 07:10 PM
Hi @Deleted
I was suggesting using the new Firewall Rules in Endpoint Security, located here. Create New Profile Windows 10/11 - Microsoft Defender Firewall Rule - Edit Rule - Then Apply the Settings below and test.
How did you confirm the issue from Windows firewall? Are your devices Azure AD Joined? Have you enabled the remote setting setting under Setting - System - Remote Desktop? I was prompted to enter creds without firewall policy as soon as I enabled the setting. You may need that setting only.
It will be great if you send us screenshot of the error you seeing.
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 29 2022 03:11 AM
I have created this configuration profile and it worked with me.
https://www.notbad.tech/all-things-it/intune/how-to-allow-rdp-port-3389-with-microsoft-defender-fire...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 02 2023 03:54 AM
@Deleted
I would suggest the following:
- Check the Firewall Rules in Intune. Particularly if you have any Security / Defender Baseline policies set. There is a setting called Policy rules from group policy not merged which I set to 'Not Configured' for the Private Firewall Profile
- Use the Scripts policy tool (or just do it manually) in Intune to deploy the following settings (PowerShell)
Set-NetFirewallRule -DisplayName "Remote Desktop - User Mode (TCP-In)" -Profile "Private"
Enable-NetFirewallRule -DisplayName "Remote Desktop - User Mode (TCP-In)"
- Check your network adaptor is using the Private Network Profile Type. (Settings > Network & Internet - Properties)
- Within Intune, create a Configuration Profile and enable the following settings:
- Allow users to connect remotely by using Remote Desktop Services
- Require user authentication for remote connections by using Network Level Authentication
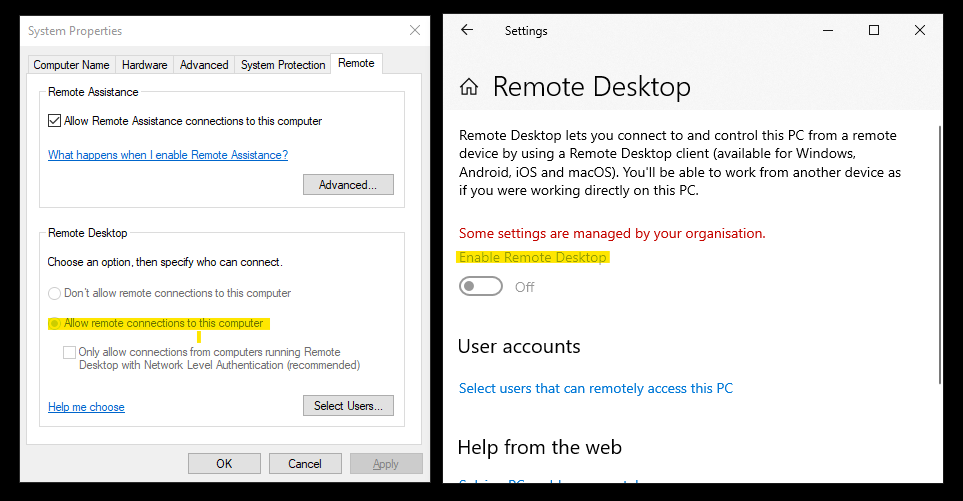
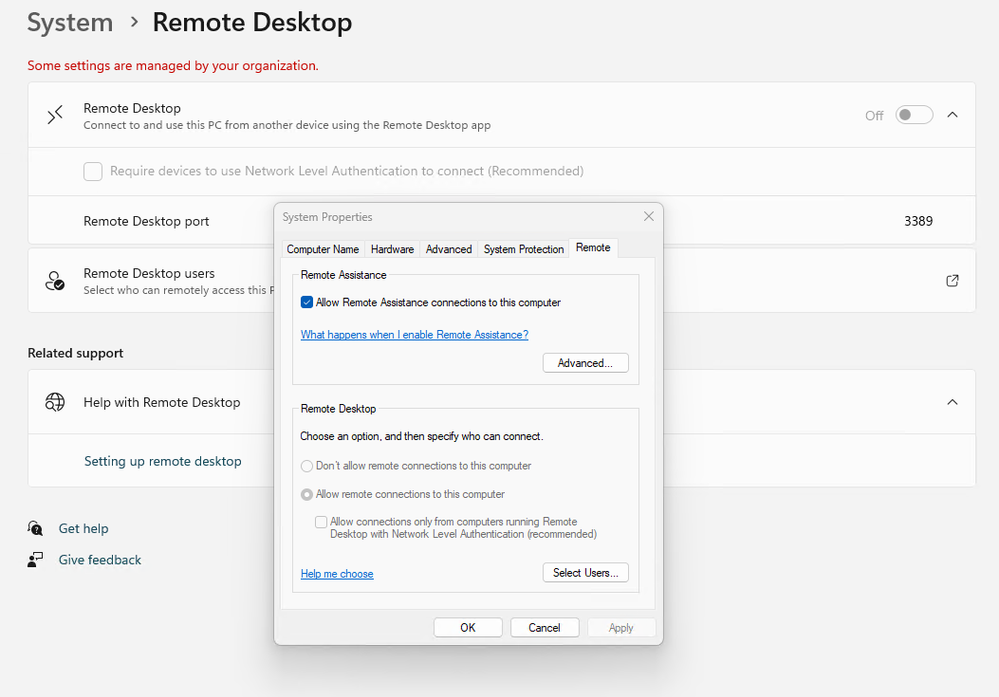
In the Windows 11 settings (System > Remote Desktop) it will show RDC as being OFF, but within The RDC options found in Control Panel, it will be turned on. Who knows what's going on here?
I believe that setting the Policy rules from group policy not merged to 'Not Configured' does open some doors in terms of security but I've had no luck using Intune FW rules.
I'd be interested if anyone has been able to do this recently with all the security baselines enabled.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 30 2023 06:27 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 30 2023 07:04 AM
Hey guys, we fixed our issue with the create of a new group to apply for a new Defender firewall policy accepted this : "The firewall allows RDP connection only with the private network or with the same domain via NTLMv2 authentication."
So need to turn on 2 profile through firewall as private network and domain accepting the outbound connection through NTLMv2 or your own config.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 19 2023 05:50 AM
I've been having issues with Intune and RDP for months so your comment about the differences between the "settings" app and sysdm.cpl interested me. Couldn't quite believe it when I saw it...
Schrödinger's RDP setting!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 26 2023 02:33 PM
I have the same issue; Settings - System shows it disabled, but it's enabled in sysdm.cpl anyone figure this out?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 27 2023 01:30 AM
I've been successfully using an AD GPO that enables remote desktop for years, but using Intune to configure the same setting ("Allow users to connect remotely by using Remote Desktop Services") doesn't work.
I used process viewer to do a deep-dive on the registry settings that were being modified when throwing these switches but I didn't conclude it yet.
My next step is to do a registry examination on an AD/GPO PC and compare it to the registry on an Intune PC. I'll post back if I find anything.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 27 2023 06:32 AM
You can enable or disable remote desktop access easily using a settings catalog policy. Please refer to this step-by-step guide for more info:
https://cloudinfra.net/enable-disable-remote-desktop-access-using-intune/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 27 2023 11:12 AM
@EtienneFiset - Thanks, we have updated the article to demonstrate the steps to enable or disable remote desktop connections using Intune - https://www.prajwaldesai.com/disable-remote-desktop-access-using-intune/