- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Disallow O365 access from 'outside' of the Android for Work work profile?
Disallow O365 access from 'outside' of the Android for Work work profile?
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 09 2017 10:49 PM
Is there a way to block Android for Work users to connect to Office 365 with apps that are installed outside of the work profile?
For example on my Android for Work capable device I have a work profile with eg. Outlook, which I can use to read my mail. However, i'm also able to use the Outlook app in my personal space to connect to Office 365, I was kinda expecting to only be able to connect to Office 365 from my work profile (?)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 09 2017 11:12 PM
https://docs.microsoft.com/en-us/intune/app-management
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 09 2017 11:40 PM
Yeah that's what I figured, but still I think its strange that you can't restrict access to O365 to just the work profile.
If I still need to have all kind of MAM policies, why would I still want/need Android for Work capability? It feels like AfW doesn't really add anything extra in regards of security....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 07 2019 01:52 PM
Hello@Joe Stocker
I have review this answer, and I would like to know if is this still valid or does now exist some way to achieve blocking access from non work profile apps to, for example, Outlook?
Thanks in advanced
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 20 2021 03:46 AM - edited Feb 20 2021 03:50 AM
it seems to make the separation of the work profile completely pointless if you cannot stop users from accessing company data from (the same) apps that they have installed in their personal profile.
We have a work profile setup, with outlook and the other office apps installed, which we can manage and wipe if needed, but there seems to be no way to prevent the user from also installing the same apps in the personal profile and then directly accessing the company data from those with, no way of controlling it (yes i know we could use MAM, but then why bother with the work profile at all)
The original post/reply is from some time ago now so I'm hoping Microsoft might have improved the situation since then with new options or policies etc to control this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 22 2021 07:46 AM
Hey i'm having the same issue
cant see the point working with "work profile" as long as the user can use the same app on personal profile . It makes no sense
365 must change that
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 22 2021 07:53 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2021 09:09 PM
@TonyKelly What configuration you have on the CA and Compliance policy to make that happen ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 01:11 AM - edited Jul 04 2021 02:38 AM
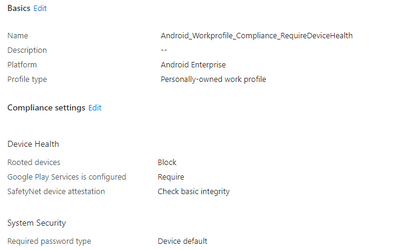
We normally create multiple compliance policies for each os etc. This one is an example of an android workprofile compliance policy
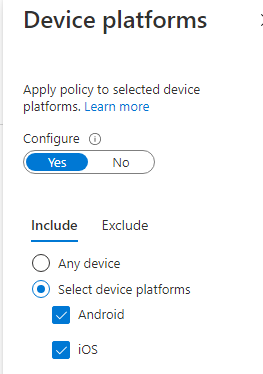
When this is configurede you could create an CA policy something like this
*Target the proper platforms:
*Target the client apps
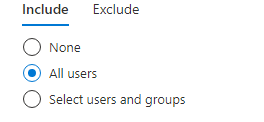
*Of course select the users :) and make sure you create an exclusion group for every ca policy you make
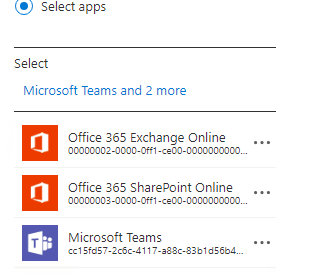
*Target the apps (or choose office 365)
*And to make sure to require compliant devices
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 01:46 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 01:56 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 02:04 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 03:25 AM
@Rudy_Ooms_MVP Hi Rudy, everything you say is correct for the device settings and limiting (legacy) client access. The question is about using the 'personal' and 'work' profiles in Android for Work/Android Enterprise, and limiting O365 access to the 'work' profile, there still doesn't seem to be a way to do that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 03:11 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2021 03:51 PM - edited Jul 04 2021 04:01 PM
The key is that compliance policies require enrollment of the device, so you create an enrollment restriction policy blocking non Android Enterprise devices this stops users from enrolling the personal profile so they can not receive a compliance policy which means they are never compliant on the personal profile.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 30 2022 05:49 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 26 2022 06:00 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 27 2022 03:15 AM - edited May 27 2022 03:47 AM
Hi @Avadhootfacctumcom, Try CA with Filter for devices. My setup is like this:
CA policy: block O365 outside workprofile
| Assignments | testuser@yourtenant.com | |
| Cloud apps or actions | Office 365 | |
Conditions: Device platforms | include: Android | |
Conditions: Filter for devices | Include filtered devices in policy | Rule syntax: device.operatingSystem -ne "AndroidForWork" |
| Grant | Block |
Filter for devices works a bit tricky: Specially the behavior with the different types of device states like: registered/unregistered/managed/unmanaged. I'm using an Include with negative operators here to make sure the policy does apply.
Please note: The OS type I'm targeting here is Not equals AndroidForWork. This means that every attempt made from other Android OS types (like AndroidEnterprise) will also be blocked. If you have other Android enrollment profiles, you will have to take that into account when you create your filter.
With this setup, I'm able to work with Outlook within the work profile, but it will block the sign-in when I try to add a work account outside the work profile. My sign-in logs confirm this behavior:
Try this with a test account and see if it works. If you only want to block Exchange Online, you could also choose "Office 365 Exchange Online" instead of "Office 365"
Oktay
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 27 2022 07:54 AM
@Oktay Sari thank you very much
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 28 2022 05:03 AM
i eventually got it to work (M'soft have changed things since i last tried), the company portal app is much better than it used to be)
Using a conditional access policy, for all cloud apps/or just 365, that required the device is enrolled AND using a known app (or app policy), along with an app policy too.
with that i couldn't use Outlook (or Teams or Onedrive or anything 365) in the personal profile :)